Exodus, a Government Malware that Infected Innocent Victims
Security researchers have found a new government spyware, tracked as Exodus, that was distributed through the Google Play Store.
A research conducted by members and associates of Security Without Borders organization along with Motherboard has revealed that government spyware that infected hundreds of people through the official Google Play Store.
The malware was tracked as Exodus, after the name of the command and control servers the malicious apps connected to.
The malware was undetected for months, and unfortunately, this isn’t the first time that malicious codes are hosted on the Google Play store without being detected.
This time, researchers discovered more than 20 malicious apps went unnoticed by Google over the course of roughly two years.
According to Motherboard, the Android surveillance malware on the Google Play store that was sold to the Italian government by a company that sells surveillance cameras. This company is not known to produce malware, and if confirmed this is the first surveillance software associated with it.
The researchers argue that the surveillance operation might have targeted also innocent victims because the spyware was poorly developed, a circumstance that is confirmed makes the software illegal.
“We identified previously unknown spyware apps being successfully uploaded on Google Play Store multiple times over the course of over two years. These apps would remain available on the Play Store for months and would eventually be re-uploaded.” reads the analysis published by the experts confirming that the malware was targeted for the Italian market.
“While details would vary, all of the identified copies of this spyware shared a similar disguise. In most cases they would be crafted to appear as applications distributed by unspecified mobile operators in Italy. Often the app description on the Play Store would reference some SMS messages the targets would supposedly receive leading them to the Play Store page. All of the Play Store pages we identified and all of the decoys of the apps themselves are written in Italian.”
The Exodus surveillance malware was hidden in look like harmless apps that propose promotions and marketing offers from local Italian cellphone providers, other apps involved in the campaign were designed to improve the device’s performance.

The experts shared their findings with Google earlier this year and the company quickly removed them and revealed that it has found a total of 25 different versions of the spyware since 2016.
Google said that less than 1,000 people were infected with malware, all Italian users.
Exodus is a two-stage malware, in the first stage, the malicious code infects the device and checks the phone number and the IMEI, likely to target specific users through a function called “CheckValidTarget.”
Experts pointed out that the checks implemented by the spyware don’t properly work, potentially infecting innocent victims.
“During our tests the spyware was upgraded to the second stage on our test device immediately after the first check-ins. This suggests that the operators of the Command & Control are not enforcing a validation of the targets. Additionally, during a period of several days, our infected test device was never remotely disinfected by the operators.” continues the report.
Then the Exodus malware steal sensitive data on the infected phone (i.e. audio recordings, phone calls, browsing history, calendar information, geolocation, Facebook Messenger logs, WhatsApp chats, and text messages, among other data, according to the researchers.
Experts discovered that the spyware also establishes a backdoor on the infected devices, it creates a shell and the port is open to anyone on the same Wi-Fi network as the target.
“If the mobile operator doesn’t enforce proper client isolation, it is possible that the infected devices are also exposed to the rest of the cellular network.” continues the analysis. “Obviously, this inevitably leaves the device open not only to further compromise but to data tampering as well.”
Experts at Security Without Borders indicated the Italian company eSurv, as the author of the malware. The company is located in the city of Catanzaro in the Calabria region, in the south of Italy.
Experts found two strings left by authors in the malware code: “mundizza,” and “RINO GATTUSO.” Mundizza is a dialectal word from the southern region of Calabria that means garbage, while Rino Gattuso is a popular Italian footballer from Calabria and current coach of the Milan football club.
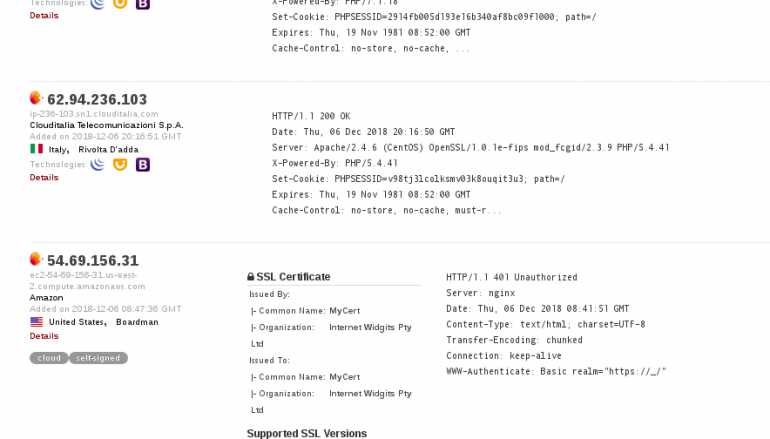
Researchers also found an overlapping infrastructure with eSurv Surveillance Cameras, the C2 server shares a TLS certificate with other servers that belong to eSurv’s surveillance camera service.
Other spyware samples communicate with a server belonging to eSurv, according to the researchers. Google confirmed the servers belong to eSurv. The Trail of Bits researcher who reviewed the technical report and the spyware confirmed that it’s linked to eSurv.

After we followed up and asked for clarification, the company declined to comment.
“eSurv won an Italian government State Police tender for the development of a “passive and active interception system,” according to a document published online in compliance with the Italian government spending transparency law. The document reveals that eSurv received a payment of EUR 307,439.90 on November 6, 2017.” reads the post published by Motherboard.
“We filed a freedom of information request to obtain information on the tender, the list of companies that participated, the technical offer sent by the company, and the invoices issued by eSurv. Our request, however, was rejected.”
Are you interested to know if such use of the Exodus spyware is legal in Italy?
Give a look at the excellent post written by Lorenzo Francesco Bicchierai.
This post Exodus, a Government Malware that Infected Innocent Victims originally appeared on Security Affairs.





