Critical infrastructure in Europe exposed to hackers
Power stations in Germany, Italy and Israeli smart building could be accessed by criminal hackers
Operators of critical infrastructure in Europe have left networks open to attack by hackers, according to investigations carried out by law enforcement officials.
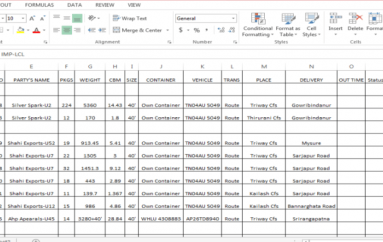
According to a report by German IT news publication Golem, Berlin Police’s Internet Wache, inquiries carried out over a couple of months found that researchers were able to access the control systems of waterworks, cogeneration units, interfaces for building automation and other industrial control system (ICS).
The researchers started the investigation after they discovered certain patterns in HTTP headers in these control systems and then programmed a Python script and used ZMap to find public IP addresses.
“Most could be read access without special authentication. Some systems even allowed access to controls, among which were German waterworks,” said the report.
“Attackers can not only capture important data critical systems, the systems are also vulnerable, and can be manipulated under certain circumstances, paralysed or even damaged. And not just the systems themselves are in danger, but also people or plants in their environment.”
The researchers said that in most cases the operators were unaware.
Among the vulnerable infrastructure were a district heating scheme in Rome, combined heat and power plants in Germany and Austria, and a smart building housing luxury apartments in Israel.
With the latter, hackers could disable lifts or alarm systems, and control air conditioning units.
The investigators found that with half of the systems they discovered, only half required some kind of authentication to gain access. Other problems found range from cross-site scripting errors and HTTP injection vulnerabilities. They alerted software vendors about software bugs in their software that allowed access and control.
Since the investigation, the researchers said that Germany’s BSI informed operators of these systems and stopped public access to systems. However, not all operators took their systems off the public internet immediately.
Nick Wilding, general manager of cyber-resilience at AXELOS, told SCMagazineUK.com that although continuing to invest in, deploy and manage complex technological control is essential, “critical infrastructure organisations must also ensure that all their employees, regardless of their role or status, exhibit good cyber-behaviours by providing them with the simple, practical guidance they need to identify threats before they are allowed to breach systems and impact corporate reputation.”
“Educating your workforce throughout the year must be a key part of any effective resilience strategy – our staff should be our most effective security control but they can be our greatest vulnerability if ‘effective’ learning is not provided.”
Matt Middleton-Leal, regional director, UK & I at CyberArk, told SCMagazineUK.com that attacks on Industrial Control Systems (ICS) certainly appear to be on the rise; the Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) has noted that 295 incidents were reported in the United States in 2015 alone.
“When it comes to the security of critical infrastructure, the potential for systems to be compromised is compounded by the avenues available to infiltrate the ICS,” he said.
“The inherent security vulnerabilities in these systems – such as the use of shared accounts with no individual oversight, the use of interactive remote user access, and network connections to the IT/Corporate environments – add to the security risks, as these access points provide an attack vector for malicious outsiders looking to infiltrate critical networks, escalate privileges, exfiltrate sensitive data or cause physical harm.”