IT Security
Artificial Intelligence in Cyber Security – Cyber Attacks and Defence Approach
Artificial Intelligence in Cyber Security is always evolving, say from the old school days when AV was thought to be
Xerosploit – Pentesting Toolkit to Perform MITM, Spoofing, DOS, Images Sniffing/Replacement, WD Attacks
Xerosploit is a penetration testing toolbox whose objective is to perform the man in the middle attacks. It brings different
Most Important Cyber Incident Response Tools List for Ethical Hackers and Penetration Testers
Cyber Incident Response Tools are more often used by security industries to test the vulnerabilities and provide an emergency incident
Top 5 Best Ways to Keep Your Data Center Safe and Secure
Everybody knows by now that Cloud technology has changed our lives. So much so that it isn’t even news anymore:
USBStealer – Password Hacking Tool For Windows Applications to Perform Windows Penetration Testing
USBStealer is a Windows Based Password Hacker Tool that helps to Extract the password from Windows-Based Applications such as Chrome
Perform Vulnerability Scanning in Your Network using Maltego
Maltego is an intelligence gathering tool, its available for windows, mac, and Linux. We will be using Kali Linux where
Free Email Security Penetration Testing Tool to Check Organization’s Security against Advanced Threats
BitDam launches a free Email Security Penetration Testing tool to determine the organization’s security posture against advanced threats. The Email
Most Important Web Server Penetration Testing Checklist
Web server pen testing performing under 3 major category which is identity, Analyse, Report Vulnerabilities such as authentication weakness, configuration
WPScan – Penetration Testing Tool to Find The Security Vulnerabilities in Your WordPress Websites
WPScan is a WordPress security scan for detecting and reporting WordPress vulnerabilities. WordPress is a free online Open source content
FileTSAR – A Free All-In-One Forensic Toolkit for Law Enforcement Agencies
FileTSAR, a free open source tool that combines various open source forensic investigation tools used by law enforcement agencies. The
Cynet Offers a Free Threat Assessment for Mid-Sized and Large Organizations – Take a Free Ride Now
Visibility into an environment attack surface is the fundamental cornerstone to sound security decision making. However, the standard process of
DDoS Attack Prevention Method on Your Enterprise’s Systems – A Detailed Report
A distributed denial-of-service (DDoS) attack aims to exhaust the resources of a network, application or service so that genuine users
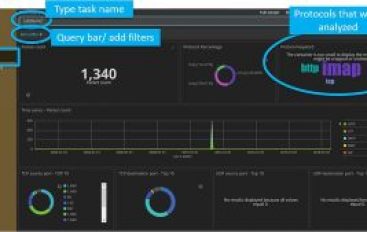
SPARTA – Network Penetration Testing GUI Toolkit
SPARTA is GUI application developed with python and inbuild Network Penetration Testing Kali Linux tool. It simplifies scanning and enumeration
Microsoft ‘s New Tamper Protection in Defender ATP Lets block never-before seen Malware within Seconds
Microsoft released a new future called Tamper protection in Microsoft Defender ATP to provide next-gen security to their users and
85 Percent Of Organizations Fail To Meet Basic Level Of PAM Maturity
Thycotic’s 2019 State of Privileged Access Management Maturity Report Reveals Alarming Shortcomings in PAM Security Practices Thycotic, a provider of
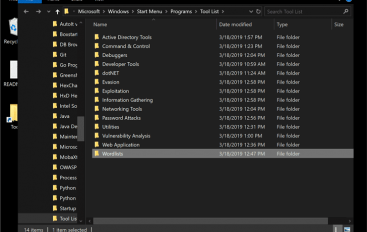
Commando VM – Using Windows for Pen Testing and Red Teaming
FireEye released Commando VM, a Windows-based security distribution designed for penetration testers that intend to use the Microsoft OS. FireEye