Archive
Insight Venture Partners has agreed to acquire a controlling interest in Recorded Future, a threat intelligence company, in addition to the minority stake it already owns. The all-cash transaction puts the value of Recorded Future at more than $780 million.
Organizations are not equipping themselves against privileged access management (PAM) abuse, according to a report by Centrify and Techvangelism. Nearly 80% of organizations were found not to have a mature approach to combating PAM cyber-attacks, yet 93% of the organizations
The WordPress plugin Convert Plus is affected by a critical flaw that could be exploited by an unauthenticated attacker to create accounts with administrator privileges. The WordPress plugin Convert Plus is affected by a critical vulnerability that could be exploited
Report: 50% Increase in Exposed Data in One Year
New research released by digital risk protection specialists Digital Shadows has revealed a 50% increase in exposed data in the last year. In its report Too Much Information: The Sequel from its Photon Research Team, Digital Shadows discovered that misconfiguration
Data protection monetary penalties have increased by GBP2m in the past year, while the number of enforcements issued fell by more than 20 from the number issued in 2017. According to PwC‘s 2018 Privacy & Security Enforcement Tracker, monetary penalties
Chinese Cyber-Spies Target Government Organizations in Middle East Chinese APT group Emissary Panda has been targeting government organizations in two different countries in the Middle East. Experts at Palo Alto Networks reported that the Chinese APT group Emissary Panda (aka
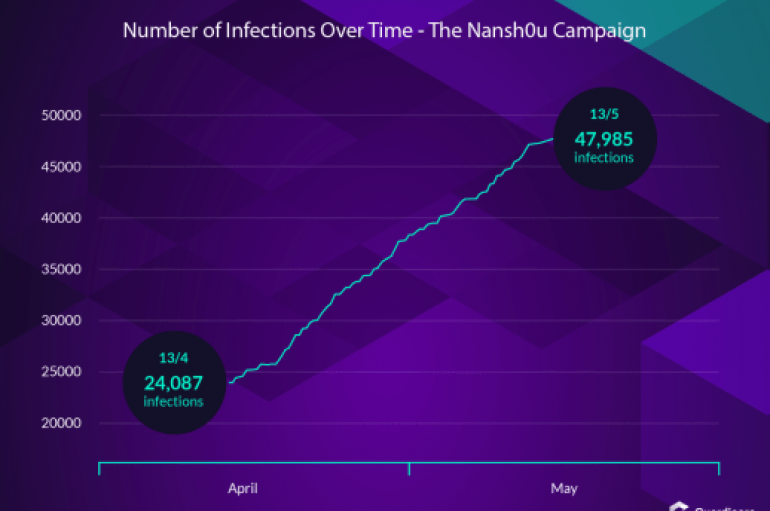
Guardicore Labs uncovered a widespread cryptojacking campaign tracked as Nansh0u and aimed at Windows MS-SQL and PHPMyAdmin servers. Security experts at Guardicore Labs uncovered a widespread cryptojacking campaign leveraging a malware dubbed Nansh0u. The malicious code aimed at Windows MS-SQL
Cybercriminals from APT-27 group targetting the high profile enterprise networks by exploiting MySQL server through malware such as NewCoreRAT(Remote Access Trojan) linked with Chinese APT Campaign. Most of the enterprise networks relay with a cloud platform to store their sensitive
Mimecast has released its third annual State of Email Security Report and has found that phishing attacks have lost companies money, data and customers. Including insights from 1,025 global IT decision-makers, the report found that social engineering attacks were on
Public Wi-Fi is easily accessible by everyone, as much as free surfing sounds cool, it is risky as well. Let’s see how your data can be hacked easily. In the contemporary world of networking, Wi-Fi has become a vital commodity.
Nearly one million PCs on the public internet are still vulnerable to wormable, BlueKeep RDP flaw. Even-though Microsoft fixed the vulnerability on May 14, 950,000 unpatched devices are still running with the older Windows operating systems. We have reported about
A race condition flaw that could be exploited by an attacker to read and write any file on the host system affects any versions of Docker. Experts found a race condition vulnerability in any versions of Docker, the vulnerability could
Flipboard Breached in Nine-Month Raid
Flipboard has reset all customer passwords as a precaution after revealing that hackers had unauthorized access to user data for over nine months. The news aggregator site, which has around 150 million monthly users, said the “unauthorized person” gained access
The Laptop loaded with six most dangerous pieces of malware was sold at an auction. The malware present in the Laptop is responsible for causing financial damages totaling $95 billion. It is the most dangerous machine right now in the
Researchers discovered a new wave of Mirai Variant that used 13 different exploits to attack various router models and other network devices. These exploits are associated with this new Mirai variant capable of launching backdoor and distributed denial-of-service (DDoS) attacks.
Experts at IBM X-Force observed a new campaign involving the HawkEye keylogger in April and May 2019 aimed at business users. Malware attacks leveraging a new variant of the HawkEye keylogger have been observed by experts at Talos. The malware