Posts From CCME
A device’s network security key is a password or pass-phrase used to authenticate with a local area network (LAN). The typical modern LAN includes computers, mobile devices, smart TVs and more. The network key must be provided by any device
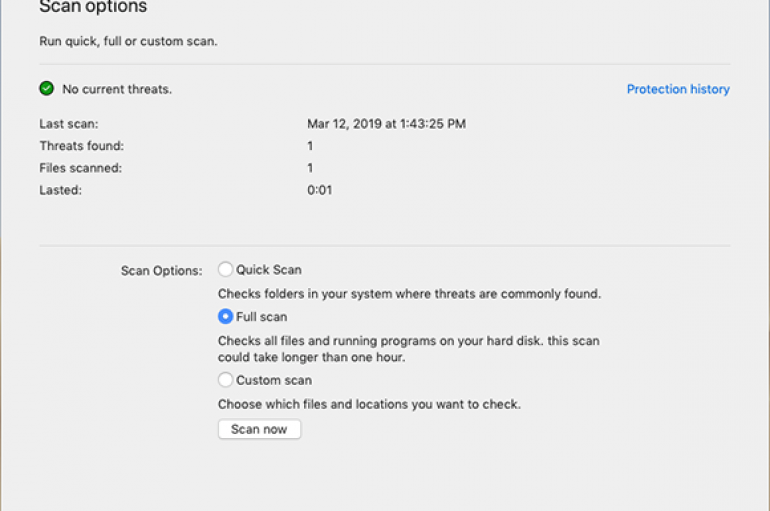
Microsoft Defender APT now protects also macOS
Microsoft has announced the availability of Microsoft 365 advanced endpoint security solution across platforms, with the support of Apple Mac it added to Microsoft Defender Advanced Threat Protection (ATP). Microsoft Windows Defender ATP was first introduced in 2016 as a
Nmap – Penetration Testing Tool to Perform Information Gathering – A Detailed Explanation
nmap is an open source network monitoring and port scanning tool to find the hosts and services in the computer by sending the packets to the target host for network discovery and security auditing. Numerous frameworks and system admins additionally
Firefox 66.0.1 Released with Fix for Critical Security Vulnerabilities that discovered via Trend Micro’s Zero Day Initiative. The vulnerability affects all the versions of Firefox below 66.0.1. An attacker could exploit these vulnerabilities to take complete control over the target
AZORult Malware Abusing RDP Protocol To Steal the Data by Establish a Remote Desktop Connection
Sophisticated AZORult Malware emerges in a new form with advanced information stealing modules that capable of stealing sensitive information from infected computers. AZORult is one of the well-known malware that often sold in Russian forums for the higher price ($100)
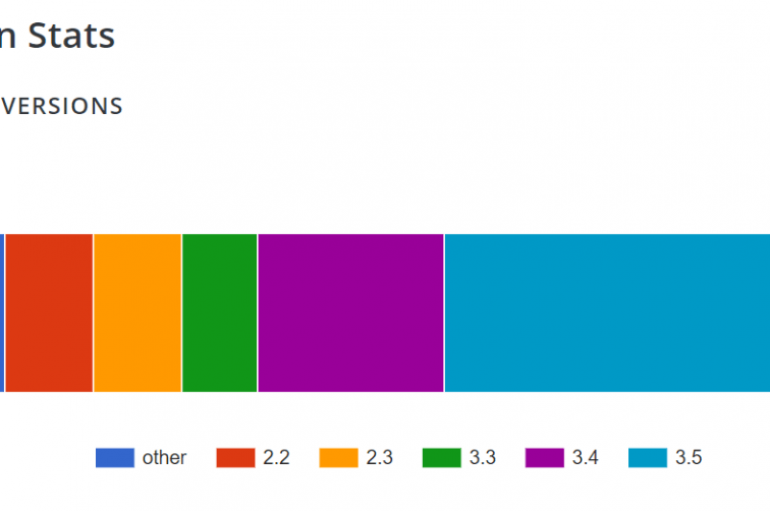
A Cross-Site Scripting (XSS) vulnerability in Social Warfare installations (v3.5.1 and v3.5.2) is actively exploited to add malicious redirects. The vulnerability in the WordPress plugin has been fixed with the release of the 3.5.3 version of the plugin. PSA: The
The Federal Emergency Management Agency’s (FEMA) has disclosed a data leak that exposed banking details and other personal information of 2.3 million survivors. In case of national disasters, the Federal Emergency Management Agency’s (FEMA) offers a program called Transitional Sheltering
Domain Name System or DNS is one of the foundational elements of the entire internet; however, unless you specialize in networking, you probably don’t realize how important it is. DNS is essentially like a phone book of numbers that computers
Organized Cybercrime – Hacker Groups Work Together To Distribute Banking Malware Globally
The banking malware considered a top threat, it allows a malware developer an easy way to gain access to someone and cause serious damage. According to the reports, the cybercrime costs more than $600 billion in 2017 and for 2018
New Variant of AZORult Trojan Written in C++
After analyzing several previously unknown malicious files that were detected earlier this month, Kaspersky Lab determined the files were a new version of a data stealer known as the AZORult Trojan. Because the files are written in C++, and not
Virtualized Calls a Top Threat for ATO Attacks
According to the 2019 State of the Call Center Authentication report from TRUSTID, a Neustar company, one of the most exploited areas in a company’s security chain is the call center. Companies may be investing more in their cybersecurity defenses,
The U.S. Department of Homeland Security Thursday issued a security advisory for multiple vulnerabilities affecting over a dozen heart defibrillators. Multiple vulnerabilities in the heart defibrillators could be exploited by attackers to remotely control the devices, potentially putting the lives
Sophisticated threats are Evolving with much more advanced capabilities and giving more pain for analysis even evade the advanced security software such as Antivirus. This comparison is made by the payload ability to bypass the default security frameworks accessible on
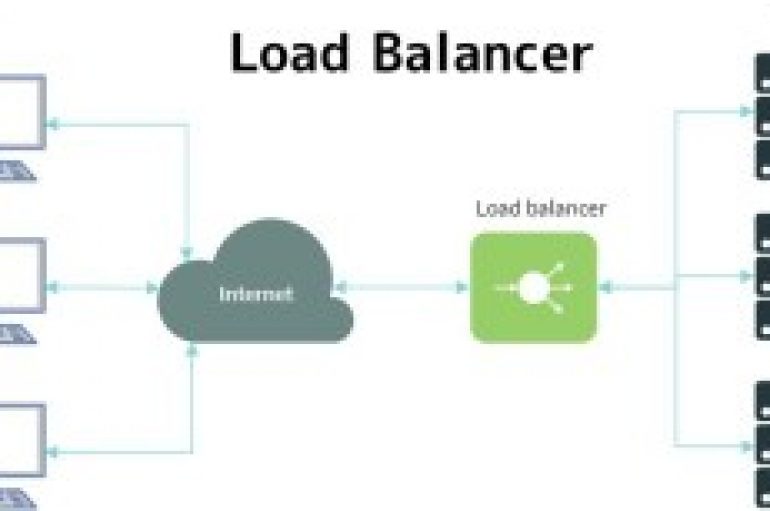
Load Balancer basically helps to distribute the network traffic across the multiple servers to improve the network, application performance. the Reconnaissance work on target to find out target domain has a load balancer so that penetration testing does not misdirect
Researchers discovered a critical Stored XSS Zero-day flaw in widely used social sharing plug-in called “Social Warfare” let attackers inject the malicious script and take over the vulnerable WordPress websites. Social Warfare, a social sharing plugin for WordPress powered by
News problems for Facebook that admitted to have stored the passwords of hundreds of millions of users in plain text. Facebook revealed to have stored the passwords of hundreds of millions of users in plain text, including passwords of Facebook