Posts From CCME
An individual or group of hackers have managed to amass over $54m in stolen digital currency by raiding digital wallets improperly secured with private keys, according to a new report. Consultancy Independent Security Evaluators (ISE) claimed the “Blockchainbandit” had taken
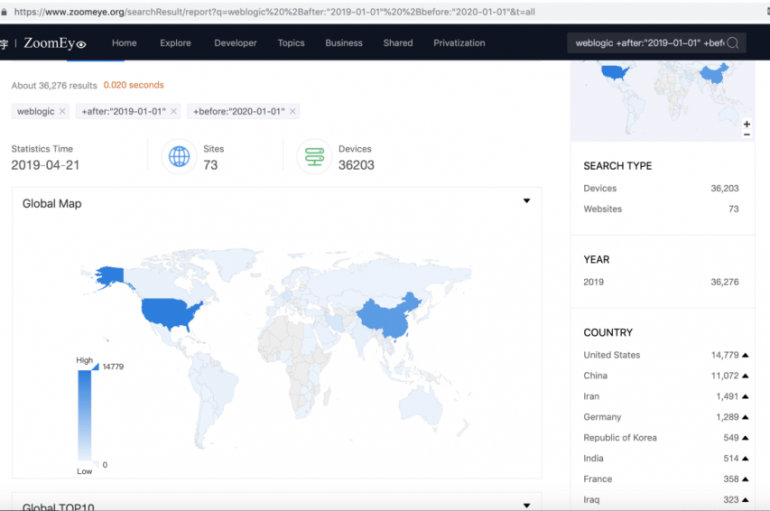
Zero-Day Vulnerability in Oracle WebLogic
Security experts are warning of a dangerous zero-day remote code vulnerability that affects the Oracle WebLogic service platform. Oracle WebLogic wls9_async and wls-wsat components are affected by a deserialization remote command execution zero-day vulnerability. New Oracle #WebLogic #RCE #Deserialization 0-day
Hackers Using Weaponized TeamViewer to Attack & Gain Full Control of the Government Networks
Researchers spotted a new wave of cyber attack from Russian speaking hacker who uses the weaponized TeamViewer to compromise and gain the full control of the Government network systems. Teamviewer is the most popular tool used for remote Desktop control,
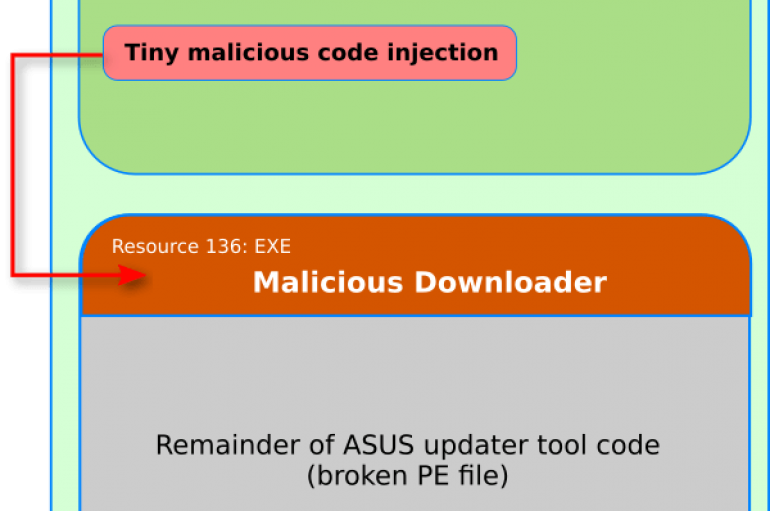
Experts at Kaspersky Lab linked the recent supply-chain attack targeted ASUS users to the “ShadowPad” threat actor and the CCleaner incident. Security researchers at Kaspersky Lab linked the recent supply-chain attack that hit ASUS users (tracked as Operation ShadowHammer) to
Magecart Swoops in to Strike Atlanta Hawks Shop
The online shop for the Atlanta Hawks currently states that it is temporarily down for maintenance, and according to Sanguine Security, the ecommerce site is the latest victim of a Magecart attack. In the wild, hawks hold their place at
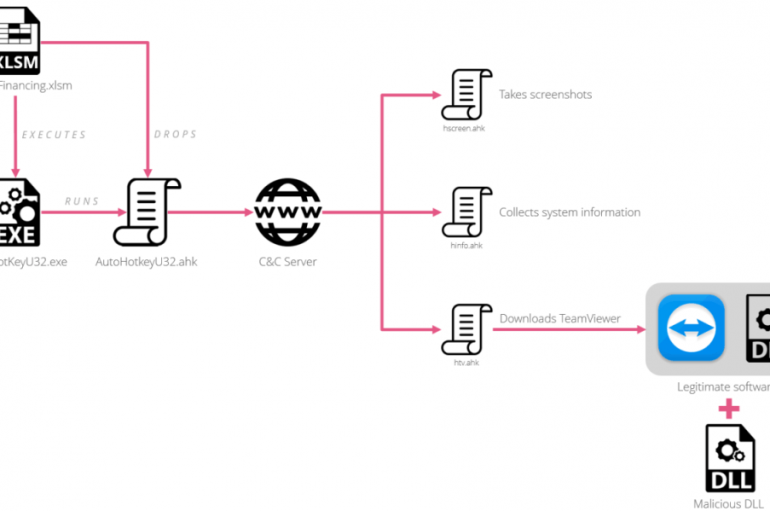
New Malware attack campaign dubbed “Aggah” targeting various countries via weaponized Word documents and infect the victims by dropping the available RevengeRAT from Pastebin. Researchers from Palo Alto recently observed the largest malware campaign via telemetry and they named as
A Wi-Fi hotspot app exposed more than two million Wi-Fi network passwords from its unprotected database. The app named WiFi Finder, downloaded by thousands of users to locate and connect with Wi-Fi hotspots, the app also stores Wi-Fi password and
CheckPoint firm uncovered a cyber espionage campaign leveraging a weaponized version of TeamViewer to target officials in several embassies in Europe. Security experts at CheckPoint uncovered a cyber espionage campaign leveraging a weaponized version of TeamViewer and malware disguised as
Bad news for fitness and bodybuilding passionates, the popular online retailer Bodybuilding.com announced that hackers have broken into its systems. The popular online retailer website Bodybuilding.com announced last week that hackers have broken into its systems. The website offers any
Cyber Readiness Worsens as Attacks Soar
The number of organizations in Europe and the US that have been hit by a cyber-attack over the past year has soared to over three-fifths (61%), according to a new report from Hiscox. The global insurer today released the results
A large trove of personally identifiable information (PII) has been leaked by an addiction treatment center after researchers found another unsecured Elasticsearch database online. Justin Paine, who is also a director of trust and safety at Cloudflare, blogged about his
Most Important Key Factors Organizations Should Consider in Implementing the Cloud Security Solutions
Cloud Security Solutions is one of the challenging tasks while performing the cloud migration for any organization and they need to ensure the best adaptable and equipped solution to handle the wider range of cyber attacks. Increasing the number organization
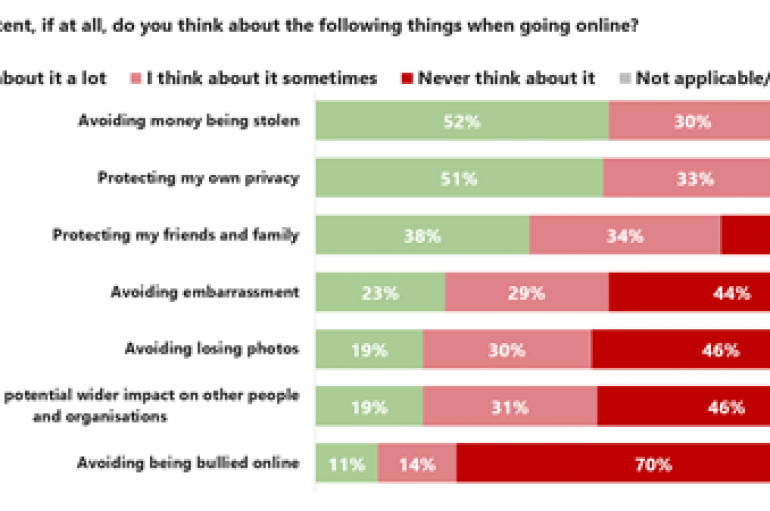
The National Cyber Security Centre (NCSC) expects 42% of Britain online users to lose money due to fraud, according to its first UK Cyber Survey. Released over the Easter weekend (April 21, 2019), the report also found that the most-used
Google to Block Logins From Embedded Browser Frameworks to Protect From Phishing & MitM Attacks
Google announced a new security update to block users sign-in using Embedded browser frameworks in order to improve the protection against Phishing and MitM attacks. Jonathan Skelker, Product Manager and Account Security at Google said, “Form of phishing, known as
Palo Alto Networks Unit 42 researchers uncovered a malicious campaign targeting entities in North America, Europe, Asia, and the Middle East with RevengeRAT. The campaign was carried out during March, threat actors tracked as Aggah” used pages hosted on Bit.ly,
Cybercriminals posted a new service called Inpivx, which provides a management dashboard for its customers to manage and to develop the malware from scratch. The new straightforward service allows anyone with average computer skill can create ransomware with all file