ZDI Paid Out $2 Million for Vulnerabilities in 2016
Trend Micro’s Zero Day Initiative (ZDI) published 674 advisories last year and paid out nearly $2 million to researchers who submitted vulnerabilities, the company said in its “2016 Retrospective” report.
ZDI encourages responsible disclosure through financial rewards, but the company does not resell or redistribute the vulnerabilities it acquires, and instead uses the information to protect TippingPoint customers against potential attacks even before a patch is made available.
Of the total number of advisories, 54 described vulnerabilities that had not been patched at the time of disclosure, while the rest were successfully coordinated with the affected vendor. Researchers reported many flaws last year, but almost 43 percent of them were rejected by ZDI.
The most interesting vulnerabilities reported through ZDI in 2016 affected Internet Explorer (CVE-2016-3382), Edge (CVE-2016-0158), Windows (CVE-2016-7272), OS X (CVE-2016-1806), Flash Player (CVE-2016-7857) and Chrome (CVE-2016-5161). CVE-2016-1806 was disclosed at the company’s Pwn2Own competition.
Several researchers stood out last year, including kdot (30 advisories), bee13oy (18 advisories), rgod (15 advisories) and Steven Seeley (20 advisories). These experts have tens of other advisories lined up for public release as soon as vendors address the flaws. Twelve percent of the published advisories are the work of ZDI’s own employees.
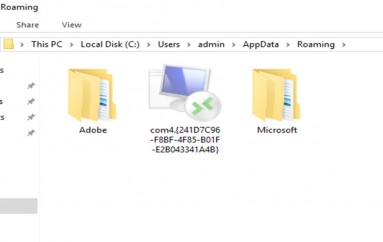
Of the 674 advisories made public last year, 149 covered vulnerabilities affecting Adobe products, representing 22 percent of the total. It’s worth noting that the November Patch Tuesday updates released by Adobe for Flash Player addressed nine flaws, all reported to the software giant via ZDI.
Surprisingly, the vendor with the second largest number of advisories, 112, is industrial automation solutions provider Advantech. Microsoft, Apple, Foxit, Oracle, Solarwinds, Trend Micro, HPE and Google also made the top 10.
Source | securityweek