Use a Malware Simulator to Better Defend Against Ransomware
If you are looking for ways to run a malware simulator to test ransomware and other forms of malware in your environment, but don’t want to deal with the actual materials to infect your systems, look no further than the Shinosec ShinoLocker suite. This is a malware simulator and target attacking suite for penetration testers and other researchers.
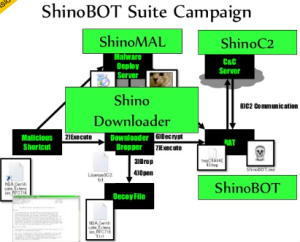
The new version includes new features and components, such as a remote access Trojan simulator, a malware delivery server, a command-and-control server and a dropper.
Ransomware Without the Ransom
The idea is to test your security and protection products against the kinds of attacks that a typical piece of ransomware would conduct. ShinoLocker behaves just like a real ransomware attack, but with one important difference: It does not ask for any actual ransom money in exchange for decryption keys.
The suite was born at the 2013 Black Hat conference with a presentation by security researcher Shota Shinogi. Since then, he has augmented its features with additional tools. Everything is controlled via a web interface, making it easy to set up and configure.
Shinogi created this ransomware to help other researchers understand how malware works. The suite allows researchers to test their forensics skills by attempting to retrieve the decryption key from memory. However, the key can be easily retrieved if the tester is stuck.
A Quick, Easy, Transparent Malware Simulator
In the past, trying to run a malware simulator required advanced skill and too much time to set it up properly. Shinosec makes this process more transparent. It even includes an encrypted Trojan hidden inside an image file.
Penetration testers often struggle to create a sufficiently valid malware simulator. There have been other, mostly academic, projects in the past, and at least two similar tools — FakeNet and MAST — have been developed. But Shinosec is still one of the most complete toolsets available, and at no cost to boot.
Educational Value Outweighs Risk
Could a real attacker abuse this suite and easily create active malware that could damage systems? That is possible, although it would take some work to disguise the Shinosec signatures. Still, the educational value far outweighs the risk. The suite helps defenders better understand and prevent future malware attacks.
Source | securityintelligence