Malware-as-a-Service – Adwind Malware Attack Utilities Industry Via Weaponized PDF File
Researchers discovered a new wave of a phishing campaign that bypassing the Microsoft APT protection and delivery the Adwind malware via weaponized PDF file to attack utilities Industry network.
Adwind, a.k.a Unrecom, Sockrat, JSocket, and jRat is a cross-platform RAT that distributed via malware-as-a-service in underground markets where users can purchase and utilize to target victims.
Between 2013 to 2018, Adwind malware roughly affected more than half a million users around the globe, and deployed in various industries such as Manufacturing, Finance, Engineering, Government, Telecom, Software and more.
In some of the previous attack, Adwind utilizing the DDE code injection to infection the cross platforms and it was equipped with spyware capabilities to steal data from victims and reporting back to the malware authors via command & control server.
Previous version Adwind Widely spreading via A360 Cloud Drive Platform Abuse for Delivering Remote Access Trojans and used as a Malware Distributing Platform by using a File-sharing site to host Malware.
Another scenario Cross-platform Remote Access Trojan “Adwind” Steal Credentials, Record and Harvest keystrokes the Aerospace Industries Data.
Initial Stage of infection starts by distributing a phishing campaign with an attached malicious PDF file that is capable of bypassing the Microsoft APT protection.
Attackers utilizing the hijacked accounts to delivery the phishing emails and also an attacker abusing the domain to host the malware.
Email body posed as a legal document and asked users to sign and return, is the was attacker trick users to click on the attached PDF file and open it.

According to Cofense report, “At the top of the email is an embedded image which is meant to look like a PDF file attachment, however, is in fact a jpg file with an embedded hyperlink. When victims click on the attachment, they are brought to the infection URL hxxps://fletcherspecs[.]co[.]uk/ where the initial payload is downloaded.”
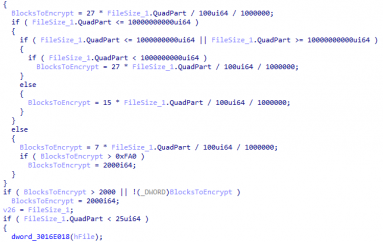
Initial payload named as “Scan050819.pdf_obf.jar.” here, attackers using obfuscation technique to make this file looks like a legitimate PDF and its create a two different .class file.
Malware author utilising the takskill.exe to disable popular analysis tools and antivirus software to evade the detection.
Adwind is developed with so many interesting features including,
- Takes screenshots
- Harvests credentials from Chrome, IE and Edge
- Accesses the webcam, record video and take photos
- Records audio from the microphone
- Transfers files
- Collects general system and user information
- Steals VPN certificates
- Serves as a Key Logger
In the end, Adwind store all the harvested data in the specific location of the system “C:UsersByteAppDataLocalTemp.” and share it to the attacker by establish a connection with Command & control server.
This post Malware-as-a-Service – Adwind Malware Attack Utilities Industry Via Weaponized PDF File originally appeared on GB Hackers.