Hundreds of Docker Hosts Compromised in Cryptojacking Campaigns
Poorly protected Docker hosts exposed online continue to be a privileged target of crooks that abuse their computational resources in cryptojacking campaigns.
Security experts have recently discovered hundreds of exposed Docker hosts that have been compromised by hackers exploiting the CVE-2019-5736 runc vulnerability in February.
The flaw was discovered by the security researchers Adam Iwaniuk and Borys Poplawski, it disclosed by Aleksa Sarai, a senior software engineer at SUSE Linux GmbH, it affectsrunc, the default container runtime for Docker, containerd, Podman, and CRI-O.
Such kind of vulnerabilities could have a significant impact on an IT environment, its exploitation could potentially escape containment, impacting the entire container host, ultimately compromising the hundreds-to-thousands of other containers running on it
The flaw could affect popular cloud platforms, including AWS, Google Cloud, and several Linux distros.
The PoC exploit code for the container escape was published on GitHub, its execution requires root (uid0) inside the container.
“This is a Go implementation of CVE-2019-5736, a container escape for Docker. The exploit works by overwriting and executing the host systems runc binary from within the container. ” states the author of the code on Github.
“An attacker would need to get command execution inside a container and start a malicious binary which would listen. When someone (attacker or victim) uses docker exec to get into the container, this will trigger the exploit which will allow code execution as root,”
The PoC code allows a malicious container to (with minimal user interaction) to overwrite the host runc binary and gain root-level code execution on the host.
Unfortunately, there are still thousands of exposed Docker hosts left unpatched.
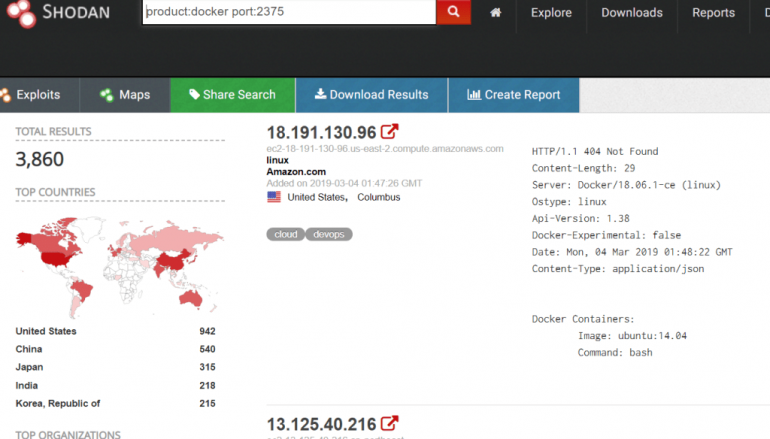
The flaw was disclosed on February 11, at the time there were approximately 3,951 daemons exposed. Now security experts Vitaly Simonovich and Ori Nakar from Imperva discovered roughly 4,042 exposed Docker daemons.

At the time of writing, I’have found 3,860 installs with the 2375 port open and 74 with the port 2376 accessible. Experts pointed only one hundred daemons have been updated to the patched 18.09.2 version or newer, remaining ones are still vulnerable to the attacks.
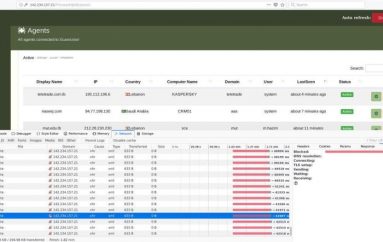
Experts discovered that the unpatched servers that were exposed online had the Docker API accessible from the loopback interface (“localhost”, “127.0.0.1”).
“We found 3,822 Docker hosts with the remote API exposed publicly.” reads the analysis published by Imperva.
“We wanted to see how many of these IPs are really exposed. In our research, we tried to connect to the IPs on port 2735 and list the Docker images. Out of 3,822 IPs, we found approximately 400 IPs are accessible.”
The researchers found Docker images of crypto miners, as well as legitimate services.
“We found that most of the exposed Docker remote API IPs are running a cryptocurrency miner for a currency called Monero. Monero transactions are obfuscated, meaning it is nearly impossible to track the source, amount, or destination of a transaction.” continues the analysis.
“Other hosts were running what seemed to be production environments of MySQL database servers, Apache Tomcat, and others.”
Experts pointed out that threat actors could compromise Docker daemons for other malicious activities, including:
- Create a botnet
- Host services for phishing campaigns
- Steal credentials and data
- Pivot attacks to the internal network
This post Hundreds of Docker Hosts Compromised in Cryptojacking Campaigns originally appeared on Security Affairs.