Critical Vulnerability in Microsoft Azure Let Hackers Take Over the Complete Control of the Azure Accounts
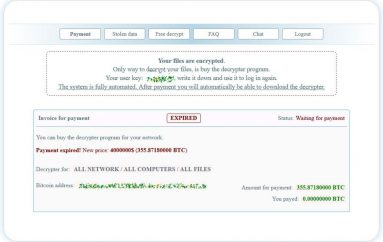
Researchers discovered a critical vulnerability in Microsoft Azure named “BlackDirect” that allows attackers to take over the Azure user’s accounts and creating the Token with the victim’s permissions.
The vulnerability specifically affected Microsoft’s OAuth 2.0 applications that allow malicious attacker access and control a victim’s account
“OAuth is a protocol for authorization that is commonly used as a way for end-users to grant websites or applications access to their information from other websites without giving the website or app secrets or passwords.”
In the next generation, OAuth2 allows third-party applications to grant limited access to an HTTP service and accessing clients might be a website or mobile application.
OAuth applications trust domains and sub-domains are not registered on behalf of Microsoft, and it can be registered by anyone. by default, OAuth approved the applications request and are allowed to ask for “access_token.”.
Researchers found that the combination of these two factors makes it possible to produce action with the user’s permissions – including gaining access to Azure resources, AD resources and more.
“This vulnerability’s attack surface is very wide and its impact can be very powerful. By doing nothing more than clicking or visiting a website, the victim can experience the theft of sensitive data, compromised production servers, lost data, manipulation of data, encryption of all the organization’s data with ransomware and more.”
Exploiting the BlackDirect Vulnerability
To exploit the vulnerability, researchers initially have listed all the service principals in their account using the “Get-AzureADServicePrincipal” command.
Later they found the URL that allowed by Microsoft application, in which some of the URLs end with “.cloudapp.net”, “.azurewebsites.net” and .{vm_region}.cloudapp.azure.com,” these all the URL registered via Microsoft Azure portal.
Omer Tsarfati from cyberark said, “To make sure no real attackers could exploit this vulnerability, I registered every sub-domain that wasn’t already registered – 54 of them That being said, there may be more sub-domains that aren’t listed.”
There are 3 following apps that are vulnerable for this account to take the attack.
- Portfolios
- O365 Secure Score
- Microsoft Service Trust
“This vulnerability makes it much easier to compromise privileged users – whether through simple social engineering techniques or by infecting a website that the privileged users occasionally access.”
As a result, the attacker will compromise the entire domain and the organization’s Azure environment.
Proof of Concept Video:
You can read the complete technical analysis here.
Mitigation Steps
- Make sure that all the trusted redirect URIs configured in the application are under your ownership.
- Remove unnecessary redirect URIs.
- Make sure the permissions that the OAuth application asks for are the least privileged one it needs.
- Disable non-used applications.
This post Critical Vulnerability in Microsoft Azure Let Hackers Take Over the Complete Control of the Azure Accounts originally appeared on GB Hackers.