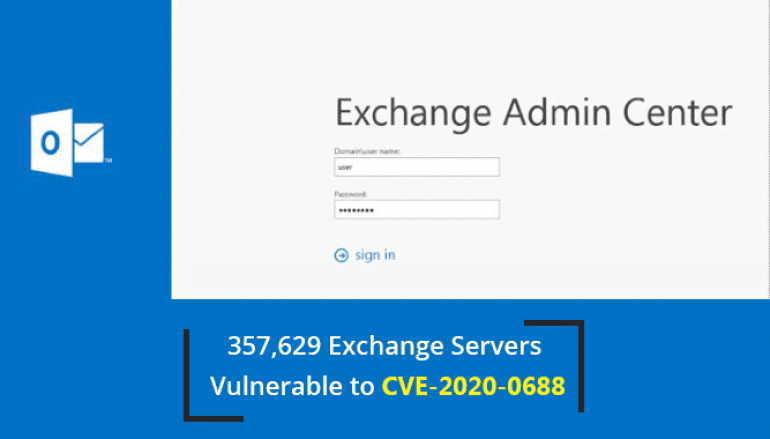
80% of Exchange Servers Still Unpatched to Critical Remote Code Execution Vulnerability
Microsoft recently patched a remote code execution vulnerability with Microsoft Exchange Server that allows an attacker to use an Exchange user account to compromise the system completely.
The bug resides in the Exchange Control Panel (ECP) component, which can be used to manage mailboxes, Distribution Groups, Contacts at the mailbox level and several other objects at the Organization level.
Based on the Rapid 7 survey using Project Sonar over 350,000 Exchange servers with the vulnerability found exposed to online.
Project Sonar is a tool used to conduct internet-wide surveys across different services and protocols to gain insights into global exposure to common vulnerabilities.
Based on the Project Sonar survey report more than 433,464 Exchange servers found to be online, at least 357,629 (82.5%) found to be vulnerable.
“Our remote, unauthenticated check doesn’t provide the version precision we’d need to be sure and our testing found that the related Microsoft update wasn’t always updating the build number, which leads to a degree of uncertainty,” reads the blog post.

The report also states that over 31,000 Exchange 2010 servers were not updated since 2012 and 800 Exchange 2010 servers never been updated.
Multiple APT actors already attempting to exploit recently patched remote code execution bug in exchange email servers.
According to Microsoft the bug was due to a memory corruption vulnerability and could be exploited by an attacker by sending a crafted email sent to a vulnerable Exchange server.
Microsoft patched the vulnerability in February 2020, users are recommended to apply the updates for addressing the vulnerability.
This post 80% of Exchange Servers Still Unpatched to Critical Remote Code Execution Vulnerability originally appeared on GB Hackers.