Archive
Biometric authentication, including facial recognition and fingerprint scanners, is increasingly common, but that doesn’t mean they are safe from hackers. At the DEFCON virtual security conference on August 8, security researcher Yamila Levalle from Dreamlab Technologies outlined how she was
An attacker could use $300 worth of off-the-shelf equipment to eavesdrop and intercept signals from satellite internet communications. The academic researcher James Pavur, speaking at Black Hat 2020 hacking conference, explained that satellite internet communications are susceptible to eavesdropping and
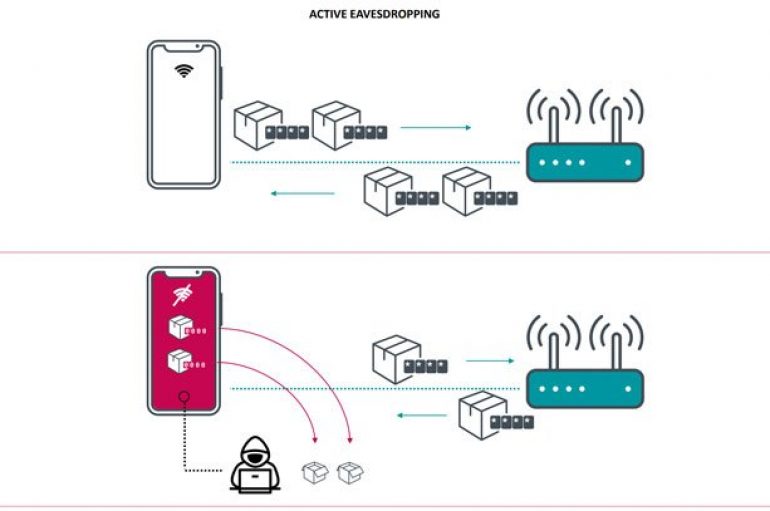
The security researchers have recently detected that small Qualcomm and MediaTek Wi-Fi chips are vulnerable to the latest variants of the KrOOk data exposure vulnerability. KrOOk is a quite dangerous vulnerability, and this vulnerability has now affected more Wi-Fi chipsets
Reddit suffered a massive hack, multiple subreddits have been defaced during the last 24 hours, and the attackers posted messages supporting Donald Trump’s reelection campaign. Reddit administrators urged users to enable two-factor authentication (2FA) on their accounts and to change
Researchers detailed a new evasive phishing technique that leverages modified favicons to inject e-skimmers and steal payment card data covertly. Researchers from cybersecurity firm Malwarebytes have analyzed a new evasive phishing technique used by attackers in the wild in Magecart
Chinese researchers discovered tens of vulnerabilities in a Mercedes-Benz E-Class, including issues that can be exploited to remotely hack it. A team of Chinese experts from Sky-Go, the Qihoo 360 division focused on car hacking, discovered 19 vulnerabilities in a
Wi-Fi chips manufactured by Qualcomm and MediaTek are impacted by vulnerabilities similar to the Kr00k issue disclosed early this year. Earlier this year, experts from ESET disclosed the Kr00k, a new high-severity hardware vulnerability, that affects Wi-Fi chips manufactured by
Clothing retailer Monsoon Accessorize has been using VPN servers that have critical vulnerabilities, putting it at risk of hacking or ransomware attack, according to an analysis by VPNpro. The researchers discovered that Monsoon has been utilizing unpatched Pulse Connect Secure
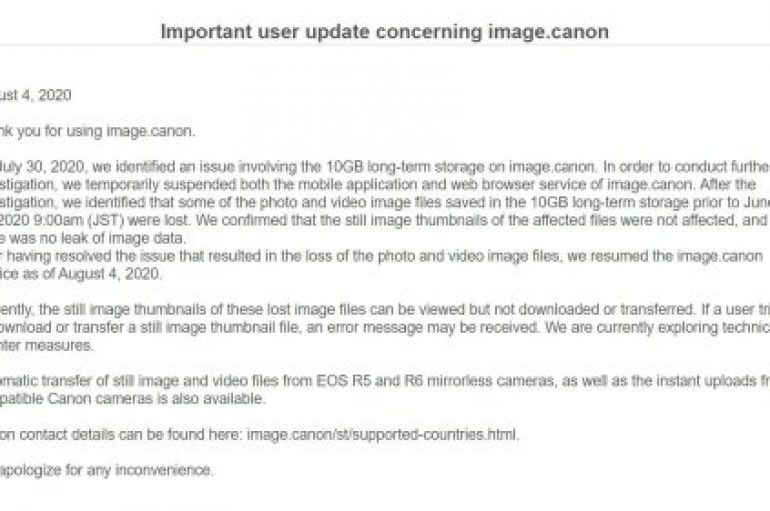
An internal memo confirms that the prolonged outage suffered by Canon last week was caused by a ransomware infection, Maze operators took credit for it. According to an internal memo obtained by ZDNet, the recent outage of Canon was caused
Cybrary Releases Free Cybersecurity Courses
The world’s largest online cybersecurity career development platform has released a second installment of free educational courses. Cybrary made a clutch of courses free in July in a bid to support people who are considering a career in cybersecurity and
Britain’s National Trust has warned volunteers of a data breach linked to a cyber-attack on US cloud computing and software provider Blackbaud in May. The charity and membership organization for heritage conservation in England, Wales, and Northern Ireland has been
Capital One Fined $80m for 2019 Breach
Capital One has been fined $80m following its breach last year. According to a statement from the Office of the Comptroller of the Currency (OCC), these actions were taken against Capital One “based on the bank’s failure to establish effective
New guidance has been produced on cyber insurance to help organizations considering investing in cover. Published by the National Cyber Security Center (NCSC), the guidance highlights seven key cybersecurity questions for businesses to address to help them make more informed
The ‘from’ address field in an email is supposed to identify the person that sent an email, but unfortunately that’s not always the case. In a Black Hat USA 2020 virtual conference session researchers outlined 18 different attacks against email
EtherOops – A New Attack Let Hackers Exploit a Bug in Ethernet Cables to Bypass Firewall and NATs
Researchers unveiled a very new method that helps to exploit a vulnerability in Ethernet cables to bypass firewalls and NATs. Earlier, this exploitation is considered as non-exploitable; but, now the weakness was named as Etheroops. This vulnerability works only if
More than half (55%) of all cyber-attacks targeted organizations’ applications in 2019, which is a substantial increase compared to the previous few years, when these types of attacks made up around 30% of the total number. This is according to