Archive
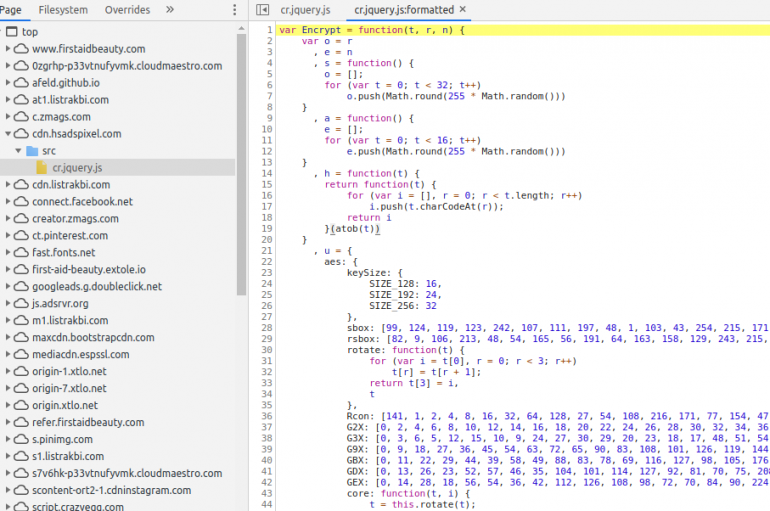
According to Willem de Groot, a researcher at Sanguine Security, threat actors planted a MageCart software skimmer on Procter & Gamble’s site First Aid Beauty on May 5, and the malicious code has remained undetected since today. First Aid Beauty
NFC Beaming Vulnerability in Android Let Hackers to Infect Vulnerable Devices With Malware
NFC expanded as Near Field Communication, contains a set of protocols that allows Android devices to establish communication at a very shortest range. NFC used for contactless payments, pairing of devices, file sharing, and access control. Nightwatch Cybersecurity noted that
An app used by drivers to cut the cost of fuel has suffered a data breach that allowed users to view the personal information of other customers. Names, email addresses, cell phone numbers, and dates of birth were exposed following
Johannesburg Held to Ransom
The city of Johannesburg has shut down its entire computer network after being targeted by a Bitcoin ransomware attack. According to The Times, South Africa’s commercial capital was hacked by a threat group called the Shadow Kill Hackers Group. The
The United States’ Department of Health and Human Services has proposed amending laws around non-monetary donations in a bid to help doctors protect healthcare services from cyber-attacks. The DHHS published proposed rules to update the regulatory Anti-Kickback Statute (AKS) safe
Two Democratic Party senators have demanded an investigation into whether Amazon Web Services (AWS) broke the law by failing to secure infrastructure which was compromised in the Capital One breach. Former AWS software engineer Paige Thompson has been accused by
Security researchers are warning of an ongoing mobile-aware phishing campaign targeting the United Nations and various NGOs for Okta, Office 365 and Outlook account credentials. The two domains hosting the phishing content have been live since March 2019, with most
Fortinet has analyzed the NukeSped RAT that is believed to be a malware in the arsenal of the Lazarus North-Korea linked APT group. The attribution to the Lazarus group is based on the similarities with other malware associated with the
Russian Hackers Compromised 100,000+ Computers Using Raccoon Malware Via Fallout & RIG Exploit Kits
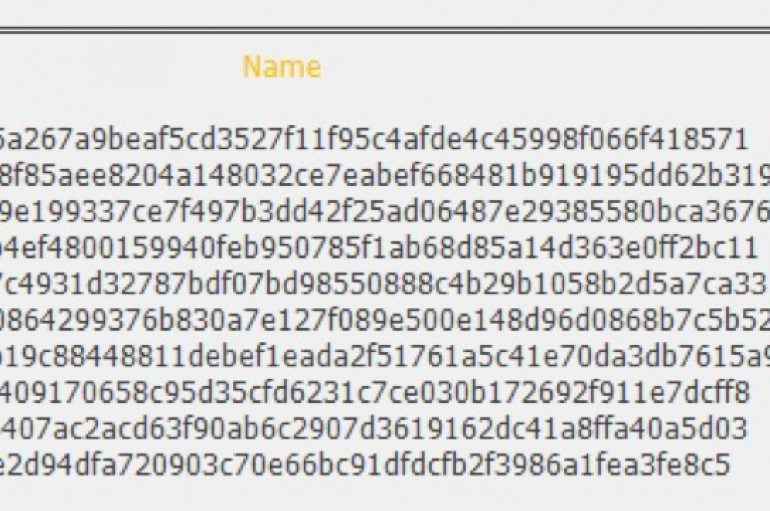
Researchers uncovered an information-stealing malware called Raccoon that delivered by the Fallout and RIG Exploit Kits to steal sensitive data from compromised victims’ devices. Raccoon malware reportedly hacked more than 100,000 computers around the world since April 2019, and the
42 Malicious Android Apps Downloaded 8 Million Times From Google Play That Infect Users With Malware
Researchers found nearly 8 Million Android users infected with adware that hides in the phone and display ads as per the attacker’s command. Researchers from ESET security identified dozens of apps with such behavior. In total 43 apps observed on
Phishing Scam Nets Montana Healthcare Service
A Montana healthcare provider that fell victim to a phishing scam has notified 129,000 patients that their personal information was exposed. According to Flathead Beacon, Kalispell Regional Healthcare (KRH) informed all its patients by letter on Tuesday of the breach,
The IT security industry threatens to be overwhelmed by cyber-threats if it doesn’t relax hiring rules, the Chartered Institute of Information Security (CIISec) has warned. In one of its first pronouncements since being awarded a prestigious Royal Charter, the industry
Action Fraud Snafu Leaves 9000 Cases Quarantined
Thousands of cybercrime reports sent to the UK’s centralized authority have been mistakenly identified as containing malware, meaning they were not investigated, according to a new report. The report, Cyber: Keep the light on – An inspection of the police
New research from bug bounty and pen testing platform HackerOne has revealed that four major data breaches – British Airways (2018), Carphone Warehouse (2018), TicketMaster (2018) and TalkTalk (2015) – which cost over £265m in damages cumulatively, could have been
AWS Left Reeling After Eight-Hour DDoS
Amazon Web Services (AWS) customers were hit by severe outages yesterday after an apparent DDoS attack took S3 and other services offline for up to eight hours. The attack hit the cloud giant’s Router 53 DNS web service, which had
Malicious Android Apps From Google Play Store Steal The SMS verification Code From System Notifications
Researchers uncovered a new malicious Android app from the Google play store that disguised as a Photo Beautification App steal the SMS verification code and activate the Wireless Application Protocol (WAP) billing. Since earlier this year, Google made various changes