USB-IF battles malware and bad chargers with Type-C Authentication spec
So far, adoption of the versatile, reversible USB Type-C connector has been going pretty well. It’s hardly universal, but it’s showing up in an increasing number of smartphones and laptops, and the number of cables and other accessories that support it is slowly growing. One of the problems that has emerged as the port has grown in popularity is non-compliant cables and power adapters, accessories that look like they ought to work but might actually end up frying the device they’re plugged into.
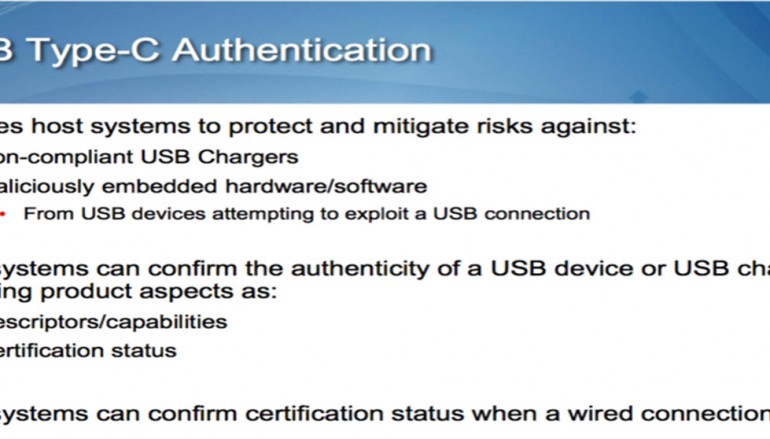
That’s one of the problems the USB-IF is trying to solve with the USB Type-C Authentication specification, announced today at the Intel Developer Forum in Shenzhen, China. When you connect a power adapter, cable, or accessory that supports the specification into a host device (like a phone or laptop) that supports the specification, the host device can verify the accessories’ capabilities and whether the accessory has been fully certified by the USB-IF. This information is transmitted to the host using 128-bit encryption before an actual data or power connection is established, and the specification is designed to work even if your charger and cable are only providing power and not a data connection.
We’ve already seen some companies make USB Type-C chargers that don’t work universally with all USB Type-C devices, as outlined in this PC World article from late last year. A supplemental specification that makes verifying the capabilities of chargers easier should hopefully put a stop to this sort of thing. The USB-IF also continues to encourage OEMs and accessory makers to use the various USB logos to clarify the capabilities of their devices, though the use of those logos on actual real-world devices is hit-or-miss at this point.
The authentication specification is also intended to combat malware and other exploits that use USB to infect or attack systems. In one possible real-world use case outlined by the USB-IF, a bank worried about USB thumbdrive security could conceivably configure its PCs so that they only work with drives that have that bank’s security certificates installed. The USB-IF says the spec “references existing internationally-accepted cryptographic methods for certificate format, digital signing, hash and random number generation,” so it ought to be relatively easy to implement in accessories.
On the host side, the USB-IF says that support for these new specifications could conceivably be implemented through a combination of firmware and software updates (though this will obviously be up to individual OEMs). Adapters, cables, and other accessories that can’t receive firmware or software updates will need to be replaced with new accessories that support the standard.
The USB-IF also made what it calls a minor “developer-only update” to the USB Power Delivery spec. USB Power Delivery 3.0 introduces support for the Authentication standard described above as well as USB Type-C Bridging; otherwise it is unchanged from the Power Delivery 2.0 spec.
Source | ARSTechnica





