Travelex Begins Reboot as VPN Bug Persists
Under-fire foreign currency firm Travelex has claimed its first customer-facing services in the UK have gone live after a crippling ransomware attack in December, with experts suggesting an unpatched VPN bug may have been to blame.
The London-headquartered business has been slammed by customers after the suspected Sodinokibi (REvil) ransomware struck on December 31, forcing it to take systems offline as a precautionary measure.
Several complained that the foreign currency they ordered and paid for online is unavailable, leaving them out of pocket. The outage affected not just Travelex’s websites but its bricks-and-mortar outlets and services it provides to major UK high street banks such as Barclays and RBS.
However, the firm claimed in an update on Friday it has been working hard this month to restore online and customer-facing systems.
“On 17 January 2020, we confirmed that the first of our customer-facing systems in the UK were live and that the phased restoration of our systems globally was now firmly underway. We are prioritizing the UK as this is our single largest market,” it said.
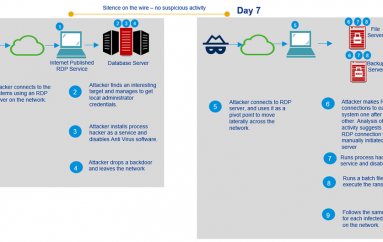
Although unconfirmed, security experts believe that an unpatched critical vulnerability in Pulse Secure VPNs (CVE-2019-11510) may have allowed attackers to remotely execute malicious code on Travelex IT systems.
Troy Mursch of Bad Packets claimed to have reached out to the firm in September to flag the software flaw, which has a CVSS score of 10.0, but received no response.
On Friday, he said that there are still over 3000 vulnerable Pulse Secure VPN servers out there. That’s bad news because the bug is seeing “wide exploitation,” despite the fact that a patch has been available since April 2019, according to the US Cybersecurity and Infrastructure Security Agency (CISA).
“A remote, unauthenticated attacker may be able to compromise a vulnerable VPN server. The attacker may be able to gain access to all active users and their plain-text credentials,” CISA said of CVE-2019-11510.
“It may also be possible for the attacker to execute arbitrary commands on each VPN client as it successfully connects to the VPN server.”
Although Travelex maintains that there is “no evidence that any data has left the organization,” the hackers behind the $6 million ransom demand have claimed they exfiltrated 5GB of sensitive customer data last year.
This post Travelex Begins Reboot as VPN Bug Persists originally appeared on InfoSecurity Magazine.