SWIFT Banking Network Heist Accomplished With Malware
The story of the February cyberattack on the Bank of Bangladesh that sought $1 billion — and achieved $81 million — keeps looking more and more like a Hollywood caper movie.
The first account of the attack said it was detected by a misspelling, which prompted an employee of the victimized SWIFT banking network to look into it. Further stories came out insinuating that the Bangladesh network was actually undone by insecure and cheap routers.
Brussels-based SWIFT is central to interbank functioning; it is the financial nerve system of the world. So what really happened when it came under attack?
More Sophisticated Than First Believed
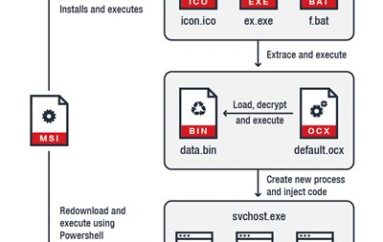
A new story has evolved, one far more menacing than bad routers. Security researchers at BAE Systems found tools lurking in malware repositories. They think the tools are connected to the attacks, stating, “The custom malware was submitted by a user in Bangladesh and contains sophisticated functionality for interacting with local SWIFT Alliance Access software running in the victim infrastructure.”
The tools seem to have been designed as part of an overall attack toolkit for SWIFT. The tools discovered were used to cover the attackers’ tracks while they sent payment instructions. By hiding their tracks, the attackers would have made detection harder, thus giving more time for money laundering to take place.
“The tools are highly configurable and, given the correct access, could feasibly be used for similar attacks in the future,” BAE Systems noted in its blog. “The tool was custom-made for this job and shows a significant level of knowledge of SWIFT Alliance Access software as well as good malware coding skills.”
The malware creator knew exactly how the SWIFT software functioned and what to do in order to bypass it. This was no random job: It was a targeted operation done using good intelligence.
SWIFT Banking Network Responds
SWIFT posted a response to all of this. “Contrary to reports that suggest otherwise, this malware has no impact on SWIFT’s network or core messaging services,” the network claimed.
“We have developed a facility to assist customers in enhancing their security and to spot inconsistencies in their local database records, however, the key defense against such attack scenarios remains for users to implement appropriate security measures in their local environments to safeguard their systems.”
The SWIFT banking network is shining the spotlight on the member banks, but it still has a serious problem: Someone knows just how to play the system. This exploit didn’t work all the way, but the next one might. The stakes are huge and call for the strongest possible response.
Source | SecurityIntelligence