Specially Crafted ZIP Archives Allow Bypassing Secure Email Gateways
Experts observed a new phishing campaign that used a specially crafted ZIP archive that was designed to bypass secure email gateways to distribute malware.
Attackers have devised a new technique to distribute malware bypassing secure email gateways and other security solutions by using a specially crafted ZIP file.
The structure of a ZIP archive contains compressed data, information about the compressed files and a single “End of Central Directory” (EOCD) record, that delimits the end of the archive structure.

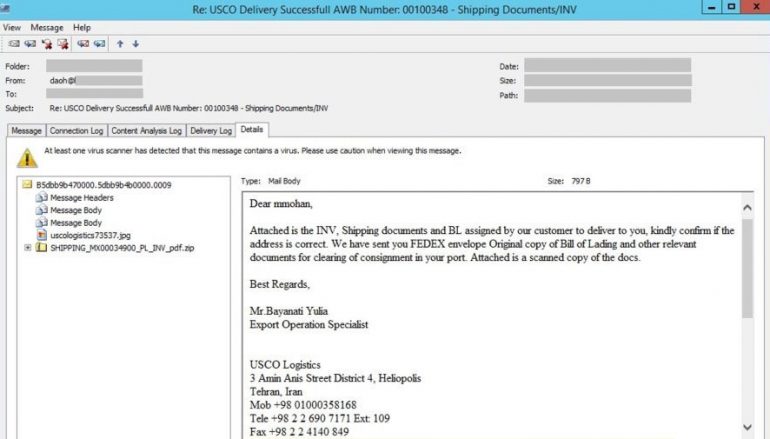
Researchers from TrustWave observed a spam campaign using fake shipping information messages pretending to be from an Export Operation Specialist of USCO Logistics.
The ZIP archive attached to the email messages, named SHIPPING_MX00034900_PL_INV_pdf.zip, raised suspicious due to its file size that was greater than its uncompressed content.
“The attachment “SHIPPING_MX00034900_PL_INV_pdf.zip” makes this message stand out,” reads a report published by Trustwave. “The ZIP file had a file size significantly greater than that of its uncompressed content. Typically, the size of the ZIP file should be less than the uncompressed content or, in some cases, ZIP files will grow larger than the original files by a reasonable number of bytes.”

The ZIP archive appeared as specially crafted and contained two distinct archive structures, each hacking its own EOCD record.
A first ZIP structure contained a decoy order.jpg file, while the second ZIP structure, contained a file named SHIPPING_MX00034900_PL_INV_pdf.exe, which is the NanoCore RAT.
The attackers behind this campaign crafted the ZIP archive to bypass secure email gateways making them to analyze only the harmless decoy image file hiding the malware.
The experts discovered that the ZIP content as viewed in different ways by different archiving tools, for example, the Windows built-in ZIP extractor consider it as not valid.
When experts attempted to open the ZIP archive with WinRar version 3.30 the software displayed in its UI the “order.jpg” as the only content of the ZIP attachment. However, it extracts “SHIPPING_MX00034900_PL_INV_pdf.exe”
“This sample challenges gateways scanners. Depending on the type of decompression engine used, there is a good probability that only the decoy file may be scrutinized and vetted, and the malicious content unnoticed – just like how some of the most popular archiving tools failed to notice the second ZIP structure.” concludes the report. “Despite what the gateway does, this attack would only succeed if the message got through the gateway and a particular archive utility is used by the end-user, such as certain versions of PowerArchiver, WinRar, and older 7Zip as described above.”
This post Specially Crafted ZIP Archives Allow Bypassing Secure Email Gateways originally appeared on Security Affairs.