Spam and Phishing in Q3 2018
Quarterly highlights
Personal data in spam
We have often said that personal data is candy on a stick to fraudsters and must be kept safe (that is, not given out on dubious websites). It can be used to gain access to accounts and in targeted attacks and ransomware campaigns.
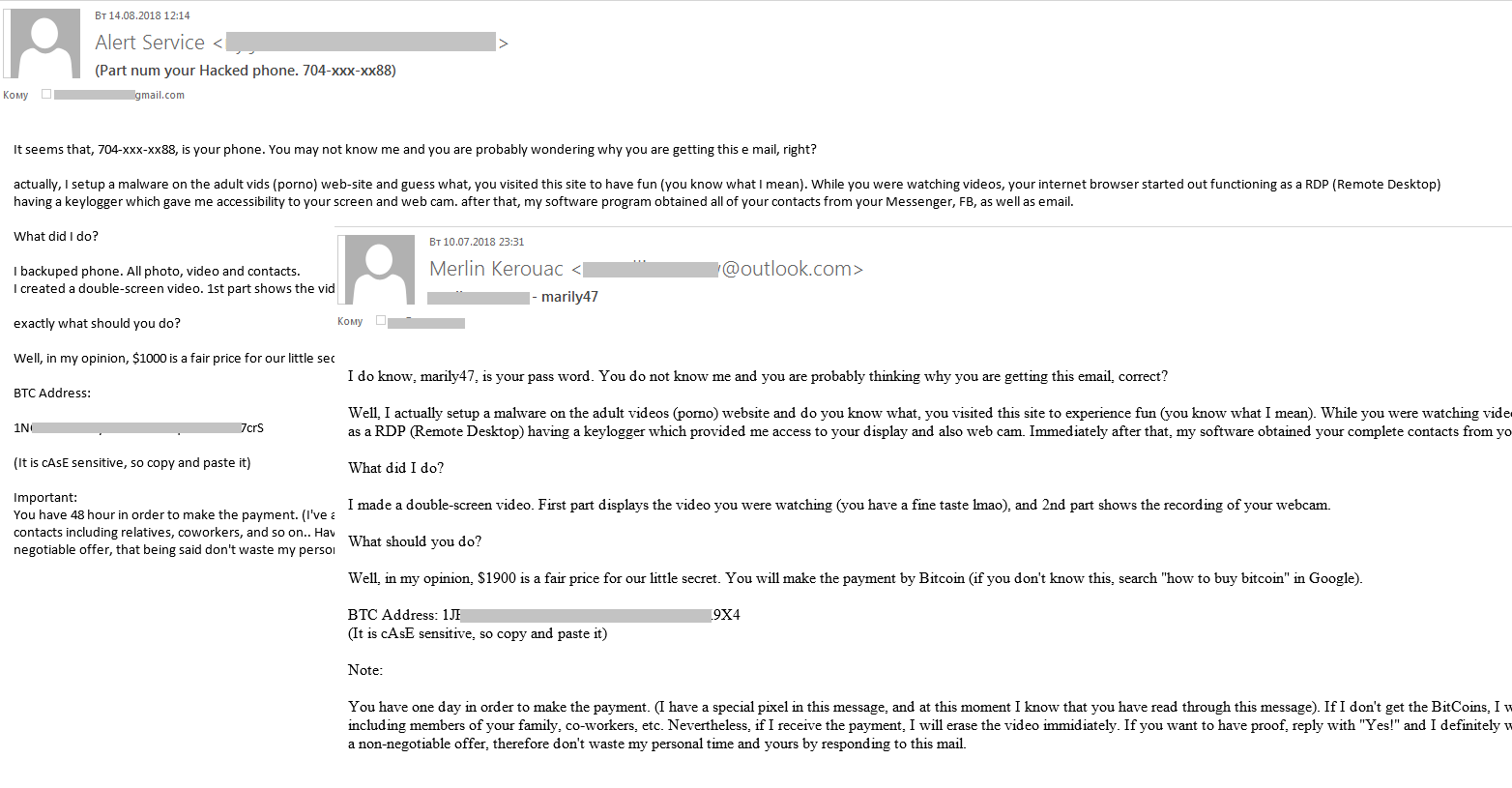
In Q3, we registered a surge of fraudulent emails in spam traffic. This type of scam we have already reported at the beginning of the year. A ransom (in bitcoins) is demanded in exchange for not disclosing the “damaging evidence” concerning the recipients. The new wave of emails contained users’ actual personal data (names, passwords, phone numbers), which the scammers used to try to convince victims that they really had the information specified in the message. The spam campaign was carried out in several stages, and it is likely that the fraudsters made use of a range of personal information databases, as evidenced, for example, by the telephone number formats that varied from stage to stage.
Whereas before, the target audience was primarily English-speaking, in September we logged a spate of mailings in other languages, including German, Italian, Arabic, and Japanese.
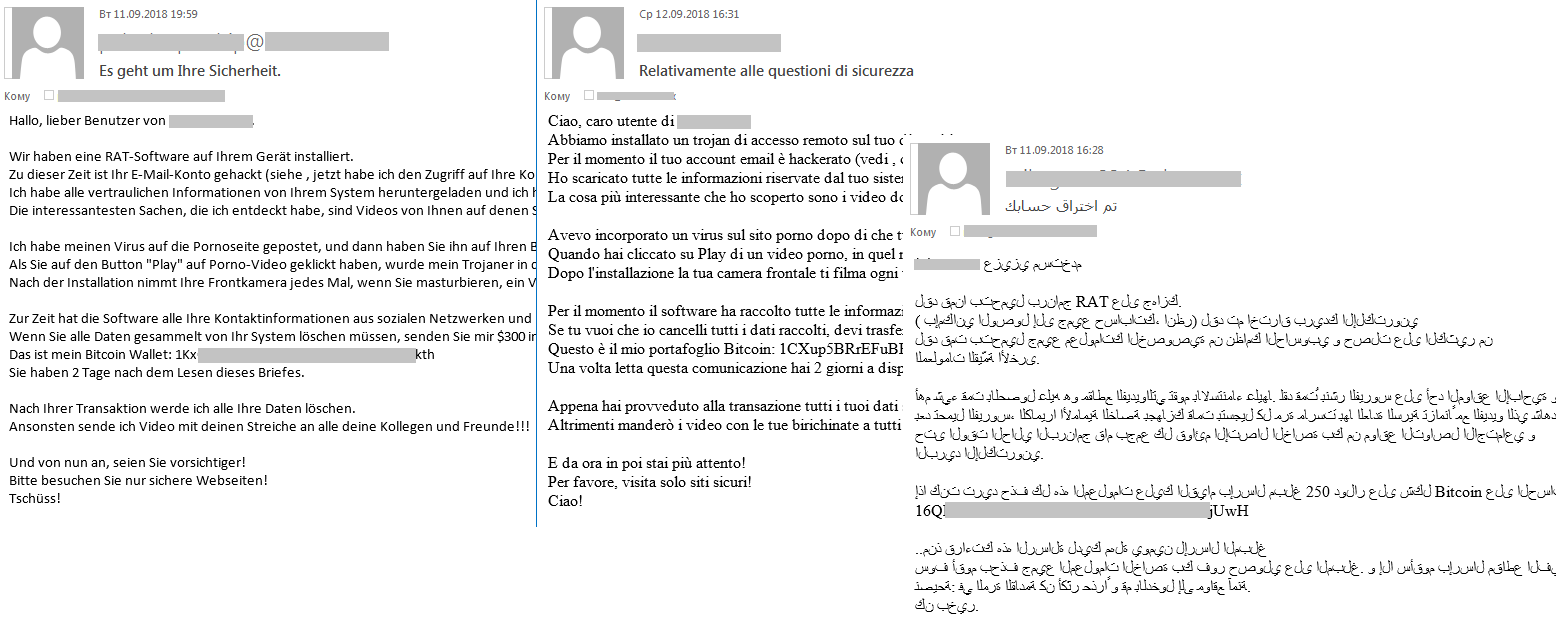
The amount demanded by the ransomers ranged from a few hundred to several thousand dollars. To collect the payments, different Bitcoin wallets were used, which changed from mailing to mailing. In July, 17 transactions worth more than 3 BTC ($18,000 at the then exchange rate) were made to one of such wallets.
Transactions to scammers’ Bitcoin wallets
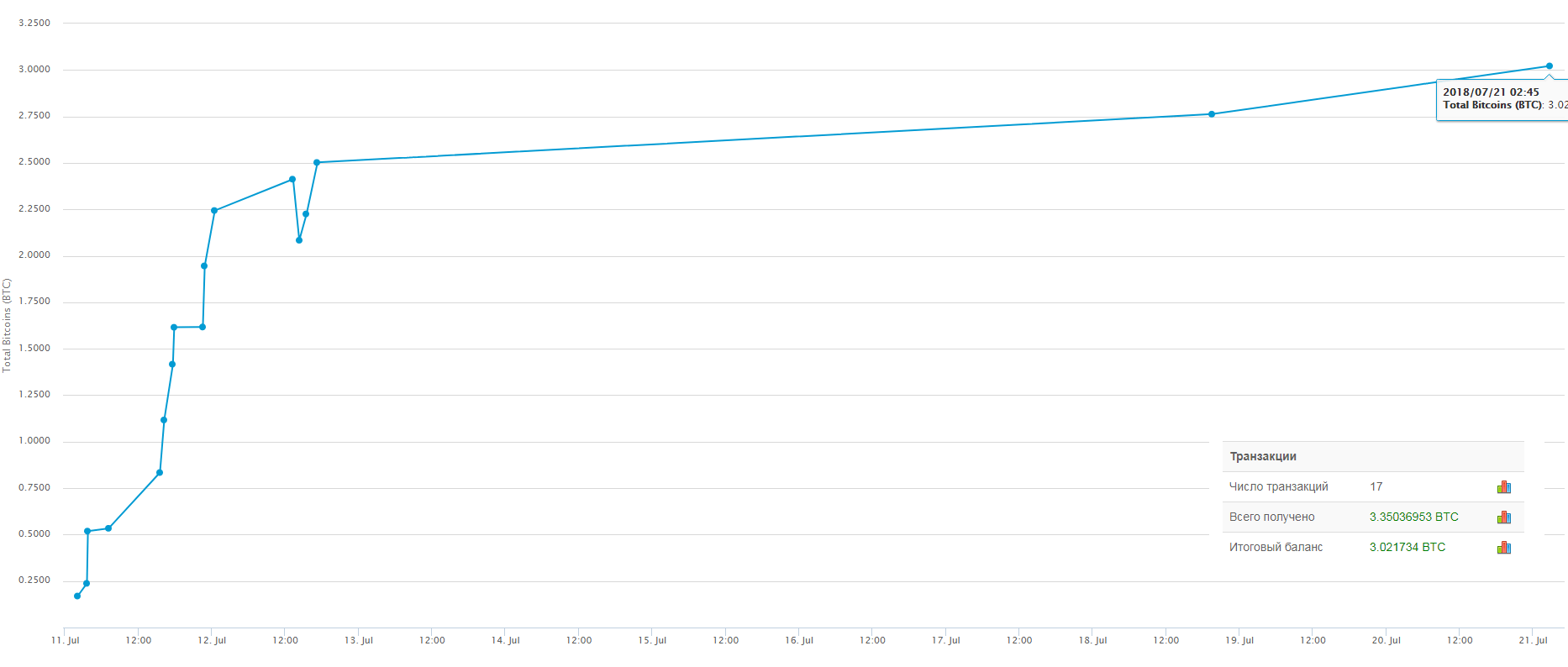
Also in Q3, we detected a malicious spam campaign aimed at corporate users. The main target was passwords (for browsers, instant messengers, email and FTP clients, cryptocurrency wallets, etc.). The cybercriminals attempted to infect victim computers with Loki Bot malware, concealing it in ISO files attached to messages. The latter were made to look like business correspondence or notifications from well-to-do companies.
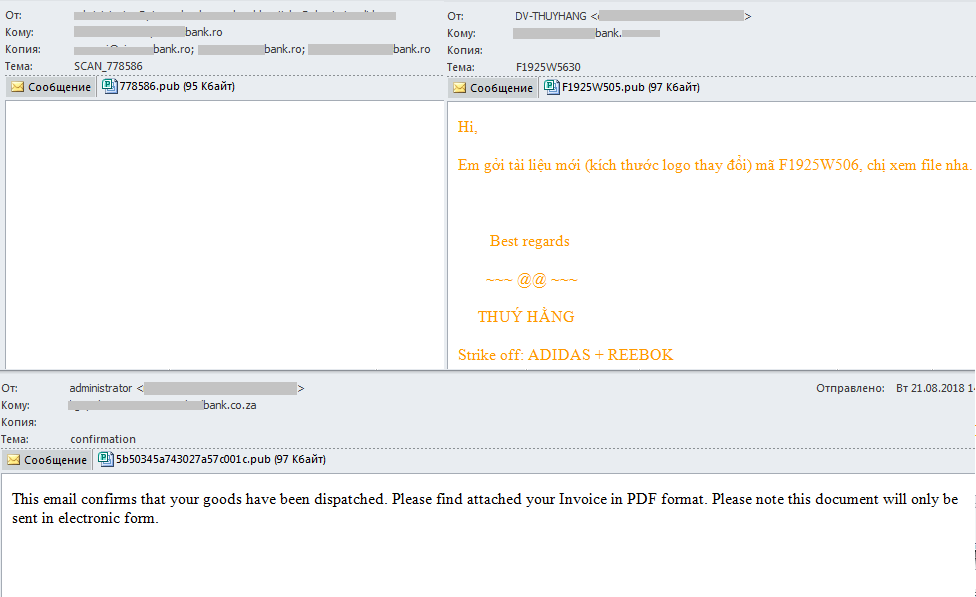
Malicious spam attacks against the banking sector
The owners of the Necurs botnet, which in Q2 was caught sending malicious emails with IQY (Microsoft Excel Web Query) attachments, turned their attention to the banking sector and, like in Q2, used a non-typical file format for spam, this time PUB (Microsoft Publisher). Messages were sent to the email addresses of credit institutions in different countries, and the PUB file attachments contained Trojan loaders for downloading executable files (detected as Backdoor.Win32.RA-based) onto victim computers.
We observed that the owners of Necurs are making increasing use of various techniques to bypass security solutions and send malicious spam containing attachments with non-typical extensions so as not to arouse users’ suspicion.
New iPhone launch
Late Q3 saw the release of Apple’s latest gizmo. Unsurprisingly, it coincided with a spike in email spam from Chinese “companies” offering Apple accessories and replica gadgets. Links in such messages typically point to a recently created, generic online store. Needless to say, having transferred funds to such one-day websites, you lose your money and your goods are not arriving.
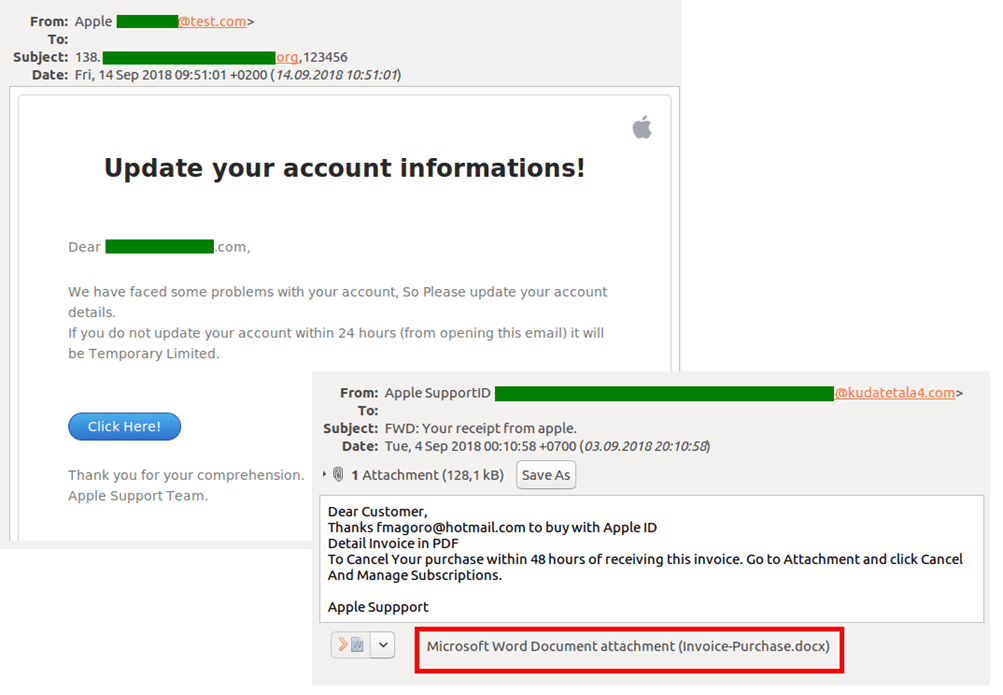
The release also went hand in hand with a slight rise in both the number of phishing schemes exploiting Apple (and its services) and messages with malicious attachments:
Classic pharma spam in a new guise
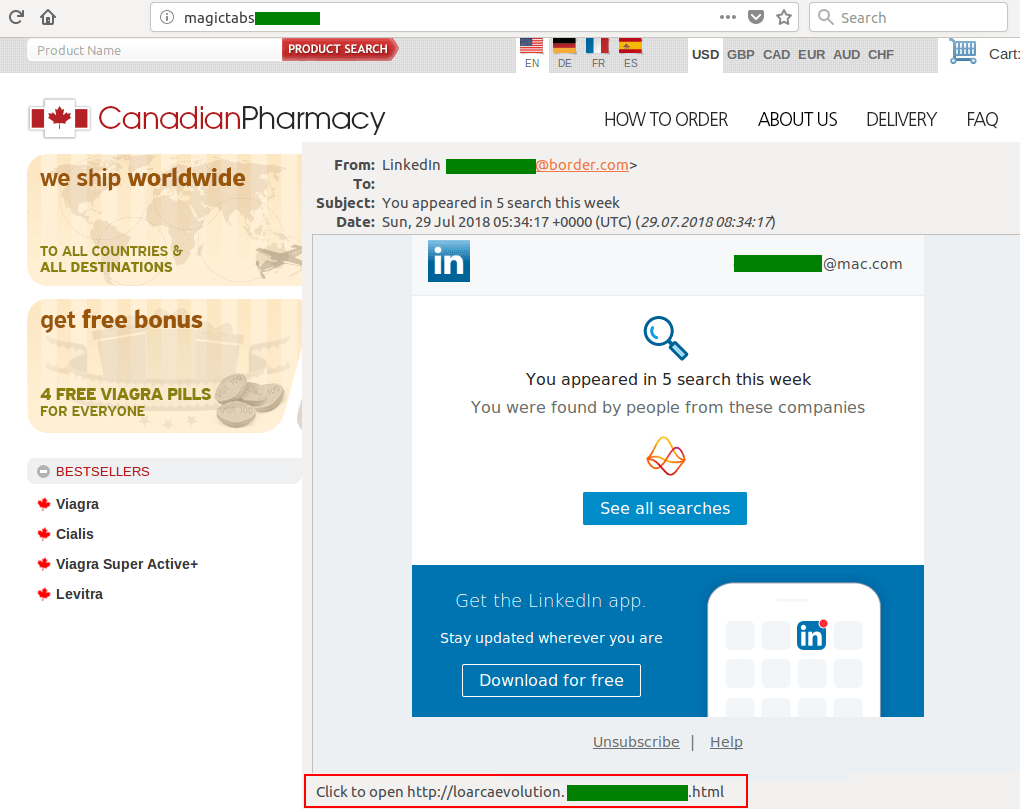
Spammers are constantly looking for ways to get round mail filters and increase the “deliverability” of their offers. To do so, they try to fabricate emails (both the contents and technical aspects) that look like messages from well-known companies and services. For example, they copy the layout of banking and other notifications and add bona fide headers in the fields that the user is sure to see.
Such techniques, typical of phishing and malicious campaigns, are being used more often in “classic spam” – for example, in messages offering prohibited medicines. For instance, this past quarter we detected messages disguised as notifications from major social networks, including LinkedIn. The messages contained a phoney link that we expected to point to a phishing form asking for personal data, but instead took us to a drug store.
This new approach is taken due to the fact that this type of spam in its traditional form has long been detectable by anti-spam solutions, so spammers started using disguises. We expect this trend to pick up steam.
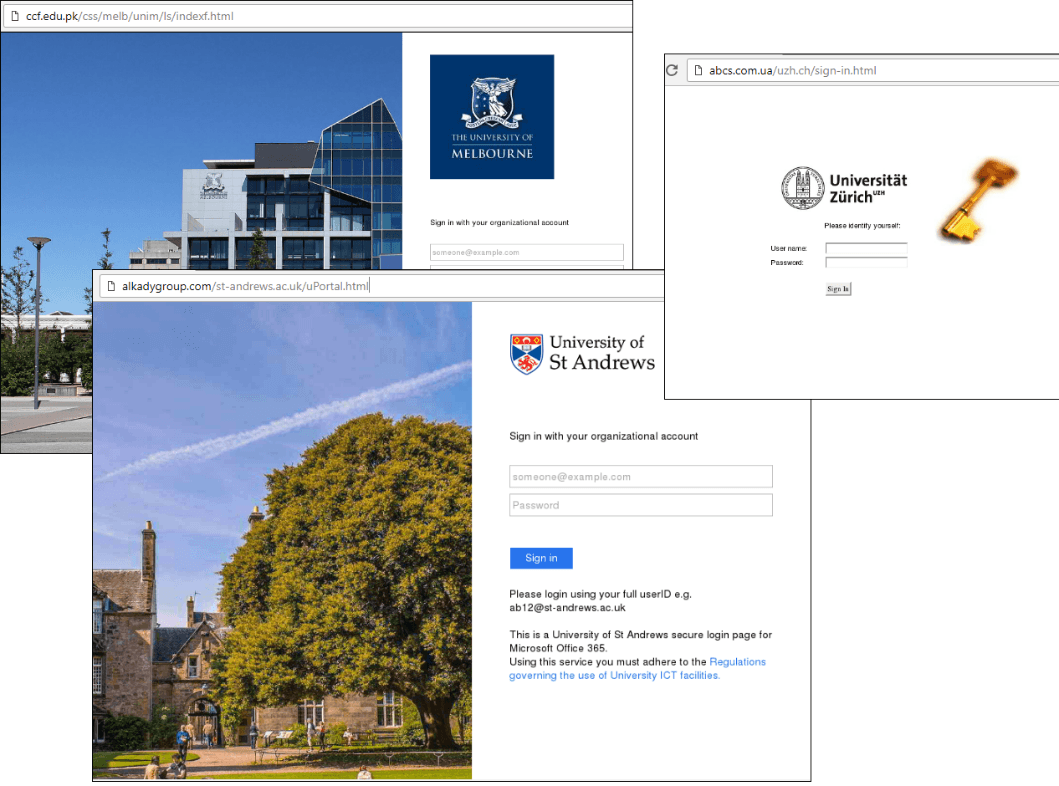
Universities
Since the start of the academic year, scammers’ interest in gaining access to accounts on university websites has risen. We registered attacks against 131 universities in 16 countries worldwide. Cybercriminals want to get their hands on both personal data and academic research.
Fake login pages to personal accounts on university websites
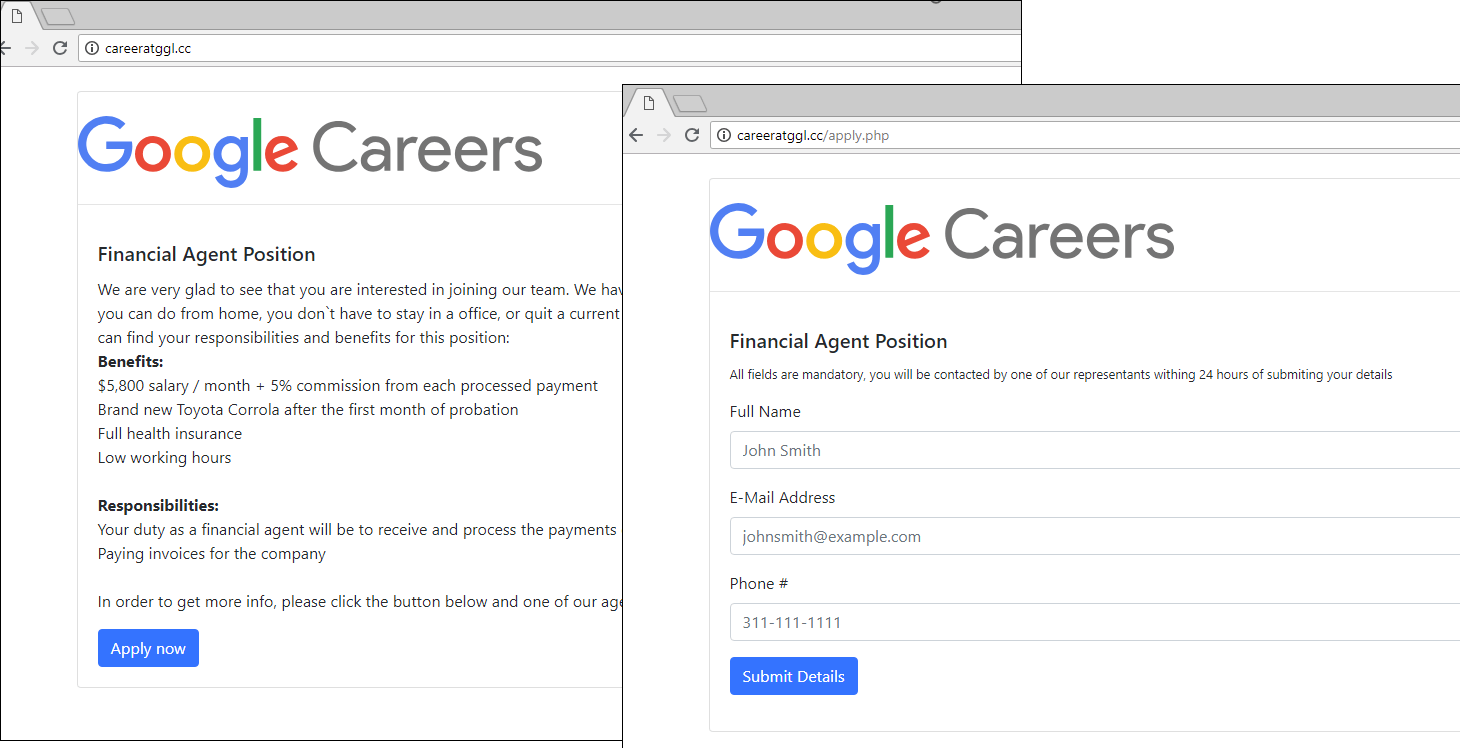
Job search
To harvest personal data, attackers exploit the job-hunting efforts. Pages with application forms lure victims with tempting offers of careers in a big-name company, large salary, and the like.
Propagation methods
This quarter we are again focused on ways in which phishing and other illegitimate content is distributed by cybercriminals. But this time we also want to draw attention to methods that are gaining popularity and being actively exploited by attackers.
Scam notifications
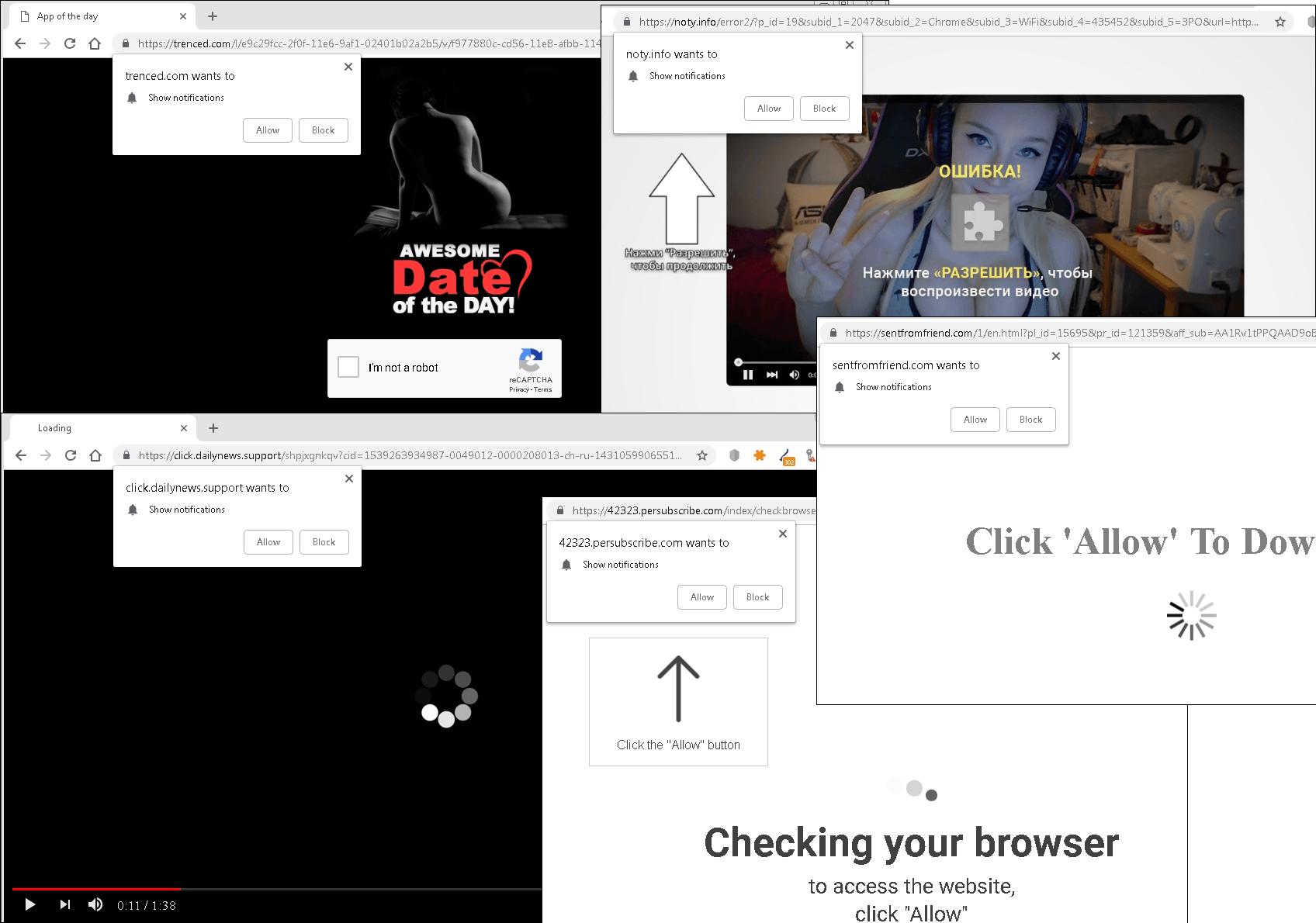
Some browsers make it possible for websites to send notifications to users (for example, Push API in Chrome), and this technology has not gone unnoticed by cybercriminals. It is mainly deployed by websites that collaborate with various partner networks. With the aid of pop-up notifications, users are lured onto “partner” sites, where they are prompted to enter, for example, personal data. The owners of the resource receive a reward for every user they process.
By default, Chrome requests permission to enable notifications for each individual site, and so as to nudge the user into making an affirmative decision, the attackers state that the page cannot continue loading without a little click on the Allow button.
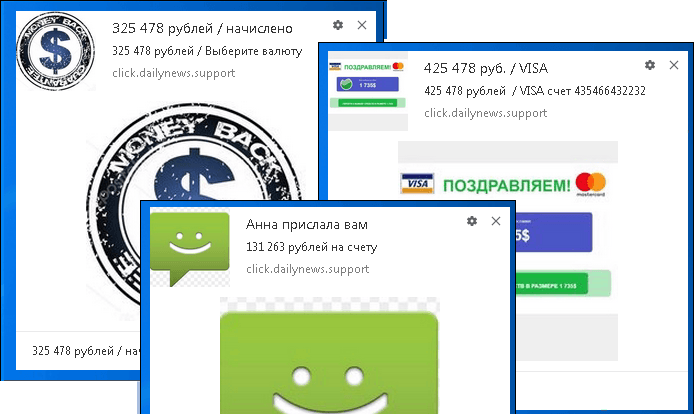
Having given the site permission to display notifications, many users simply forget about it, so when a pop-up message appears on the screen, they don’t always understand where it came from.
Notifications are tailored to the user’s location and displayed in the appropriate language
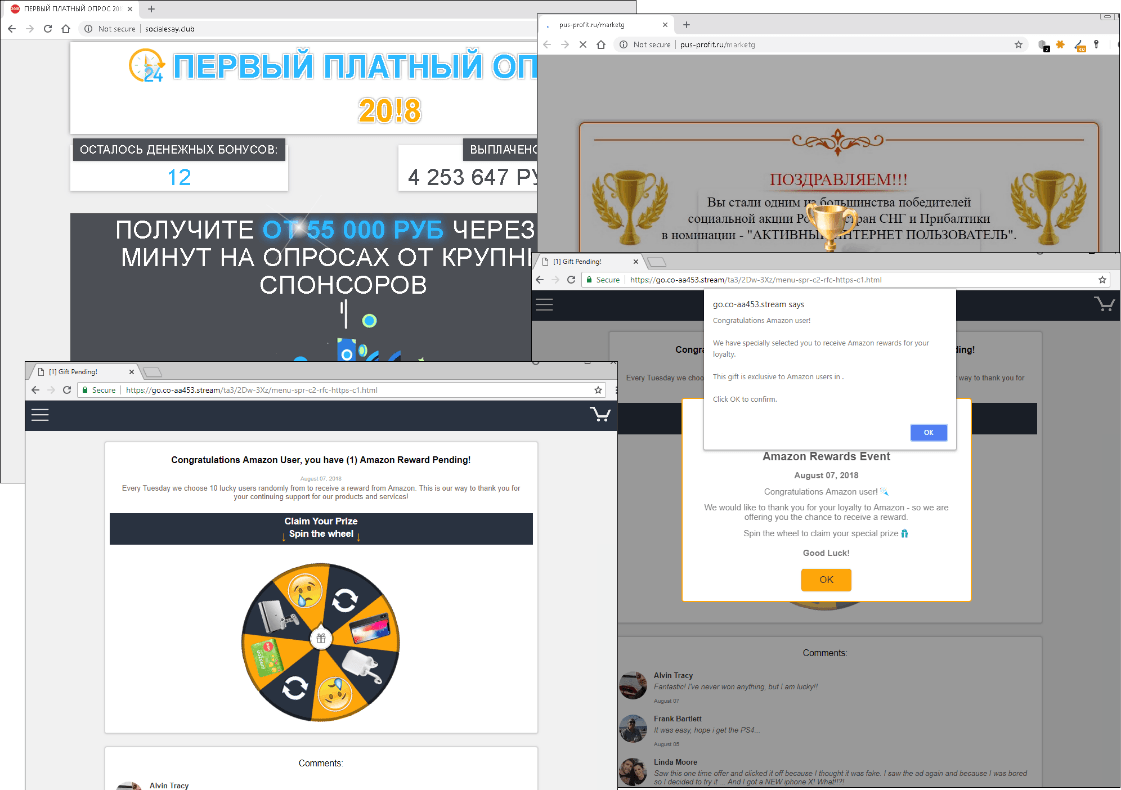
The danger is that notifications can appear when the user is visiting a trusted resource. This can mislead the victim as regards the source of the message: everything seems to suggest it came from the trusted site currently open. The user might see, for instance, a “notification” about a funds transfer, giveaway, or tasty offer. They all generally lead to phishing sites, online casinos, or sites with fake giveaways and paid subscriptions:
Examples of sites that open when users click on a notification
Clicking on a notification often leads to an online gift card generator, which we covered earlier in the quarter (it also works in the opposite direction: the resource may prompt to enable push notifications). Such generators offer visitors the chance to generate free gift card codes for popular online stores. The catch is that in order to get the generated codes, the visitor needs to prove their humanness by following a special link. Instead of receiving a code, the user is sent on a voyage through a long chain of partner sites with invitations to take part in giveaways, fill out forms, download stuff, sign up for paid SMS mailings, and much more.
Media
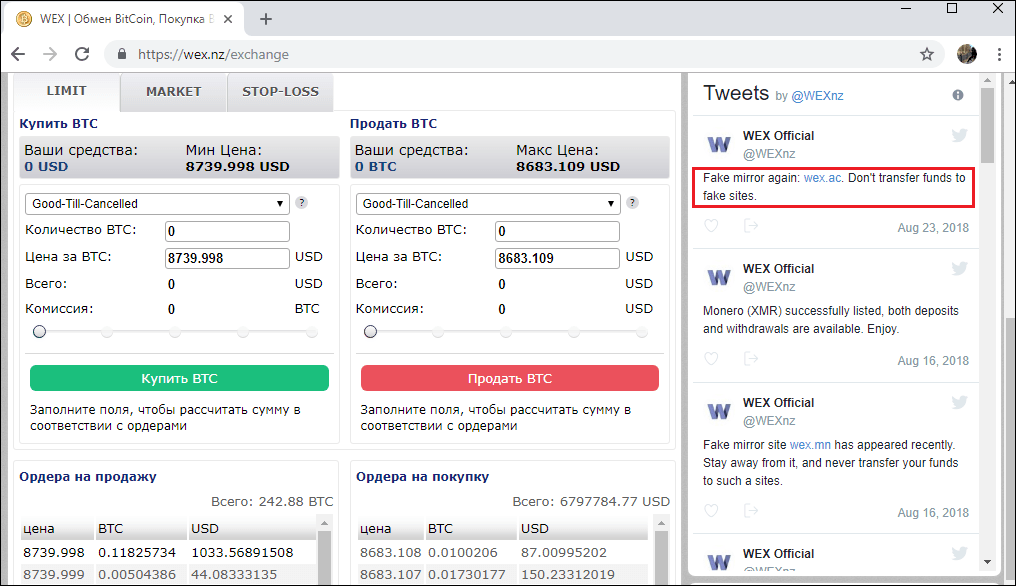
The use of media resources is a rather uncommon, yet effective way of distributing fraudulent content. This point is illustrated by the story of the quite popular WEX cryptocurrency exchange, which prior to 2017 went by the name of BTC-E. In August 2018, fake news was inserted into thematic “third tier” Russian media saying that, due to internal problems, the exchange was changing its domain name to wex.ac:
The wex.nz administration soon tweeted (its tweets are published on the exchange’s home page) that wex.ac was just another imitator and warned users about transferring funds.
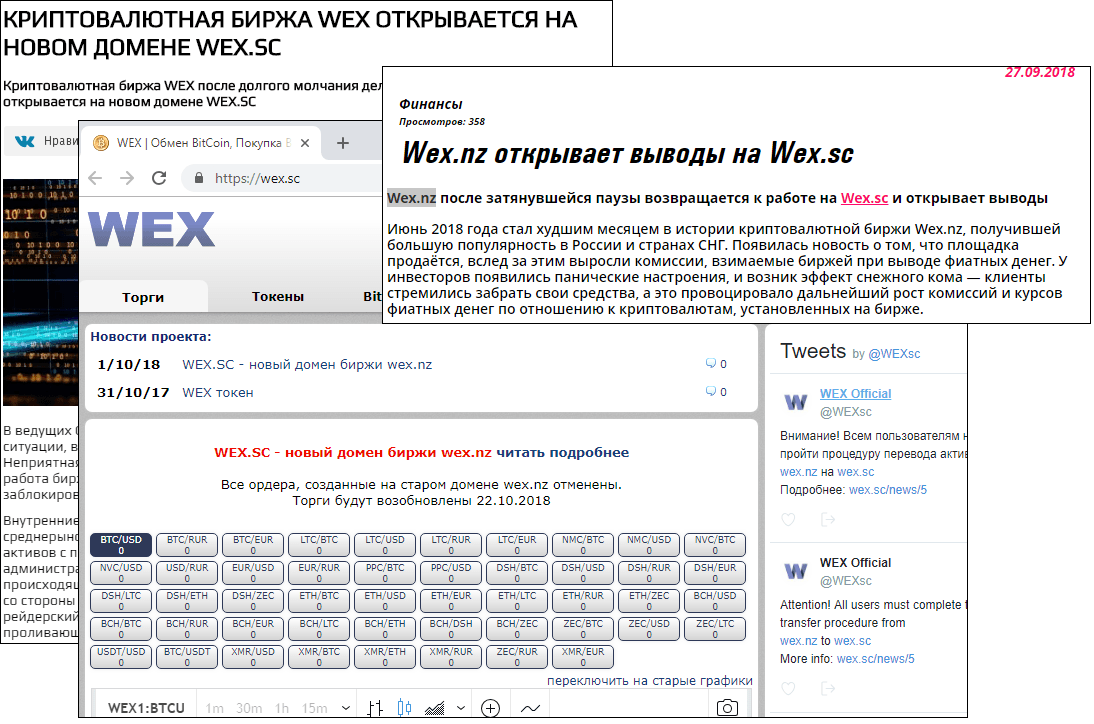
But that did not stop the scammers, who released more news about the exchange moving to a new domain. This time to the .sc zone:
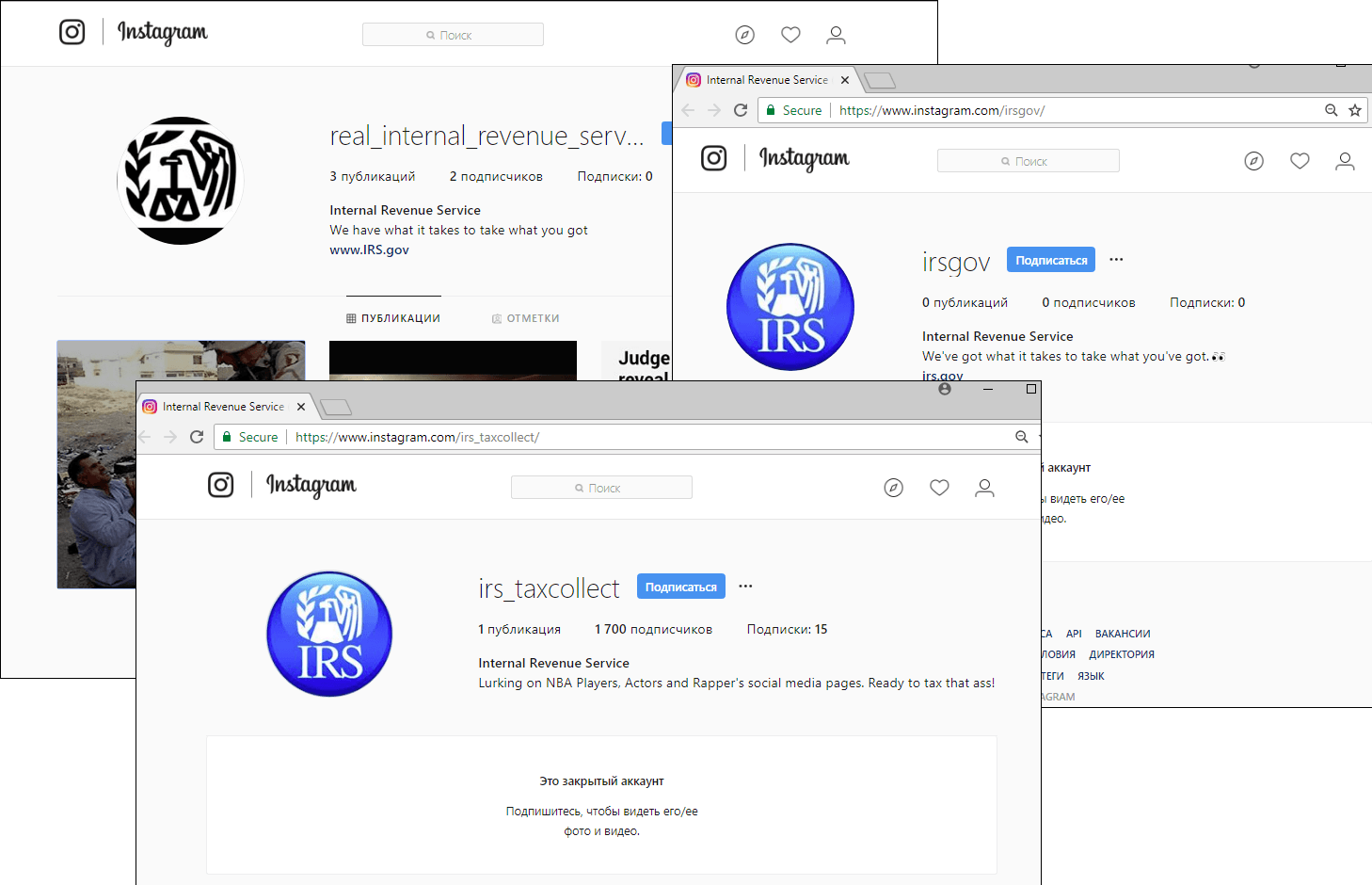
Among the social media platforms used by scammers to distribute content, Instagram warrants a special mention. Only relatively recently have cybercriminals started paying attention to it. In Q3 2018, we came across many fake US Internal Revenue Service user accounts in this social network, as well as many others purporting to be an official account of one of the most widely-used Brazilian banks.
Fake IRS accounts on Instagram
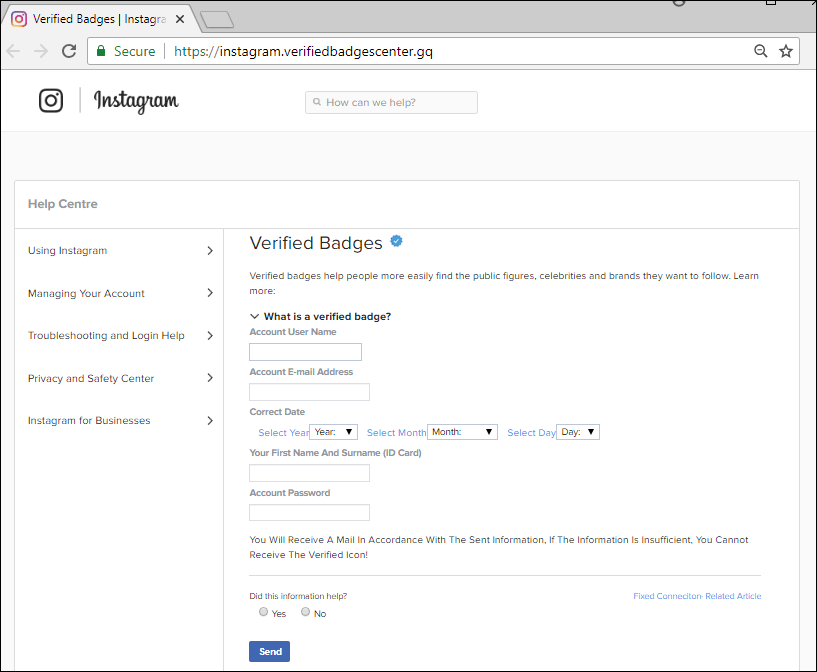
Scammers not only create fakes, but seek access to popular accounts: August this year saw a wave of account hacking sweep through the social network. We observed accounts changing owners as a result of phishing attacks with “account verification” prompts – users themselves delivered their credentials on a plate in the hope of getting the cherished blue tick.
Back when scammers offered to “verify” accounts, there was no such function in the social network: the administration itself decided whom to award the sacred “badge.” Now it is possible to apply for one through the account settings.
Statistics: spam
Proportion of spam in email traffic
This post Spam and Phishing in Q3 2018 originally appeared on Securelist.