Ransomware operator TeslaCrypt shuts down, releases master encryption key
Over the past few weeks the developers of the malicious ransomware TeslaCrypt, which would encrypt files or entire computers and hold them hostage, signaled that they were closing down operations. As time went on the project’s website slowly dismantled and payment sites began to vanish. Out of curiosity, a security researcher from ESET North America anonymously contacted the group asking if the master decryption key would be released.
Much to the researcher’s surprise, the key was made public.
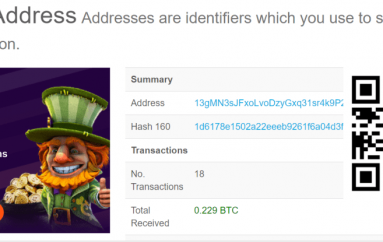
Above: The TeslaCrypt master key released on a Tor .onion website (sill publicly available at time of writing).
This has allowed ESET to release a free decrypting tool capable of unlocking files affected by all variants of the ransomware. The software is capable of decrypting every version of TeslaCrypt ransomed files up to 4.0 includes files with the extension .xxx, .ttt, .micro, .mp3 and encrypted files without an extension.
Ransomware: a dreadful scourge on the Internet
TeslaCrypt acts as a ransomware Trojan that targets computers with particular video games installed and it was originally discovered in the wild in 2015. The malware will hit and encrypt files related to the Call of Duty series, World of Warcraft,Minecraft and World of Tanks by seeking out file extensions related to these games.
Newer variants of TeslaCrypt did not focus on compter games and also focused on encrypting documents such as Word, PDF and JPG files.
Once the malware hit a user, it would prompt the victim to send $500 worth of bitcoins in order to obtain a decryption key for the files.
Although resembling CryptoLocker, an older and more common ransomware suite, TeslaCrypt shares no code with the more prominent ransomware. TeslaCrypt infects computers via the Angler Adobe Flash injection exploit. This means that users could be infected by visiting a malicious website using a vulnerable version of Flash. (Adobe Flash has been on a long, hard and slow death for some years now and is a common vector for malware to afflict computers.)
According to the FBI, victims of ransomware lost approximately $18 million from 2014 to mid 2015.
The proliferation of ransomware has become a plague on consumers and businesses alike and can have devastating effects outside of the Internet as well. Recently, remote access tool TeamViewer users became the target of ransomware, locking their computers. Worse, hospitals have become notable targets of ransomware, one example is Hollywood Presbyterian Medical Center, shut down by a ransomware attack in February; another is Kentucky’s Methodist Hospital, which found itself infected with Locky in March of this year.
This is one ransomware down; but there are many more to go.
If you have been affected by TeslaCrypt, visit the ESET support knowledgebase and follow the repair instructions.
Source | SiliconAngle