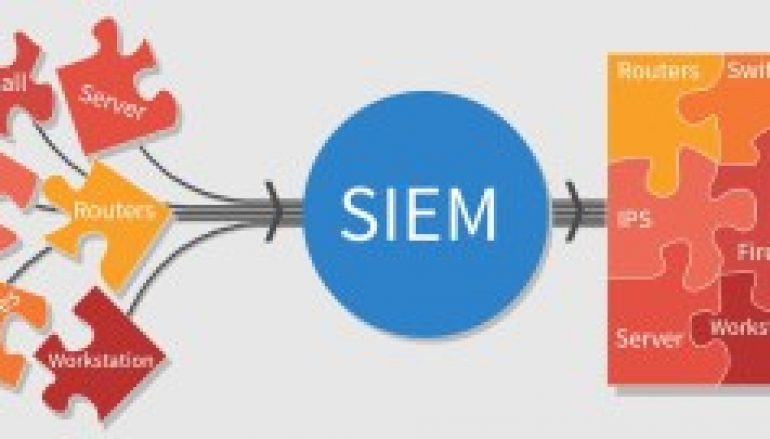
Indicator Of Attack(IoA’s) And Activities – SOC/SIEM – A Detailed Explanation
What is an Indicator of Attack (IOA)
IoA’s is some events that could reveal an active attack before indicators of compromise become visible.
Use of IoA’s provides a way to shift from reactive cleanup/recovery to a proactive mode, where attackers are disrupted and blocked before they achieve their goal such as data thief, ransomware, exploit, etc.
IOA’s focus on detecting the intent of what an attacker is trying to accomplish, regardless of the malware or exploit used in an attack. Just like AV signatures, an IOC-based detection approach cannot detect the increasing threats from malware-free intrusions and zero-day exploits. As a result, next-generation security solutions are moving to an IOA-based approach
10 Indicators of attack (IoA’s)
The following most common attack activities could have been used, individually or in combination, to diagnose an active attack:
1) Internal hosts with bad destinations
Internal hosts communicating with known bad destinations or to a foreign country where you don’t conduct business.

Example of HP ArcSight Dashboard that shows client’s hosts communicating with Feeds(IP, Domain, Url) from “ransomwaretracker.abuse.ch” website.
[Ransomware Hunter is available as free a free package included at HPE Protect724 from SOC Prime]

Example of Global Threat Intelligence from McAfee
2) Internal hosts with non-standard ports
Internal hosts communicating to external hosts using non-standard ports or protocol/port mismatches, such as sending command shells (SSH) rather than HTTP, HTTPS traffic over port 80,443, the default web port.

Example of Internal Host using 21(FTP), 445(SMB), 137(NETBIOS-NS), 135(RPC) to Internet
3) Public Servers/DMZ to Internal hosts
Publically servers or demilitarized zone (DMZ) hosts communicating to internal hosts. This allows leapfrogging from the outside to the inside and back, permitting data exfiltration and remote access to assets such as RDP(Remote Desktop Protocol), Radmin, SSH.

Example of a Report that monitor Top 10 Traffic from “DMZ” zone to “Internal/Client” Zone.
From this report, Security Analyst should investigate to Highlighted
Servers that communicating to Internal hosts via RDP(TCP/3389),
SSH(TCP/22)
4) Off-hour Malware Detection
Alerts that occur outside standard business operating hours (at night or on weekends) could signal a compromised host.

Example of IPS alerts on non-working time (Holiday)
5) Network scans by internal hosts
Network scans by internal hosts communicating with multiple hosts in a short time frame, which could reveal an attacker moving laterally within the network.
These incidents detect from Perimeter network defenses such as firewall and IPS. You must choose Zone/Interface from “Internal” to “Internal” only. For Future, you should focus form “Internal” to “DMZ” too. It may be “Insider Threat” or “Compromise hosts” that they need more information from your networks (Reconnaissance)

Example of Network Scans Report that filters from “Internal” to “Internal” zone
6) Multiple alarm events from a single host
Multiple alarm events from a single host or duplicate events across multiple machines in the same subnet over a 24-hour period, such as repeated authentication failures. THIS IS COMMON USE CASE.

Example Dashboard that monitoring “User Login Failures” from Single Hosts
Note: some login failed events form e-mail applications on mobile phones can generate events more 500 events/minute. I found this case when the password of a user account is expired but they have not changed the new password on their devices.
7) The system is reinfected with malware
After Infected host is cleaned, a system is reinfected with malware within 5-10 minutes, repeated reinfections signal the presence of a rootkit or persistent compromise. This incident may detect from Endpoint Security Protection or Anti Virus events.

This is Example Maleware Dashboard.
Detection: You must create at least 3 rules on SIEM follow as
- The rule alert when it found infected host then “Add To” Current Infected Hosts List and Historical Infected Hosts List (Store at least 1 week)
- The rule alert when malware is cleaned from infected Host then “Remove To” Current Infected Hosts List
- The rule alert when it found an infected host that is “Historical Infected Hosts List” within specific time range. THAT SYSTEMs SHOULD SCAN/INVESTIGATE MALWARE AGAIN!!!
8. Multiple Login from different regions
A user account trying to login to multiple resources within a few minutes from/to different region. This is a sign that the user’s credentials have been stolen or that a user is up to mischief.

Example of Correlated rule that Ideal solutions may vary based on your network conditions and security policy.
This rule detects from an event in the “Login” normalization category, with an Event Outcome equal “Success” with multiple Source Geo-locations, within a specified Time Range and Events are grouped by Source User.
9. Internal hosts use much SMTP
E-Mail Protocol such as SMTP (Simple Mail Transfer Protocol), POP3 or IMAP4 should be monitoring. Some malware will use this port to send information to Suspicious or Hacker’s server.

Example of Infected client that use SMTP(TCP/25)
10. Internal hosts many queries to External/Internal DNS
Many organization has Internal DNS servers for caching records and serve DNS service to internal hosts. DHCP configuration is defined as Primary DNS Server to Internal DNS server. If you found that some internal hosts query to External DNS such as 8.8.8.8, 8.8.4.4 (Google DNS), you should try scan malware on that clients.

Some Incidents found that the internal host query many requests to the internal DNS server (> 1,000 events/hour)
This post Indicator Of Attack(IoA’s) And Activities – SOC/SIEM – A Detailed Explanation originally appeared on GB Hackers.