Hackers using fake gaming torrents to launch malicious app spreading campaign
Gamers seeking pirated versions of popular video games have become the latest targets of an ongoing malware distribution campaign, which involves hackers using fake gaming torrents to lure victims and spread malicious PUAs (Potentially Unwanted Applications).
As part of the campaign, the cybercriminals use games such as World of Warcraft: Legion, The Division, Assassin’s Creed Syndicate, The Walking Dead, The Witcher 3: Wild Hunt and Just Cause 3 as baits to gamers to install the malware.
Cybersecurity firm Symantec uncovered the campaign, cautioning gamers of the dangers of installing pirated games onto their systems. The company identified several websites offering gamers pirated versions of popular games via fake torrent files, which enclosed a malicious script that attempted to automatically infect systems when installed. In efforts to dupe victims into believing its legitimacy, the file uses an icon similar to the UTorrent logo.
“On several sites, we found fake torrents with the names of popular games, such as Assassin’s Creed Syndicate or The Witcher 3, which were used as bait to trick users into silently installing PUAs on their computer,” the company said. “Symantec believes that the parties behind this campaign are attempting to fly under the radar by abusing numerous pay-per-install affiliate programs. While this campaign only spreads PUA downloaders, the same distribution model may be used to deliver additional security risks or even malware.”
A PUA is a kind of malicious software that can affect a user’s privacy and their systems’ performance and is also capable of further crippling a system’s security, thereby making it vulnerable for hackers to exploit. Symantec explains: “There are several ways that a PUA might get installed on a computer or device. It may arrive as a freeware application or be bundled with third-party software. In many cases, user consent is required, but on some occasions a more intrusive PUA may perform a silent install that escapes attention.”
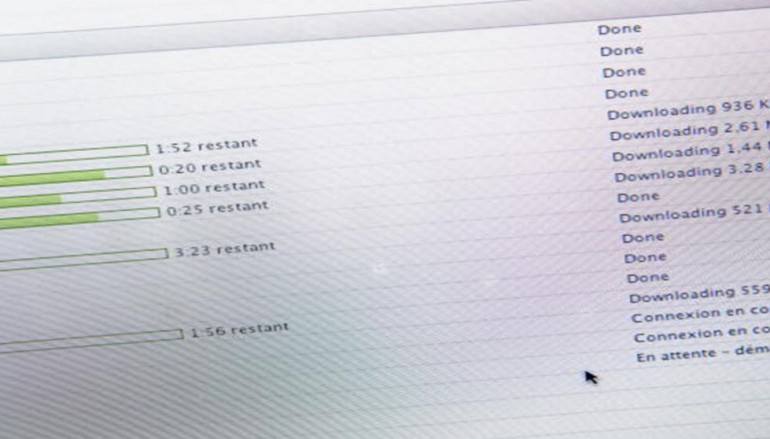
While the Windows UAC (User Access Control) system generally deters such malicious scripts from running, the hackers have specifically designed the malware to instruct users before downloading the malware, to let the script run on their systems, despite UAC’s warning. This means, if users choose to ignore the UAC alert, the malware then automatically downloads additional PUAs.
Symantec said: “The installation of additional PUA software proceeds without any user interaction and without displaying any end-user licence agreement (EULA). Symantec analysis shows the installed PUA programs may change the browser default home page, hide certain browser shortcuts, or replace existing browser shortcuts with shortcuts to third-party browsers containing advertisements.”
Source | IBTimes





