Experts Collect More Evidence That Link Op ‘Sharpshooter’ to North Korea
Security experts at McAfee analyzed the code of a C2 server involved in the cyber espionage campaign tracked as Op. Sharpshooter and linked it with the North Korea-linked APT group
McAfee worked with a government entity and discovered that the
Op. Sharpshooter is much more extended and more complex than initially thought.
“McAfee today revealed evidence that the Operation Sharpshooter campaign exposed in 2018 is more extensive in complexity, scope and duration of operations.” reads the press release published by the company.
“The analysis led to identification of multiple previously unknown command-and-control centers, and suggest that Sharpshooter began as early as September 2017, targeted a broader set of organizations, in more industries and countries and is currently ongoing.”
In Decembed 2018, security experts at McAfee uncovered a hacking campaign, tracked as Operation Sharpshooter, aimed at infrastructure companies worldwide. The threat actors are using malware associated with Lazarus APT group that carried out Sony Pictures attack back in 2014.
The campaign targeted nuclear, defense, energy, and financial companies, experts believe attackers are gather intelligence to prepare future attacks.
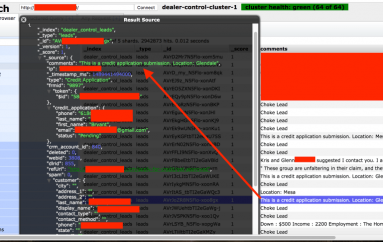
“In October and November 2018, the Rising Sun implant has appeared in 87 organizations across the globe, predominantly in the United States, based on McAfee telemetry and our analysis.” reads the analysis published by McAfee.
“Based on other campaigns with similar behavior, most of the targeted organizations are English speaking or have an English-speaking regional office. This actor has used recruiting as a lure to collect information about targeted individuals of interest or organizations that manage data related to the industries of interest.”

Threat actors carried out spear phishing attacks with a link poining to weaponized Word documents purporting to be sent by a job recruiter. The messages are in English and include descriptions for jobs at unknown companies, URLs associated with the documents belongs to a US-based IP address and to the Dropbox service.
The macros included in the malicious document uses an embedded shellcode to inject the Sharpshooter downloader into Word’s memory.
Attackers attempted to hide their identity through the use of the ExpressVPN service that showed connections to the web shell (Notice.php) that was discovered on a compromised server coming from two IP addresses in London.
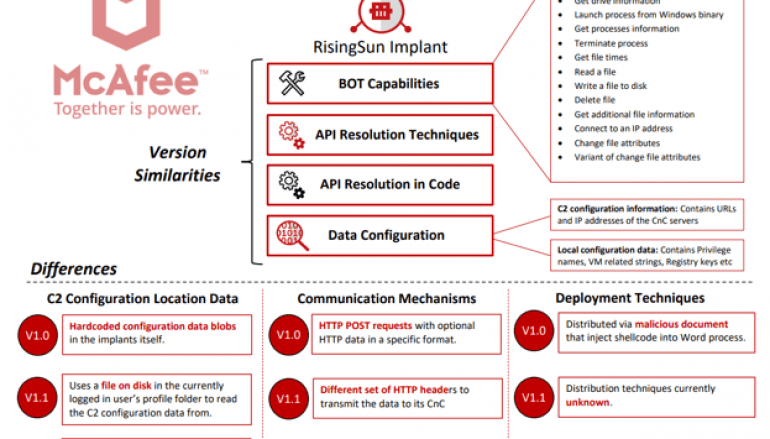
The experts observed threat actors using three different variants of the
Rising Sun backdoor (v1.0, v1.1, and v2.0), a circumstance that confirms the evolution from the Duuzer Trojan that was used by Lazarus APT in attacks against the South Korean organizations.
Experts noticed that backdoor used by the attackers that is similar to versions of the Rising Sun implant dating back to 2017 and has the source code borrowed from Lazarus’s Duuzer Trojan.

“These [Rising Sun] implants were all based on the original Backdoor Duuzer source code,” reads the report published by the experts.
Other similarities in the TTPs of the adversaries are the use of the fake job recruitment campaigns and the use of similar versions of Rising Sun backdoor.
Experts found evidence that variants of the Rising Sun backdoor were used by the attackers since at least 2016.
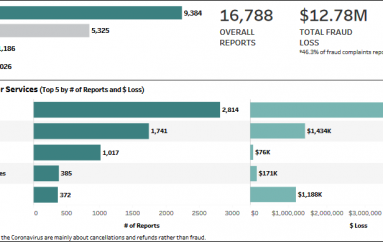
The analysis of the c2 allowed the experts to determine that the largest number of recent attacks primarily target Germany, Turkey, the United Kingdom and the United States. Previous attacks were focused on entities in telco, government and financial industr, primarily in the United States, Switzerland, and Israel, and others.
Experts also discovered a set of unobfuscated connections from IP addresses in Windhoek, a city in Namibia, Africa. Researchers argue that attackers use the region to make some tests or that attackers run the operation from this are. However, experts cannot exclude that this is a false flag to deceive researchers.
Key findings shared by McAfee are:
- Hunting and spearphishing. Operation Sharpshooter shares multiple design and tactical overlaps with several campaigns, for example a very similar fake job recruitment campaign conducted in 2017 that the industry attributes to Lazarus Group.
- African connection. Analysis of the command-and-control server code and file logs also uncovered a network block of IP addresses originating from the city of Windhoek, located in the African nation of Namibia. This led McAfee Advanced Threat Research analysts to suspect that the actors behind Sharpshooter may have tested their implants and other techniques in this area of the world prior to launching their broader campaign of attacks.
- Maintaining access to assets. The attackers have been using a command-and-control infrastructure with the core backend written in Hypertext Preprocessor (PHP) and Active Server Pages (ASP). The code appears to be custom and unique to the group and McAfee’s analysis reveals it has been part of their operations since 2017.
- Evolving Rising Sun. The Sharpshooter attackers used a factory-like process where various malicious components that make up Rising Sun have been developed independently outside of the core implant functionality. These components appear in various implants dating back to 2016, which is one indication that the attackers have access to a set of developed functionalities at their disposal.
The researchers will present their findings at the RSA security conference.
This post Experts Collect More Evidence That Link Op ‘Sharpshooter’ to North Korea originally appeared on Security Affairs.