Advanced Persistent Threat (APT):
An attack in which an unauthorized actor, often a nationstate,employs highly sophisticated technology and/or tactics to gain and maintain surreptitious access to a network. The intention of an APT may be to steal data, or to cause damage to the network or organization, or to plant attack capabilities for future activation. Stuxnet is an example of an ATP.
Adware
A software package that automatically plays, displays or downloads advertising material to a computer after the software is installed on it or while the application is being used
Application layer
In the Open Systems Interconnection (OSI) communications model, the application layer provides services for an application program to ensure that effective communication with another application program in a network is possible.
Authentication
Procedures to verify that a network user is who he or she claims to be. A simple and common authentication procedure is a password. “Two-factor” authentication is the use of two independent forms of authentication, such as a password, a fingerprint, or a series of digits generated by a secure identification token, a small handheld device.
Analog
A transmission signal that varies continuously in amplitude and time and is generated in wave formation
Scope Note: Analog signals are used in telecommunications
Asset
Something of either tangible or intangible value that is worth protecting, including people, information, infrastructure, finances and reputation
Asymmetric key (public key)
A cipher technique in which different cryptographic keys are used to encrypt and decrypt a message
Authenticity
Authenticity is assurance that a message, transaction, or other exchange of information is from the source it claims to be from. Authenticity involves proof of identity.
Availability
Ensuring timely and reliable access to and use of information
Botnet
A network of computers that have been penetrated, compromised, and programmed to operate on the commands of an unauthorized remote user, usually without the knowledge of their owners or operators. The network of “robot” computers can then be manipulated by the remote actor to commit attacks on other systems. The computers on botnets are frequently referred to as “zombies” and are often employed in digital denial of service attacks.
Bring your own device (BYOD)
An enterprise policy used to permit partial or full integration of user-owned mobile devices for business
purposes
Brute force
A class of algorithms that repeatedly try all possible combinations until a solution is found.
Brute force attack
Repeatedly trying all possible combinations of passwords or encryption keys until the correct one is found
Buffer overflow
Occurs when a program or process tries to store more data in a buffer (temporary data storage area) than it was intended to hold
Scope Note: Since buffers are created to contain a finite amount of data, the extra information—which has to go somewhere—can overflow into adjacent buffers, corrupting or overwriting the valid data held in them.
Although it may occur accidentally through programming error, buffer overflow is an increasingly common type of security attack on data integrity. In buffer overflow attacks, the extra data may contain codes designed to trigger specific actions, in effect sending new instructions to the attacked computer that could, for example, damage the user’s files, change data, or disclose confidential information. Buffer overflow attacks are said to have arisen because the C programming language supplied the framework, and poor programming practices supplied the vulnerability
Certificate (Certification) authority (CA)
A trusted third party that serves authentication infrastructures or enterprises and registers entities and issues them certificates
Chief Information Security Officer (CISO)
The person in charge of information security within the enterprise
Continuous Monitoring
A continuous monitoring program is a process designed to regularly assess information systems to determine if the complete set of planned, required, and deployed security controls within an information system continue to be effective over time, as changes in the system occur. Continuous monitoring transforms the traditional model of static, sporadic security compliance assessments to dynamic, near-real-time situational awareness.
Cipher
An algorithm to perform encryption
Ciphertext
Information generated by an encryption algorithm to protect the plaintext and that is unintelligible to the unauthorized reader.
Compliance
Adherence to, and the ability to demonstrate adherence to, mandated requirements defined by laws and regulations, as well as voluntary requirements resulting from contractual obligations and internal policies
Computer emergency response team (CERT)
A group of people integrated at the enterprise with clear lines of reporting and responsibilities for standby support in case of an information systems emergency . This group will act as an efficient corrective control, and should also act as a single point of contact for all incidents and issues related to information systems
Critical Infrastructure
The PATRIOT Act defines critical infrastructure as systems and assets,
whether physical or virtual, so vital to the United States that the incapacity or destruction of such systems and assets would have a debilitating impact on security, national economic security,national public health or safety, or any combination of those matters. The Department of Homeland Security currently identifies 18 critical infrastructure sectors, including transportation, electricity, financial services, and nuclear power. Most critical infrastructure entities are dependent upon computer networks and therefore vulnerable to cyberattacks.
Confidentiality
Preserving authorized restrictions on access and disclosure, including means for protecting privacy and proprietary information
Containment
Actions taken to limit exposure after an incident has been identified and confirmed
Cybercrime
Cybercrime is criminal activity conducted using computers and the Internet, often financially motivated. Cybercrime includes identity theft, fraud, and internet scams, among other activities. Cybercrime is distinguished from other forms of malicious cyber activity, which have political, military, or espionage motivations.
Digital Denial of Service (DDOS)
A cyber war technique in which an Internet site, a server, or a router is flooded with more requests for data than the site or device can respond to or process. Consequently, legitimate traffic cannot access the site and the site is in effect shut down. Botnets are used to conduct such attacks, thus distributing the attack over thousands of originating computers acting in unison.
Encryption
The scrambling of information so that it is unreadable to those who do not have the code to unscramble it.
Hack
A verb meaning to gain unauthorized access into a computer system.
Hacker
Someone who uses skills to gain access to a computer or network without
authorization.
Hacktivism
The exploitation of computers and computer networks as a means of protest to
promote political ends. The anti-secrecy group Anonymous is an example of a hacktivist organization.
Hardware
Refers to the machines, wiring, and other physical components of a computer, network, or other information technology system.
Internet Service Provider (ISP)
A corporation (or government agency) that provides the wired or wireless connectivity from a user’s home, office, or mobile computer to the Internet.
Keystroke Logger
A program or device that captures every key depression on the computer. Cybercriminals install them on computers to clandestinely record the computer user’s passwords and other confidential information.
Logic Bomb
A software application or series of instructions that cause a system or network to shut down and/or to erase all data or software on the network. A logic bomb is a type of malware.
Malware
Malicious software that compromises or reprograms computers or networks with the intention of disrupting their intended functions or operations. Examples of malware include logic bombs, worms, viruses, Trojan Horses, and keystroke loggers.
Obfuscation
The deliberate act of creating source or machine code that is difficult for humans to understand
Open Systems Interconnect (OSI) model
A model for the design of a network. The open systems interconnect (OSI) model defines groups of functionality required to network computers into layers. Each layer implements a standard protocol to implement its functionality. There are seven layers in the OSI model.
Open Web Application Security Project (OWASP)
An open community dedicated to enabling organizations to conceive, develop, acquire, operate, and maintain applications that can be trusted
Payload
The section of fundamental data in a transmission. In malicious software this refers to the section containing the harmful data/code.
Penetration testing
A live test of the effectiveness of security defenses through mimicking the actions of real-life attackers
Pharming
A technique used by hackers to redirect users to false websites without their
knowledge.
Phishing
A socially-engineered attempt by malicious actors to deceive internet users into providing personal information such as usernames, passwords, social security numbers and credit card details. Common phishing tactics include posing as a known contact, a legitimate company, or an otherwise trusted entity in an electronic communication.
Port (Port number)
A process or application-specific software element serving as a communication endpoint for the Transport Layer IP protocols (UDP and TCP)
Port scanning
The act of probing a system to identify open ports
Privacy
Freedom from unauthorized intrusion or disclosure of information about an individual
Protocol
The rules by which a network operates and controls the flow and priority of transmissions
Proxy server
A server that acts on behalf of a user
Ransomware
A type of malicious software from cryptovirology that threatens to publish the victim’s data or perpetually block access to it unless a ransom is paid
Residual risk
The remaining risk after management has implemented a risk response
Risk
The combination of the probability of an event and its consequence. (ISO/IEC 73)
Resilience
The ability of a system or network to resist failure or to recover quickly from any disruption, usually with minimal recognizable effect
Risk assessment
A process used to identify and evaluate risk and its potential effects
Risk assessments are also used to manage the project delivery and project benefit risk.
Rootkit
A software suite designed to aid an intruder in gaining unauthorized administrative access to a computer system
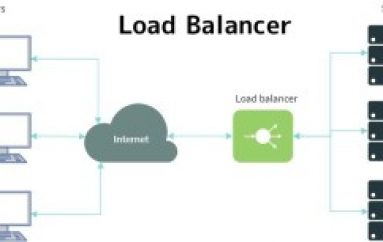
Router
Routers are computer hardware that direct the movement of internet data, ensuring that the data, such as emails or website requests, reaches its intended destination. Routers are a type of server.
RSA
A public key cryptosystem developed by R. Rivest, A. Shamir and L. Adleman used for both encryption and digital signatures
SCADA
SCADA stands for supervisory control and data acquisition. It generally refers to an industrial control system, which is an automated system used to control industrial processes,such as regulation of electrical power transmission, wastewater treatment, or chemical mixing.
Server
A computer that is programmed to provide services – such as hosting software platforms,databases, or websites – to other computers and computer users.
Typically, servers are designed to be automated, operating without constant human monitoring.
Simple Mail Transfer Protocol (SMTP)
The standard electronic mail (e-mail) protocol on the Internet
Software
Refers to the programs and other operating information used by a computer. Software programs provide the instructions that direct computers what to do and how to do it.
Secure Shell (SSH)
Network protocol that uses cryptography to secure communication, remote command line login and remote command execution between two networked computers
Secure Sockets Layer(SSL)
A protocol that is used to transmit private documents through the Internet
Symmetric key encryption
System in which a different key (or set of keys) is used by each pair of trading partners to ensure that no one else can read their messages
SQL injection
Results from failure of the application to appropriately validate input. When specially crafted user-controlled input consisting of SQL syntax is used without proper validation as part of SQL queries, it is possible to glean
information from the database in ways not envisaged during application design.(MITRE)
Telnet
Network protocol used to enable remote access to a server computer
Threat
Anything (e.g., object, substance, human) that is capable of acting against an asset in a manner that can result in harm
Transmission Control Protocol (TCP)
A connection-based Internet protocol that supports reliable data transfer connections
Transport Layer Security (TLS)
A protocol that provides communications privacy over the Internet. The protocol allows client/server applications to communicate in a way that is designed to prevent eavesdropping, tampering, or message forgery. (RFC 2246)
Trapdoor /Trojan/Trojan Horse
A type of malware added to a program to facilitate future
unauthorized entry into a network or into the software program. Often after an initial entry, the perpetrators will leave behind a trapdoor that will permit future access to be faster and easier.
Triple DES (3DES)
A block cipher created from the Data Encryption Standard (DES) cipher by using it three times
Virtualization
The process of adding a “guest application” and data onto a “virtual server,” recognizing that the guest application will ultimately part company from this physical server
Virus
A program with the ability to reproduce by modifying other programs to include a copy of itself
Vulnerability scanning
An automated process to proactively identify security weaknesses in a network or individual system
Voice-over Internet Protocol (VoIP)
Also called IP Telephony, Internet Telephony and Broadband Phone, a technology that makes it possible to have a voice conversation over the Internet or over any dedicated Internet Protocol (IP) network instead of over dedicated voice transmission lines
Web server
Using the client-server model and the World Wide Web’s HyperText Transfer Protocol (HTTP), Web Server is a software program that serves web pages to users.
Wi-Fi protected access (WAP)
A class of systems used to secure wireless (Wi-Fi) computer networks.
Wireless local area network (WLAN)
Two or more systems networked using a wireless distribution method
Worm
A programmed network attack in which a self-replicating program does not attach itself to programs, but rather spreads independently of users’ action
Zero-day Attack
A cyberattack that uses previously unknown coding (malware, etc.) or exploits a previously unknown security vulnerability. This type of attack is particularly dangerous because existing patches, anti-virus software, and other defenses are not programmed to defend against it. It is called a zero-day attack, because it occurs on “day zero” of learning of the vulnerability.