Checking in with spear phishing, criminals check out with hotel credit card data
Hotel chains focus on hospitality, but their security practices have made them entirely too hospitable a target for data theft. Hotels have been brutalized over the past year by a wave of point-of-sale system breaches that have exposed hundreds of thousands of guests’ credit card accounts. And those attacks, as a recent episode described by Panda Security’s Luis Corrons demonstrates, have become increasingly targeted—in some cases using “spear-phishing” e-mails and malware crafted specifically for the target to gain access to hotels’ networks.
In one incident that was uncovered recently, the target “was a small luxury hotel chain,” Corrons told Ars. “We discovered the attack, and it was really customized for the specific hotel. This was 100 percent tailored to the specific target.”
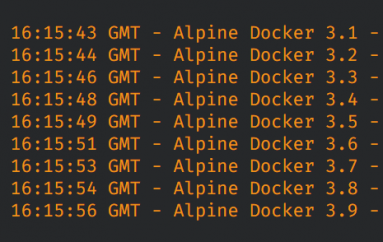
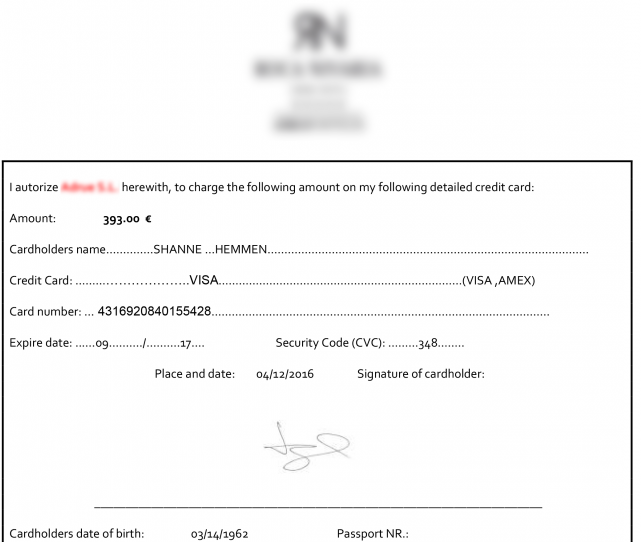
The attackers used a Word document from the hotel itself—one frequently used by the hotel to allow customers to authorize credit card charges in advance of a stay. The document was actually enclosed as part of a self-extracting file, which also installed two other files on the target machine—one of them an installer for backdoor malware named “adobeUpd.dll” to disguise it and the other a Windows .cmd batch script that both opens the Word document and launches the backdoor.
Because of the custom nature of the malware, it was not caught by antivirus software. And to avoid detection of its activity, the command and control server for the malware used a domain name almost identical to that of the hotel’s own domain—other than the fact that it was a domain registered as part of Gabon’s top-level domain (.ga). “If you check logs, if you see something connecting to a domain that has the name of your company, you may not realize anything is going on.” Corrons explained.
The level of customization is evidence of at least some deeper intelligence gathering and reconnaissance by the attackers in advance of the phishing attack. The document used isn’t published on the website of the hotel and is usually sent out only after a customer contacts the hotel to request it, Corrons said. The attackers may have also probed to find out which antivirus software the hotel used to make sure their malware package didn’t trigger alerts.
Checkout time
These types of attacks, Corrons told Ars, are the work of gangs that have specialized in stealing credit card data from point of sale systems. “Hotels are a gold mine” for credit card theft, he said. And while they have lots of other data, including customer personal information, that might be valuable, the network breaches pulled off by the attackers who hit chains such as Hilton, Mandarin Oriental, Trump Hotels, White Lodging, Starwood, Hyatt, and Hard Rock Las Vegas focused entirely on credit card transaction data—the data most easily monetized.
While the chains affected in these attacks have not publicly detailed how the breaches took place, Corrons said that attacks seen by Panda’s Adaptive Defense 360 service were predominantly via e-mails targeted at hotel employees. “It’s probably the easiest way to get in,” he explained. “You only need to get your hands in one computer, and once you’ve compromised that computer it’s not that difficult to move laterally within the network.”
That’s because, like many businesses, hotels often do little to segment their networks. Those who have poked around a little on hotel Internet access know that many hotel chains—especially smaller ones—lack any division of their networks, with systems often easily identifiable simply by browsing the network’s advertised systems. “That happens everywhere, not just in hotels,” Corrons noted. “I have been in some retail hubs where they have free Wi-Fi, and [when you connect] you have access to everything. Even the [network] names of everything show this is a point of sale system and that is a server.” And while some of the larger hotels have better security teams, Corrons noted, “the smaller ones don’t even have a security team in place.”
Source | ARSTechnica