APT Group Targets High Profile Networks in Central Asia
Security firms have foiled an advanced cyber espionage campaign carried out by Chinese APT and aimed at infiltrating a governmental institution and two companies.
Antivirus firms have uncovered and foiled an advanced cyber espionage campaign aimed at a governmental institution and two companies in the telecommunications and gas sector.
The level of sophistication of the attack and the nature of targets suggests the involvement of an advanced persisten threat, likely from China, focused on cyber espionage activity in Central Asia.
Attackers used multiple commodity malware and previously unknown backdoors in the attacks, the analysis of their code suggests a possible link with multiple campaigns uncovered over several years.
Most of the C2 used by the attackers are hosted by the provider Choopa, LLC, and threat actors made large use of Gh0st RAT, a malware attributed to China-linked cyber espionage groups.
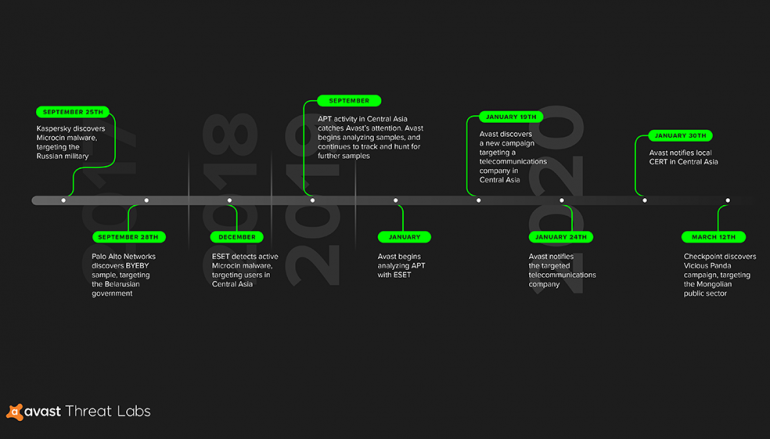
The security firm ESET and Avast first detected the attacks since September and January respectively. The researchers identified a host used as a repository containing hacking tools and backdoors, whose code has many similarities with malware previously associated with China-linked APT groups.
“The samples we analyzed contain links to malware samples and campaigns, such as Microcin, BYEBY, and Vicious Panda, previously described by Kaspersky, Palo Alto Networks, and Check Point, respectively. The backdoors we found are custom tools that have not previously been analyzed, as far as we know.” reads a report published by Avast. “The majority of the C&C servers are registered to Choopa, LLC, a hosting platform that has been used by cybercriminals in the past.”
Below a timeline of the attacks that appeared to be associated with the same threat actor.

“An APT group, which we believe could possibly be from China, planted backdoors to gain long-term access to corporate networks. Based on our analysis, we suspect the group was also behind attacks active in Mongolia, Russia, and Belarus.” continues Avast.
Researchers from ESET that investigared into the attacks discovered three backdoors that collectively tracked as Mikroceen. The backdoors allowed the threat actors to manage the target file system, establish a remote shell, take screenshots, manage services and processes, and run console commands.
Below the list of backdoors published by ESET:
- sqllauncher.dll (VMProtected backdoor)
- logon.dll (VMProtected backdoor)
- logsupport.dll (VMProtected backdoor)
Both “sqllauncher.dll” and “logon.dll” run as services and use the same C2 infrastructure, experts noticed that all of them feature protection against reverse engineering. Two of them, “sqllauncher.dll” and “logon.dll,” run as services and use the same C2 server.
Attackers use a version of the Mimikatz post-exploitation tool and rely on Windows Management Instrumentation (WMI) for lateral movement.
“Avast reported its findings to the local CERT team and reached out to the telecommunications company. We have not heard back from either organization.” concluded Avast.
“Avast has recently protected users in Central Asia from further attacks using the samples we analyzed.”
Both Avast and ESET have published a list of indicators of compromise (IoC) for the above threats.
This post APT Group Targets High Profile Networks in Central Asia originally appeared on Security Affairs.