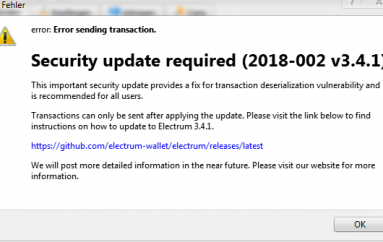
ADOBE DOLES OUT SECOND ROUND OF HIGHER PRIORITY PATCHES
A week after issuing updates on Patch Tuesday, Adobe has posted patches for a second slew of 24 critical vulnerabilities, which have a higher risk of being exploited.
This week’s crop of vulnerabilities, of which there were 47 overall, impact versions of Adobe’s Acrobat DC Acrobat Reader DC, and Photoshop CC, all for both Windows and MacOS.
While last week’s fixes were assigned a severity rating of priority 2, this week’s patches have been assigned a priority 1 rating, indicating that the vulnerabilities are more likely to be used in real-world attacks.
“This update resolves vulnerabilities being targeted, or which have a higher risk of being targeted, by exploit(s) in the wild for a given product version and platform. Adobe recommends administrators install the update as soon as possible,” Adobe said in a description of the priority 1 severity ratings.
The company added that it “is not aware of any exploits in the wild for any of the issues addressed in these updates.”
The security updates for Adobe Acrobat and Reader include several critical vulnerabilities that could lead to arbitrary code execution. Of these, 13 are listed as use-after-free, and seven are listed as heap overflow flaws.
“The most serious of these vulnerabilities, CVE-2018-4946 and CVE-2018-4947 (both reported by Cisco Talos), can allow an attacker to execute arbitrary code on a victim’s system,” Allan Liska, threat intelligence analyst at Recorded Future, told Threatpost. “The vulnerability allows an attacker to embed malicious JavaScript into the PDF file that manipulates memory on the victim system to execute the code. This attack works whether the PDF is executed locally or accessed via website.”
The remainder of the Acrobat/Reader vulnerabilities in the update include a double free vulnerability, an out-of-bounds write, a type confusion vulnerability and an untrusted pointer dereference. Additional flaws include security bypass and information disclosure issues, which are rated “important”.
Impacted versions include 2018.011.20038 and earlier versions of Acrobat DC and Acrobat Reader DC; as well as 2017.011.30079 and earlier versions of both Acrobat 2017 and Acrobat Reader 2017.
Also, 2015.006.30417 and earlier versions of Acrobat DC (Classic 2015) for Windows and MacOS, and Acrobat Reader DC (Classic 2015) for Windows and MacOS are impacted.
Read more
Source | threatpost