Archive
Kaiten Malware Returns to Threaten IoT
Kaiten, an Internet Relay Chat (IRC)-controlled malware typically used to carry out distributed denial-of-service (DDoS) attacks, has returned, in a stronger configuration. It’s targeting routers and internet of things (IoT) devices. ESET researchers have identified three tougher versions of the
A 16-year-old hacker exploited vulnerability in Steam and went on to publish his 45-second-long ‘game’ onto Steam without a single person at Valve setting eyes on it. Ruby Nealon, who created the game called Watch Paint Dry, is a game about
FBI resists call to reveal Tor hacking secrets
The FBI is resisting calls to reveal how it identified people who used a child pornography site on the Tor anonymising network. The agency was ordered to share details by a Judge presiding over a case involving one alleged user
‘Father of Car Hacking’ awarded for research
The “Father of Car Hacking” was just announced the winner of the 2015 ACM-Infosys Foundation Award, but the first step on the path that lead here started several years ago. University of California – San Diego (UCSD) professor Stefan Savage
A hacker’s next target is just a Web search away
“Google dorking.” It sounds goofy, but it could be just the ticket for a hacker looking to stir mayhem. The search technique is one of several methods that bad guys can use to find vulnerable computer systems and trace them
According to The Register, a UK-based news site about tech security and related issues, “hackers infiltrated a water utility’s control system and changed the levels of chemicals being used to treat tap water.” The hackers had “ties to Syria,” and
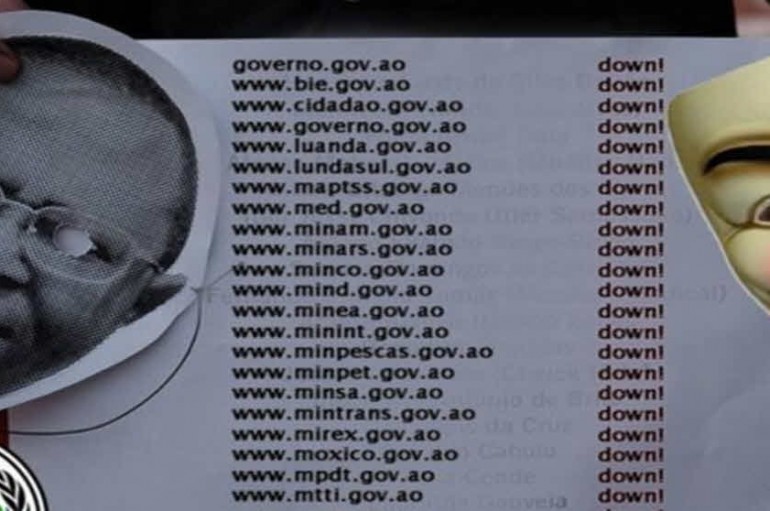
The hacking collective Anonymous says it has shut down more than 20 Angolan government websites in response to the jailing of 17 youth activists. Many of the sites were still down 20 hours after the Portuguese branch of the group
No need for stocking masks and sawn-off shotguns. The unprecedented heist of $81 million from the U.S. account of Bangladesh’s central bank is the latest among increasingly large thefts by criminals who have leveraged the speed and anonymity of hacking
Microsoft’s president and chief legal officer Brad Smith wants to let the politicians decide, when it comes to the tricky balance between privacy, security and technology. Speaking at the opening ceremony of RightsCon in San Francisco, Smith trod a careful
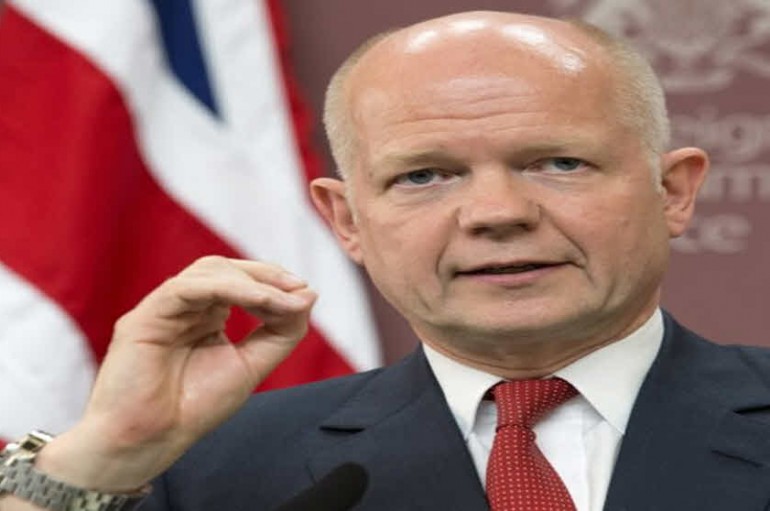
Brussels attack: Encryption and Snowden to blame for intelligence failures claims William Hague
Former UK Foreign Secretary William Hague has claimed that recent terrorist atrocities in Brussels show ‘the need to crack’ terrorist communications, citing strong encryption and the Edward Snowden leaks as contributing factors to ongoing intelligence failures across the globe. “Because
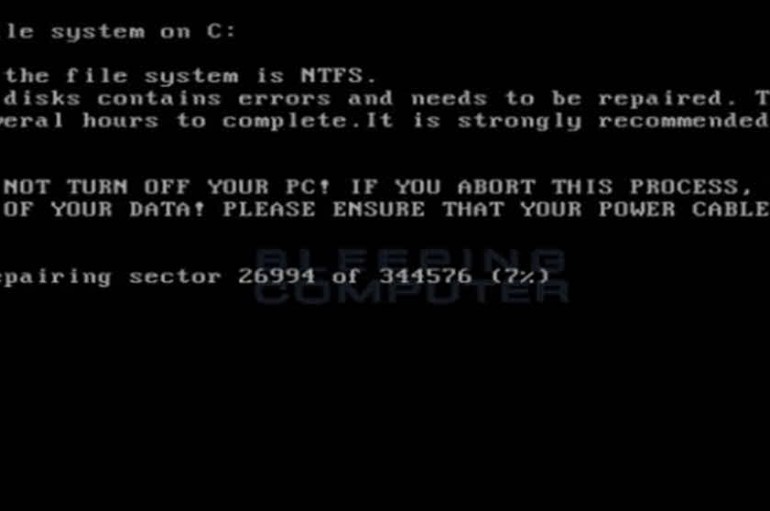
Encryption can be used to secure your personal communication from prying eyes, keep your banking details secure, and plenty of other great things. However, it’s also the key to an increasingly common form of malware called ransomware. When a computer
Senator Ron Wyden (D-OR) has put out a call to arms to digital rights activists, asking them to join in a SOPA-style effort to defeat upcoming efforts to weaken encryption. In a wide-ranging speech that covered J Edgar Hoover, Miranda
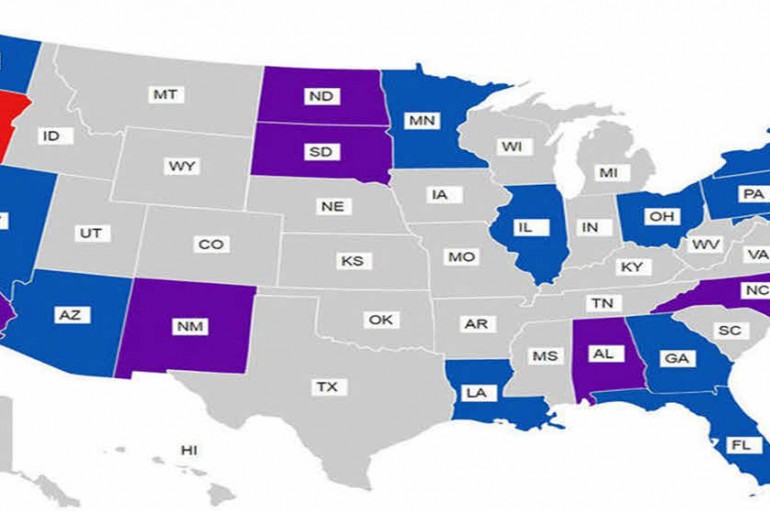
The American Civil Liberties Union (ACLU) has identified 63 cases in which the government has sought a court order demanding Apple or Google access to devices during investigations. A range of government departments filed requests with the courts, including the
The US government has used the same legal tactic it deployed in its encryption fight with Apple in more than 60 other phone-unlocking cases, according to a tally by a privacy watchdog, including other iPhones and devices running Google’s Android
BRUNSWICK, Maine (AP) – A computer hacking operation has tried to trick three Maine school departments into handing over employees’ personal tax information. The Portland Press Herald (http://bit.ly/1MAO82J ) reports the hacker or hackers posed as a district superintendent and
Hackers broke into the computer networks of some big U.S. law firms, including Cravath Swaine & Moore LLP and Weil Gotshal & Manges LLP, the Wall Street Journal reported on Tuesday. Federal investigators are looking to see if confidential information