Sorebrect- A Fileless Ransomware
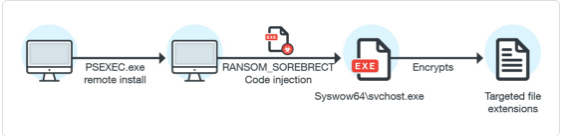
A new ransomware malware has been discovered by Trend Micro. The ransomware incorporates the characteristics of fileless and was discovered from attacks in the systems and the networks of Middle East. Sorebrect is the name of the ransomware that abuses PxExec utility and can leverage the ransomwares code injection capability.
Characteristics
The ransomware is a fileless threat because it has a self-destruct routine. Sorebrect injects its code into a legitimate system process before self-destructing its main binary. It also deletes the affected systems event logs and other files that can provide forensic information about the attack such as timestamps. Manipulating and deleting system files makes the ransomware untraceable.
Organizations in the Middle East such as Kuwait and Lebanon were the first victims of the ransomware but the ransomware has also been spotted in Canada, China, Croatia, Italy, Japan, Mexico, Russia, Taiwan and the U.S.
Sorebrect attacks PsExec, a command-line utility used by administrators to run executable files on remote systems. For PsExec to be abused, the administrator credentials are required and since it can easily attack PsExec, we must assume that the credentials are already abused by the attacker. The utility is further abused by making sure that it performs code injection into other systems. After injecting the code into a legitimate Windows process, it self-destructs while the process executes the payload.
Sorebrect also makes sure that the system event logs are deleted by abusing wevttil.exe and vssadmin to delete shadow copies. It uses Tor network protocol to anonymize its connection to its C&C server.
Best practices for securing systems
- Restricting user write permissions
- Limiting the leverage for PsExec – Only system administrators can run them
- Keeping your system and network up-to-date
- Backing up data regularly
- Adiot a cyber security-aware workforce
- Deploy multilayered security mechanisms
Source: http://blog.trendmicro.com/trendlabs-security-intelligence/analyzing-fileless-code-injecting-sorebrect-ransomware/