There is no doubt that WannaCry, a ransomware that exploits a zero-day vulnerability shook the world. Everyone was on alert to make sure that do not partake in the infection rate. Imagine what could potentially happen if 20 percent of world corporate networks were compromised. It has occurred. Fireball is a recent Chinese threat operation going viral around the globe. In fact, Rafotech, the company held responsible for Fireball, may have the facility to cause a “global catastrophe”.

Fireball: Chaos Around the World
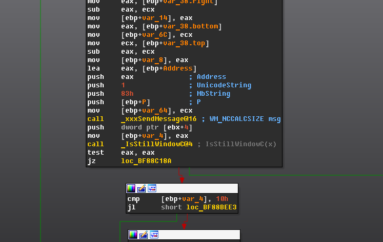
Fireball Infograph
Functionality of Fireball:
According to checkpoint threat intelligence research team who first discovered the malware, Fireball has two main capabilities:
1. Execute any code remotely on the victim (includes the downloading of files and malware)
2. Manipulation of web browsers
The malware’s apparent purpose is to generate ad revenue. However, its capabilities have the ability to expand beyond profit purposes. A substantial digital marketing agency, Rafotech, is using Fireball in order to manipulate victims’ browsers by replacing their default search engines and homepage with a fake one that has the ability to redirect queries to google.com. These fake engines entail tracking pixels that are used to collect private information. In effect, users could be spied on, redirected to malicious websites, malware can be dropped, and malicious code could potentially be executed.
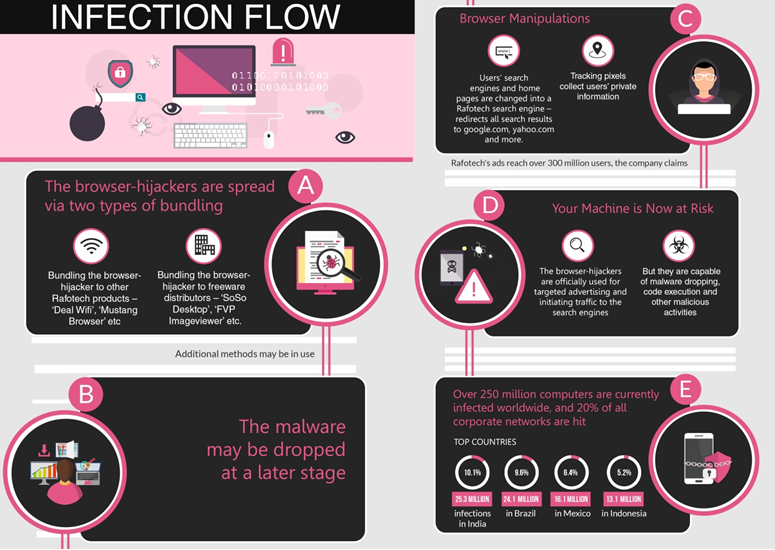
Fireball Infection Map
Spreading Fireball:So how does it spread? It usually comes with a software bundle without prior knowledge of the user. Fireball has been identified to generally spread in two ways:
1. Bundling with freeware such as FVP Imageviewer and Soso Desktop
2. Bundling to other Rafotech Products such as Mustang Browser and Deal Wi-Fi
Target of Fireball:
1. Estimated infection is 250 million computers
2. 20 percent of all corporate networks
3. Highest infections are India (10.1% — 25.3 million) and Brazil (9.6% — 24.1 million)
4. Highest hit rates are Indonesia (60%), India (43%), and Brazil (38%). U.S. and China have alerting hit rates of 10.7% and 4.7%.
There has not been any significant impact on the Middle East Region although infections did occur in the region.
Detecting Fireball:
1. Check if your homepage on your browser is yours
2. Check if you have the ability to modify your browser’s homepage
3. Check your default search engine and whether or not you can modify it as well
4. Check if you remember installing all of your browser extensions
Failing to comply with any the above means that you could potentially be affected.
Removing Fireball:
In short, an adware cleaner software may do the job. You can also uninstall the corresponding application from your OS in addition to resetting or restoring your browser configurations to their defaults.
Mcafee products and Blue Vector are able to detect Fireball.
C&C addresses
- attirerpage[.]com
- s2s[.]rafotech[.]com
- trotux[.]com
- startpageing123[.]com
- funcionapage[.]com
- universalsearches[.]com
- thewebanswers[.]com
- nicesearches[.]com
- youndoo[.]com
- giqepofa[.]com
- mustang-browser[.]com
- forestbrowser[.]com
- luckysearch123[.]com
- ooxxsearch[.]com
- search2000s[.]com
- walasearch[.]com
- hohosearch[.]com
- yessearches[.]com
- d3l4qa0kmel7is[.]cloudfront[.]net
- d5ou3dytze6uf[.]cloudfront[.]net
- d1vh0xkmncek4z[.]cloudfront[.]net
- d26r15y2ken1t9[.]cloudfront[.]net
- d11eq81k50lwgi[.]cloudfront[.]net
- ddyv8sl7ewq1w[.]cloudfront[.]net
- d3i1asoswufp5k[.]cloudfront[.]net
- dc44qjwal3p07[.]cloudfront[.]net
- dv2m1uumnsgtu[.]cloudfront[.]net
- d1mxvenloqrqmu[.]cloudfront[.]net
- dfrs12kz9qye2[.]cloudfront[.]net
- dgkytklfjrqkb[.]cloudfront[.]net
- dgkytklfjrqkb[.]cloudfront[.]net/main/trmz[.]exe
File Hashes
- FAB40A7BDE5250A6BC8644F4D6B9C28F
- 69FFDF99149D19BE7DC1C52F33AAA651
- B56D1D35D46630335E03AF9ADD84B488
- 8C61A6937963507DC87D8BF00385C0BC
- 7ADB7F56E81456F3B421C01AB19B1900
- 84DCB96BDD84389D4449F13EAC75098
- 2B307E28CE531157611825EB0854C15F
- 7B2868FAA915A7FC6E2D7CC5A965B1E
Mcafee users, please refer to Threat Intelligence Library for updated hashes as stated by their report.
Refer to IBM X-Force Exchange for YARA ruleset and more hashes.
The hashes and domains provided are by no means complete, but are rather samples.
Further Aliases, C&Cs, Hashes, and counter measures can be found here:
References:
http://blog.checkpoint.com/2017/06/01/fireball-chinese-malware-250-million-infection/