Thanks to Irongate Malware, Industrial Machines Now Have New Threat on the Horizon
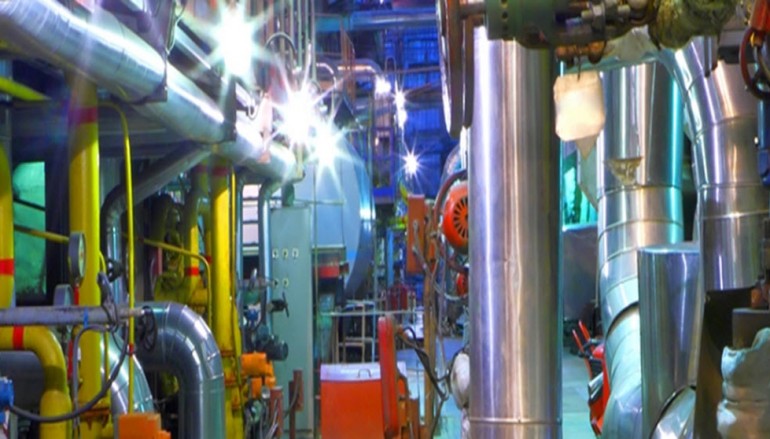
For any business that owns and relies on industrial machines, the cybersecurity landscape recently got a little more troubling thanks to the discovery of a new family of malware that is designed to wreak havoc on those devices.
Security experts at FireEye, a California-based network security company, discovered the malware in late 2015 and revealed its existence earlier this month. Dubbed “Irongate,” the malware’s sole purpose apparently is to manipulate a specific industrial control system (ICS)running within a simulated Siemens control system environment.
Irongate has the ability to alter control processes unbeknownst to those who are supposed to be operating and monitoring the industrial equipment. FireEye researchers believe Irongate is a “proof of concept” malware and haven’t yet seen instances of it on a real machine. However, the malware has the potential to alter files that control the temperature and pressure of specific Siemens control systems.
The researchers also say there are a few key similarities between Irongate and Stuxtnet, the piece of malware allegedly launched by the United States and Israel that disrupted the Iranian nuclear program by destroying centrifuges.
A Disruptive and Deceptive Threat
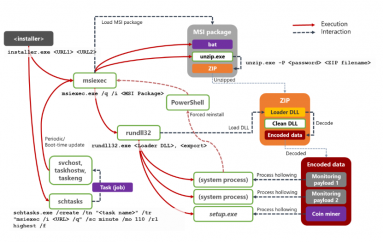
According to FireEye, Irongate’s key feature is a man-in-the-middle attack against process input-output and process operator software within industrial process simulations. The malware replaces Dynamic Link Library (DLL) files with a malicious DLL, which then acts as a broker between a programmable logic controller (PLC) and the legitimate monitoring software.
The malware then records five seconds of “normal” traffic from a PLC to the user interface and replays it, while sending different data back to the PLC. “This could allow an attacker to alter a controlled process unbeknownst to process operators,” FireEye says.
This is particularly troubling because those operating industrial machines could be fooled into thinking processes are normal while their machines are being disrupted. As IDG News Service reports: “Stuxnet did this by suspending the PLC operation so the reported centrifuge rotor speed would remain static and within normal limits while it actually was not. IRONGATE instead records valid data from the PLC and then continuously plays that data back— think of robbers feeding the same video recording to a surveillance camera in a loop.”
Irongate also evades “sandboxes” from firms like VMware or Cuckoo Sandbox, and will not run if it encounters those, in an effort to avoid detection and resist analysis. FireEye says that in “developing these anti-sandbox techniques indicates that the author wanted the code to resist casual analysis attempts” and also implies that the tool is malicious.
While Irongate “does not compare to Stuxnet in terms of complexity, ability to propagate, or geopolitical implications,” they share many similarities.
Both pieces of malware look for a single, highly specific process and replace DLLs to achieve process manipulation. Irongate detects environments that are hunting for malware, whereas Stuxnet looked for the presence of anti-virus software.
Security Implications for Businesses
The researchers say that Irongate’s characteristics “lead us to conclude that it is a test, proof of concept, or research activity.” According to ZDNet, the ProductCERT security team at Siemens says “Irongate does not work against operational control systems and does not exploit any known vulnerabilities to hijack industrial processes.”
FireEye says that even though companies that manage industrial machines and processes “face no increased risk from the currently identified members of the Irongate malware family,” the discovery offers “valuable insight into adversary mindset.”
Companies need to invest in network security monitoring and technologies that will indicate whether their industrial processes have been compromised, FireEye recommends.
Industrial control system operators should “require integrity checks and code signing for vendor- and user-generated code,” FireEye says, adding that without “cryptographic verification,” companies will be vulnerable to file replacement and man-in-the-middle attacks.
To guard against malware like Irongate, firms also need to develop ways to check the integrity of input-output data, such as independent sensing and backhaul. FireEye says companies also need to compare the data they actually see to the data they are expecting in their industrial processes, and not being aware of the expected state makes it easier for attackers to manipulate industrial machines without alarming their operators.
Source | BizTechMagazine