Snake Ransomware That Written in Golang Language Removes Backup Shadows Copies & Encrypt Windows Files
Researchers observed new snake ransomware that written in Golang targeting Windows users to encrypt the system files and remove the Volume Shadow Copies that the OS uses for backup.
Snake ransomware is a targeted campaign that contains a standard ransomware feature with some of the more complex functionalities.
Malware authors choose the Golang language which is used to write some of the most recent ransomware families and utilized by some of the RaaS (Ransomware as a Service) offerings since it is flexible for cross-platform and completely open-source programming language.
Researchers believe that the campaign has the potential to do serious and critical damage to an infected environment.
Snake ransomware targeting the specific platforms such as SCADA, enterprise management tools, system utilities and also some of the specific targeted applications include VMware Tools, Microsoft System Center Operations Manager, Nimbus, Honeywell HMIWeb, FLEXnet,
Once it infects the system, relevant files are overwritten with encrypted data, and the encrypted files extension is changed as ” EKANS”.
Also, modified files added with random characters which used to make it more difficult to identify the specific ransomware family.

Malware authors used both symmetric and asymmetric cryptography to encrypt the victim’s windows system files.
A symmetric key is required for encrypting and decrypting of files, In this case, symmetric key used to encrypt the victim’s files with attacker’s public key and the decryption process is only possible by having the attackers private key.
Since the attackers using key lengths (AES-256, RSA-2048), which makes it impossible to crack the key and decrypt the data.
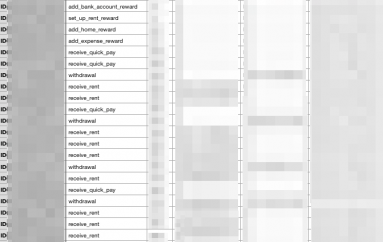
Snake ransomware also terminates the various system process of following.

According to SentinelOne research, “If the threat is executed with administrative privileges, the ransom note will be written to c:userspublicdesktopFix-Your-Files.txt. In the event that administrative privileges are not present, the ransom note will be written to an alternative location: c:users\AppDataLocalVirtualStore“
Once the Snake ransomware completes the infection process and encrypted the system files, it drops the ransomware notes that contain the details about how to decrypt the files.

Instead of providing the web address to obtain the payment, authors are instructed the victims to contact them via the email address in the ransom note is “bapcocrypt @ ctemplar.com” to get the decryption key from the attacker.
This post Snake Ransomware That Written in Golang Language Removes Backup Shadows Copies & Encrypt Windows Files originally appeared on GB Hackers.