QAKBOT RETURNS, LOCKING OUT ACTIVE DIRECTORY ACCOUNTS
QakBot, a worm-like strain of information-stealing malware that’s been around since 2009, has resurfaced again.
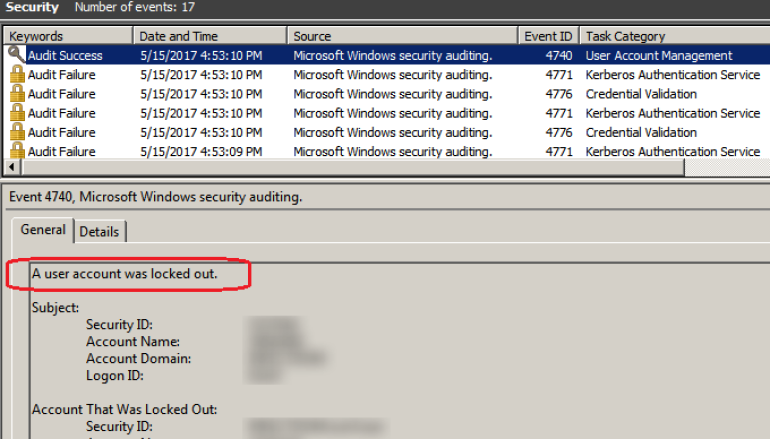
The malware has been a thorn in the side of administrators as of late. After a recent stretch of inactivity, researchers now link a rash of recent Microsoft Active Directory lockouts to QakBot.
Active Directory, Microsoft’s directory server, allows admins to control networks from a single location. Admins typically use the database to authenticate and authorize users.
The lockouts, which occurred last week, are a first for the malware and have left users unable to access endpoints, company servers and networked assets on affected domains, said Michael Oppenheim, Kevin Zuk, Matan Meir, and Limor Kessem, six researchers with IBM’s X-Force Research team, on Friday.
The latest iteration of the malware has been spreading through endpoints via a dropper that waits 10 to 15 minutes to execute in hopes of evading detection from sandboxes or anti-virus systems. The dropper opens an executable, injects a .DLL, and overwrites the original file. From there the dropper downloads the QakBot’s payload.
The malware has exhibited worm-like tendencies in the past, such as being able to self-replicate via shared drives and removable media. This time around QakBot has been spreading through networks – and ultimately locking users out of their accounts – by cycling through user and domain credentials. The malware pairs logins with different password guessing schemes, including one that guesses passwords by using words in the dictionary.
Source : threatpost





