Experts Devised Advanced SMS Phishing Attacks Against Modern Android-based Phones
Experts warn of advanced phishing attacks in certain modern Android-based phones that can trick users into accepting new malicious phone settings.
When users insert a new SIM in their mobile phone and access to the cellular network for the first time, the carrier service automatically configures or sends you a message containing settings for the connection to data services.
Researchers from Check Point have discovered that advanced phishing attacks in certain modern Android-based phones, could allow an attacker to trick users into accepting new device settings that could expose them to various attacks, including traffic hijacking.
The issue affects several modern Android-based phones, including devices manufactured by Samsung, Huawei, LG and Sony. In these attacks, a remote agent can trick users into accepting new phone settings that, for example, route all their Internet traffic through a proxy controlled by the attacker. The attack technique leverages on the over-the-air (OTA) provisioning process used to remotely provide network-specific settings to the phones.
“Check Point Researchers have identified a susceptibility to advanced phishing attacks in certain modern Android-based phones, including models by Samsung, Huawei, LG and Sony. In these attacks, a remote agent can trick users into accepting new phone settings that, for example, route all their Internet traffic through a proxy controlled by the attacker.” reads the analysis published by CheckPoint.
“This attack vector relies on a process called over-the-air (OTA) provisioning, which is normally used by cellular network operators to deploy network-specific settings to a new phone joining their network. However, as we show, anyone can send OTA provisioning messages.”
The experts pointed out that the industry standard for OTA provisioning, Open Mobile Alliance Client Provisioning (OMA CP) implements limited authentication methods. This means that the protocol doesn’t allow a recipient to verify the origin of the provisioning setting messages.
Checkpoint discovered that phones manufactured by major vendors, including Samsung, Huawei, LG and Sony (more than 50% of all Android devices on the market) implement a weak authentication for Mobile carriers send OMA CP (Open Mobile Alliance Client Provisioning) sent by the carriers.
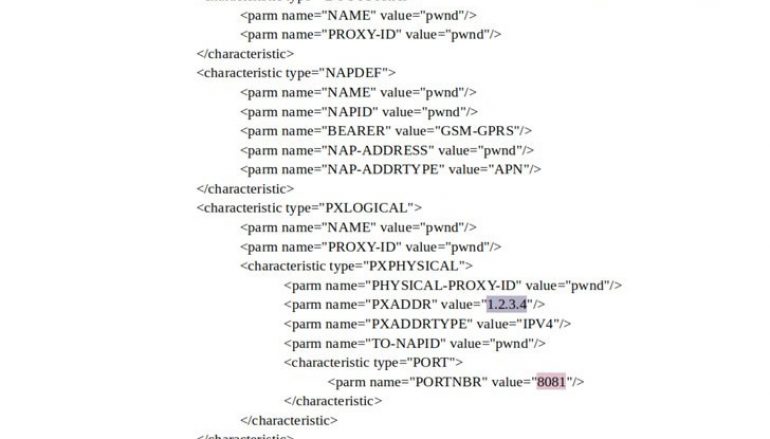
The Mobile carriers send OMA CP messages to the devices that contain APN settings, which your phone needs to set up a connection to the gateway between your carrier’s mobile network and the public Internet.
An Access Point Name (APN) is the name of a gateway between a GSM, GPRS, 3G or 4G mobile network and another computer network, frequently the public Internet. A mobile device making a data connection must be configured with an APN to present to the carrier.
The settings also include an optional HTTP proxy that can be set by an attacker to route web traffic through it.
The attack devised by the Checkpoint researcher can allow remote hackers to trick users into updating the APN settings of their devices with proxy servers under the attackers’ control.
The proxy could allow the attacker to intercept network connections a targeted device makes through its data carrier service, such as including web browsers and built-in email clients.
To carry out the attack, hackers need to send OMA CP messages. Attackers need to send the binary SMS messages using a GSM modem (either a $10 USB dongle, or phone operating in modem mode), and a simple script or off-the-shelf software that allows it to create the OMA CP.

OMA CP could be used to change one of the following settings over-the-air:
- MMS message server
- Proxy address
- Browser homepage and bookmarks
- Mail server
- Directory servers for synchronizing contacts and calendar
The experts provided the following attack scenarios in which attackers attempt to trick victims into setting up a proxy under their control.
Unauthenticated (Samsung)
If the victims use Samsung phones, the attacker can simply send them unauthenticated OMA CP messages, specifying the proxy that he controls. This is possible because there it isn’t implemented any authenticity check.
Authenticated with IMSI for Huawei, LG or Sony devices
If the attacker is able to obtain the International Mobile Subscriber Identity (IMSI) numbers of a target Huawei, LG or Sony phones, he can carry out a phishing attack
OMA CP messages include and an optional security header that could enable validation of the CP’s authenticity with the recipient’s IMSI number. In this case, Huawei, LG and Sony phones allow the installation of malicious settings.
Authenticated with PIN
For those potential victims whose IMSI could not be obtained, the attacker can send each victim two messages. A text message that purports to be from the victim’s network operator, asking him to accept a PIN-protected OMA CP, and specifying the PIN as an arbitrary four-digit number. Then, the attacker sends him an OMA CP message authenticated with the same PIN. This trick will allow installing the settings.
The attacker can send out targeted phishing CP messages (i.e. preceded with a custom text message tailored to deceive a particular recipient) send out them in bulk.
However, the researchers explained that proxy settings for mobile data network are not used by every app installed a targeted device.
The experts pointed out that this technique would not be effective to decrypt HTTPS connections.
Researchers shared their findings with the affected vendors in March 2019. Samsung and LG have addressed the issue in their Security Maintenance Release for May and July respectively.
Huawei is planning will address the issue in the next generation of Mate series or P series smartphones. Bad news for Sony users, the vendor did not acknowledge the issue cause their mobile phone devices are compliance with the OMA CP specification.
“We described an advanced phishing attack flow against modern Android-based phones. This attack flow enables anyone who has a cheap USB modem to trick users into installing malicious settings onto their phones. To target some of the susceptible phones, the attacker needs to know the victims’ IMSI numbers, which can be obtained via an Android application having READ_PHONE_STATE permission.” concludes the report.
“We verified our proof of concept on the Huawei P10, LG G6, Sony Xperia XZ Premium, and a range of Samsung Galaxy phones, including S9.”
This post Experts Devised Advanced SMS Phishing Attacks Against Modern Android-based Phones originally appeared on Security Affairs.