Collection #1 Data Breach Analysis – Part 2
The cyber security expert Marco Ramilli continues its analysis of the data leak known as Collection #1, he shared some interesting views on data
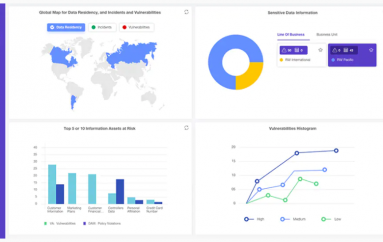
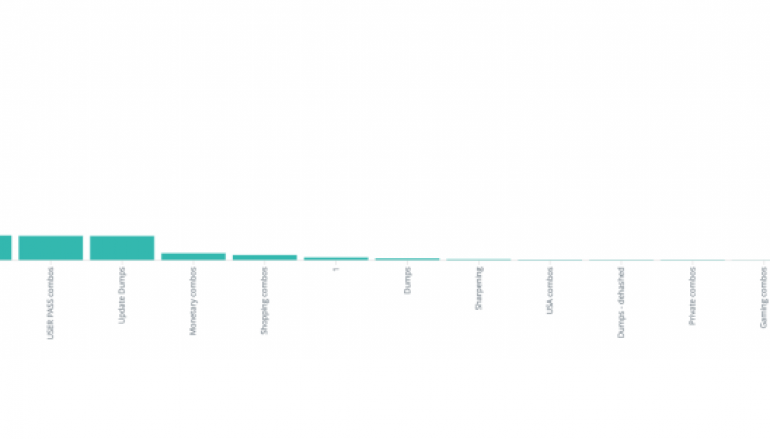
On January 19th we downloaded Collection #1 to make statistics on its content (you might find more information here). During these days we finished the two main activities to be able to answer some more questions about its data: (i) ELK import and (ii) building of simple views to visualise desired information. The following image shows a final general importing view mostly focused on Collection#1 interesting folders (as described on Part1). In this post, I’d like to give my second personal overview without getting into details such as: private domains, government domains, domains belonging to municipalities and so on. A professional report (and not a personal blog post) on that topic might be available in few days in a special session.

It is interesting to compare the differences between Part 1 and Part 2, since the panorama of the most leaked email’ domain names changed quite a bit. Yahoo, Mail.ru, and Hotmail follow Gmail, which stands on top of the raking list. If you remember the same graph in Part1 you might appreciate a nice difference in ranking list where yahoo, gmail, aol and hotmail were leading the pics.

While there are a lot of unique entries (unique emails), there are several emails leaked multiple times. Testing emails such as: sample@email.tst, 123@mail.ru and 1@gmail.com as well as 123@yandex.ru, email@email.com and nogood87@yahoo.com and private emails belonging to gmail are the most leaked ones. It was also possibile to see multiple credentials (same email and password) within multiple file entries which highlights an insane reuse of credentials.

Focusing on the most recent folders: “NEW combo semi private” and “MAIL ACCESS combos” and assuming the folder name is explicit, we might observe most of the “recent combos” (please see Part1) belong to EU and RU.

Further data and conclusions are available in the blog post published by Marco Ramilli, founder and CEO Yoroi, in his blog.
https://marcoramilli.com/2019/01/26/collection-i-data-breach-analysis-part-2/
This post Collection #1 Data Breach Analysis – Part 2 originally appeared on Security Affairs.