Posts From CCME
Wawa Stores Plagued by Malware Since March
Payment processing systems at Wawa, the American chain of convenience and fuel stores, have been harboring malware that steals credit card information for nine months. In an open letter published online yesterday, Wawa CEO Chris Gheysens announced that the malware
A malicious email campaign that exploits the notoriety of youthful Swedish climate crisis activist Greta Thunberg has been discovered by multiple research teams. Threat actors constructed an email that appears to invite the recipient to participate in a demonstration being
New research into the attitudes and beliefs of cybersecurity professionals has identified a sharp rise in the number of businesses paying up when stung by a ransomware attack. The 2019 Global Security Attitude Survey Report by California cybersecurity technology company
Hackers abuse legitimate RDP service to use fileless attack techniques for dropping multi-purpose off-the-shelf tools for device fingerprinting and to deploy malicious payloads ranging from ransomware to cryptocurrency miners. The Remote Desktop is the built-in feature with most of the
Data Leak Exposes 267 Million Facebook Users
A database of 267 million Facebook user IDs, phone numbers, and names was left exposed online for a fortnight thanks to another cloud misconfiguration, according to researchers. The trove was likely to have been the result of an illegal scraping
UK Police in the Dock as Device Losses Soar 150%
UK police officers and staff reported on average four lost or stolen devices every day over the most recent financial year, according to newly released data. Think tank Parliament Street received Freedom of Information (FOI) requests from 22 forces across
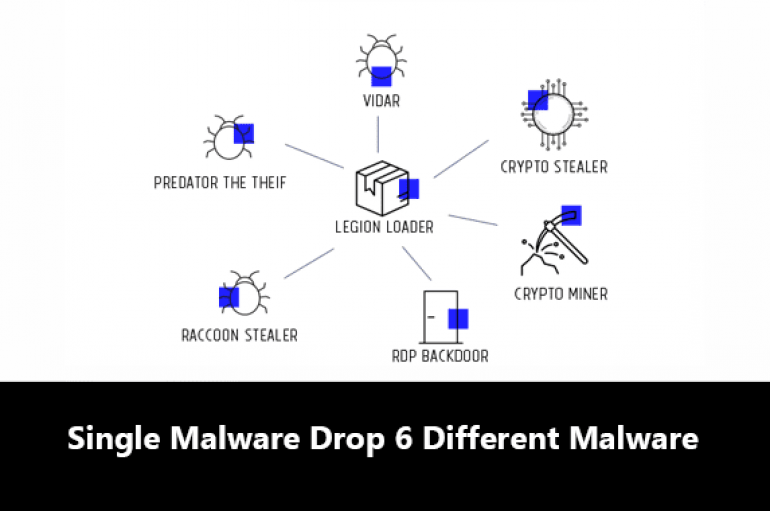
Dropper-for-Hire – Hackers Using a Single Malware to Drop 6 Different Malware in Targeted Systems
Researchers observed a new malware campaign under a dropper-for-hire method that drops 6 different malware to attack the targeted victims and perform a variety of malicious activities. Nowadays malware authors collaborative with other threat actors to develop sophisticated malware become
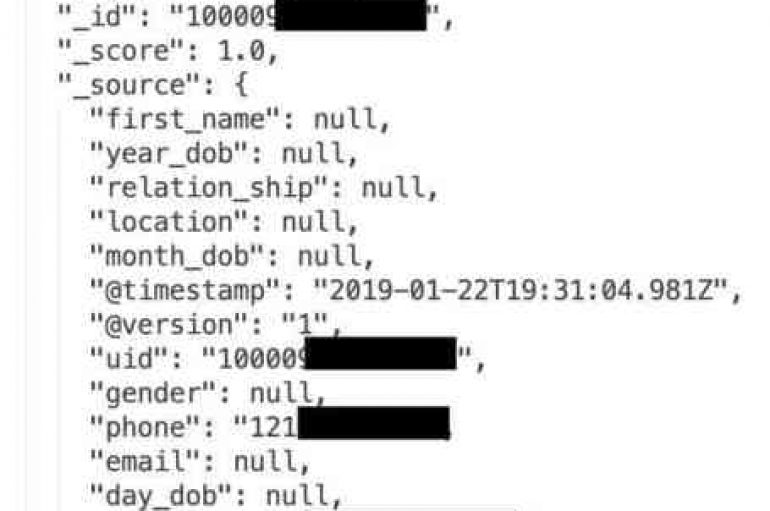
Security researcher Bob Diachenko discovered more than 267 million Facebook user IDs, phone numbers and names in an unsecured database. Security expert Bob Diachenko, along with Comparitech, has discovered more than 267 million Facebook user IDs, phone numbers and names
Australia’s Deakin University is to launch the country’s first cybersecurity course accredited by the Australia Computer Society (ACS). The ACS is the only body in Australia with the power to accredit IT and ICT courses. Only recently did it add
New research into litigation trends has identified cybersecurity as a major new source of legal disputes in the United States. The 2019 Litigation Trends Annual Survey conducted by global law firm Norton Rose Fulbright questioned corporate counsel about dispute-related issues
How to Fight with Ransomware Attack? Should You or Shouldn’t You Pay a Hacker’s Ransomware Demand?
Ransomware attacks are targeting educational institutions, hospitals, as well as local governments. The number of incidents has more than doubled in 2019. Cybercriminals deploy crushing new types of malicious software and additional attack techniques. The point is that they are
Honda Leak Hits 26,000 North American Customers
Honda has become the latest big-name brand to expose the personal information of countless customers because of a cloud misconfiguration. The carmaker’s North America business leaked around 26,000 unique customer records thanks to an unsecured Elasticsearch cluster, according to security
The FBI has issued a warning to holiday travelers not to use public Wi-Fi on the road this Christmas because of cybersecurity concerns. As internet users cross countries and continents to be with friends and family over the holiday period,
Hackers Using Remote Desktop Application To Install “Zeppelin” Ransomware & Encrypt Windows Files
Cybercriminals abusing a Remote Desktop application ConnectWise Control that previously known as (ScreenConnect) to deliver the Zeppelin Ransowmare (aka Vega) and encrypt the victim’s files in Windows PC. ConnectWise is a remote desktop software mostly used in the enterprise network
Unknown Hacking Group Launching Custom Malware “Dudell” via Weaponized Microsoft Excel Documents
Researchers discovered a new wave of custom malware campaign named as “Dudell” from previous unknown cyberespionage group dubbed Rancor. Rancor Threat group active since 2017, and they continuously targeting the government organization until January 2019, in this current campaign, researchers
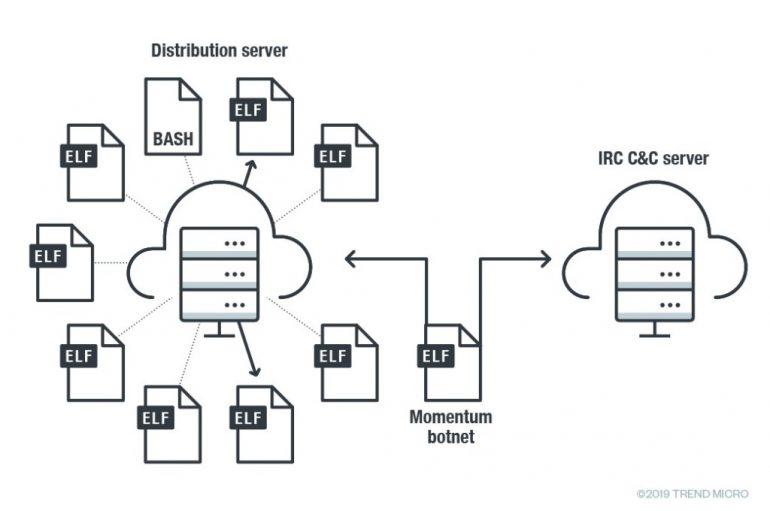
Security experts recently found notable malware activity affecting devices running Linux that is associated with the Momentum Botnet. Malware researchers from Trend Micro recently observed notable malware activity affecting devices running Linux that is associated with the Momentum Botnet. Experts