Archive
A European fashion retailer has become the latest big-name brand to expose personal data on millions of its customers after misconfiguring a cloud database. Researchers at vpnMentor discovered the unencrypted Elasticsearch server on June 28 and parent company BrandBQ finally
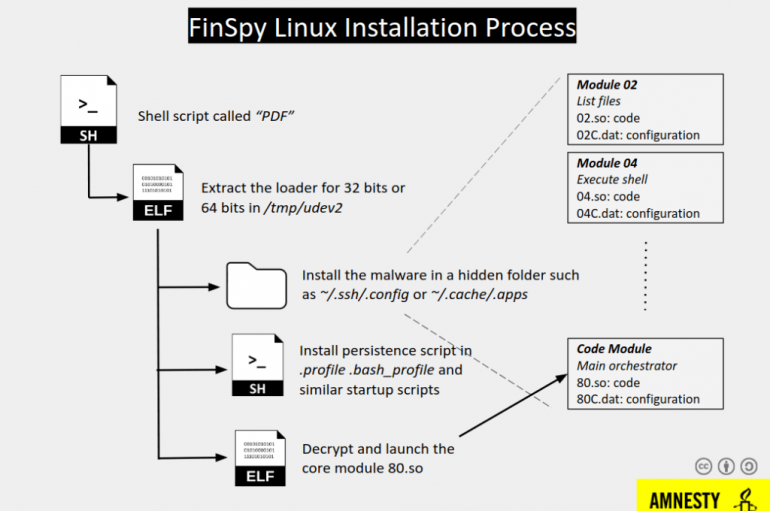
Experts from Amnesty International uncovered a surveillance campaign that targeted Egyptian civil society organizations with a new version of FinSpy spyware. Amnesty International uncovered a new surveillance campaign that targeted Egyptian civil society organizations with previously undisclosed versions of the
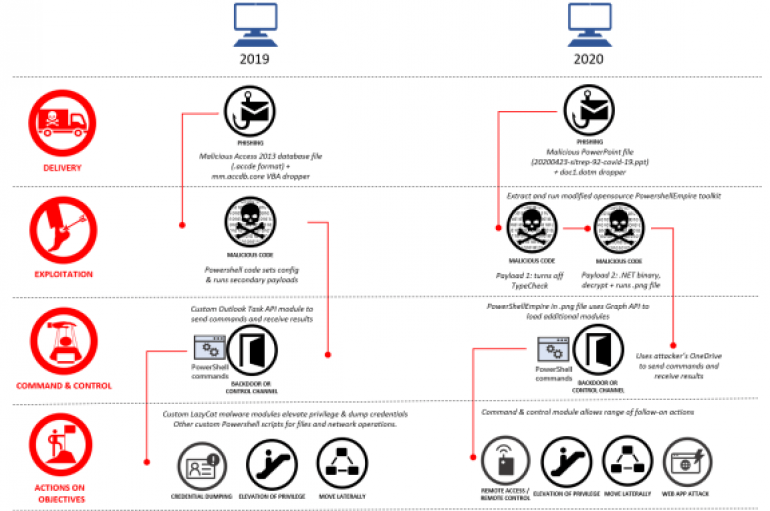
Microsoft removed 18 Azure Active Directory applications from its Azure portal that were created by a Chinese-linked APT group Gadolinium. Microsoft announced this week to have removed 18 Azure Active Directory applications from its Azure portal that were created by
Texas Software Provider Reports Cyber-attack
A cyber-attack has struck a Texas company that provides software services to schools and state and local governments across the United States. Tyler Technologies notified customers on September 23 that its phone and computer systems had been compromised by a
US Federal Agency Compromised by Cyber-Actor
A warning has been issued by America’s Cybersecurity and Infrastructure Security Agency (CISA) after a malicious cyber-actor compromised a United States federal agency. The attacker used valid log-in credentials for multiple users’ Microsoft Office 365 accounts and domain administrator accounts
According to SAM Seamless Network, over 200,000 businesses are using Fortigate VPN with default settings, exposing them to the risk of a hack. In response to the spreading of Coronavirus across the world, many organizations deployed VPN solutions, including Fortigate
Cyber-criminals stole more than GBP4m from elderly people in the UK in the financial year 2018-19, data received by the charity Age UK has revealed. A freedom of information (FOI) request submitted by the charity to the UK’s national fraud
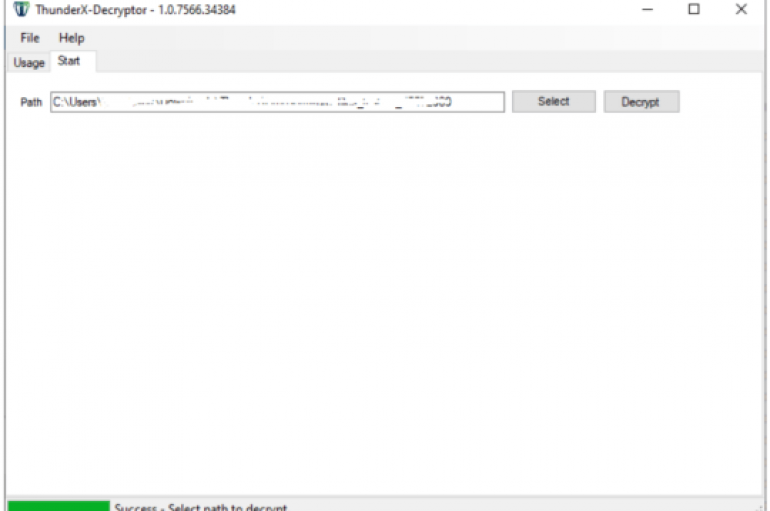
Good news for the victims of the ThunderX ransomware, cybersecurity firm Tesorion has released a decryptor to recover their files for free. Cybersecurity firm Tesorion has released a free decryptor for the ThunderX ransomware that allows victims to recover their
Facebook has been forced to remove over 150 fake accounts tied to Beijing’s efforts to influence public opinion in south-east Asia. The social media giant describes influence operations like this as “coordinated inauthentic behavior” (CIB), as those behind them use
#COVID19 Pushes More Fraud Online
Fraudsters are increasingly moving online to cash-in on the COVID-19 pandemic, although overall unauthorized fraud losses dropped in the first half of 2020, according to UK Finance. The banking industry body’s 2020 Half Year Fraud Update revealed some promising headline
Microsoft has warned that a critical vulnerability it patched in August is now being actively exploited in the wild, enabling attackers to remotely control a target organization’s Windows domain. Also known as “Zerologon,” CVE-2020-1472 is a critical elevation of privilege
The way cybersecurity awareness training is conducted in organizations has a huge bearing on employees’ subsequent security outlook and behaviors, according to a new report from Osterman Research. The researchers discovered that users who found security training “very interesting” were
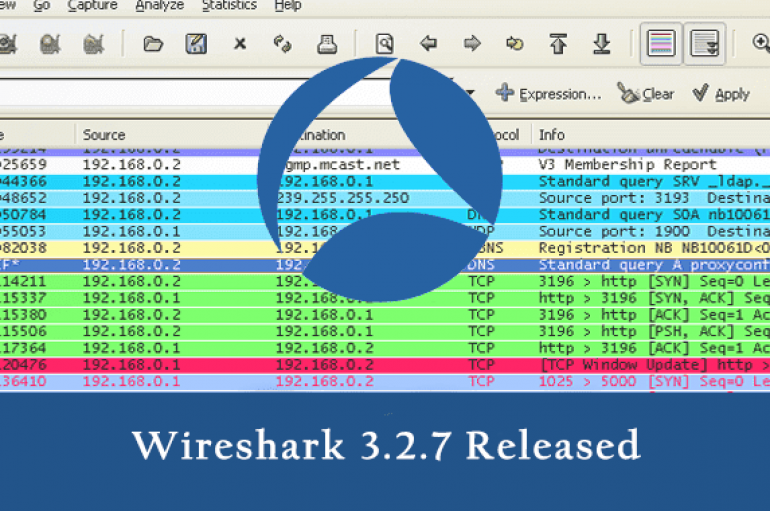
Wireshark 3.2.7 was released with a fix for security vulnerabilities and an updated version of Npcap & Qt. Wireshark is known as the world’s most popular network protocol analyzer. It is used for troubleshooting, analysis, development, and education. It is
5G also called the fifth generation of wireless cellular networks, will offer new opportunities to all walks of life, including health, supply chain, agriculture, etc. Similarly, emerging technologies such as IoT (Internet of Things), Artificial Intelligence (AI), and others will
Attacks Against Oil and Gas Industry on the Rise
New research published today by Kaspersky examines a rise in the number of cyber-attacks on industrial control system (ICS) computers used by the oil and gas industry. Over the first six months of 2020, the percentage of systems attacked in
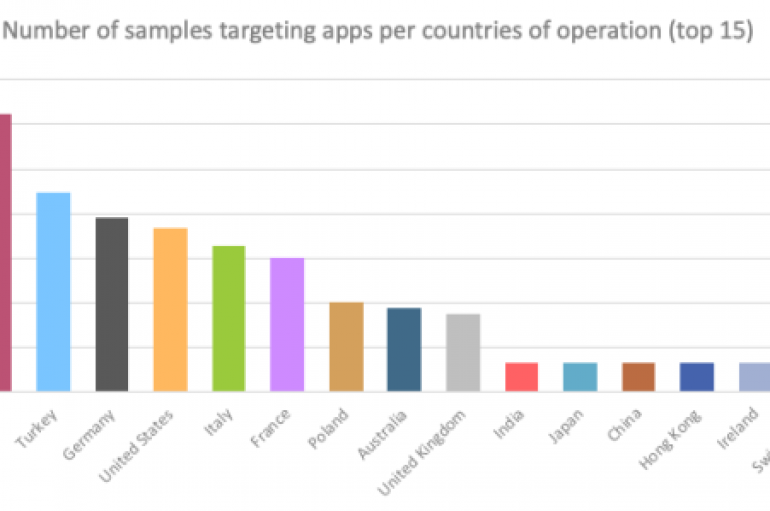
Security researchers spotted a new strain of Android malware, dubbed Alien, that implements multiple features allowing it to steal credentials from 226 apps. Researchers from ThreatFabric have discovered and analyzed a new strain of Android malware, tracked as Alien, that