Researcher Grabs VPN Password With Tool From NSA Dump
Cisco has already warned customers about two exploits found in the NSA-linked data recently dumped by hackers calling themselves The Shadow Brokers. Now, researchers have uncovered another attack included in the cache, which they claim allows the extraction of VPN passwords from certain Cisco products—meaning hackers could snoop on encrypted traffic.
Security researcher Mustafa Al-Bassam first documented the hacking tool, which uses the codename BENIGNCERTAIN, in a blog post published Thursday. He coined the attack “PixPocket” after the hardware the tool targets: Cisco PIX, a popular, albeit now outdated, firewall and VPN appliance. Corporations or government departments might use these devices to allow only authorised users onto their network.
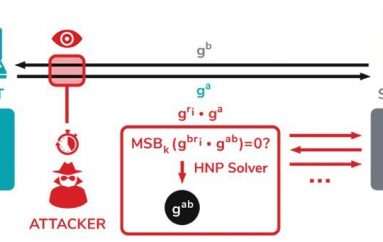
Based on his analysis of the code, Al-Bassam writes that the tool works by sending a packet to the target machine that makes it dump some of its memory. Included in that dump is the VPN’s authentication password, which is used to log into the device.
“With access to the preshared key, they could decrypt any traffic”
Brian Waters, another security researcher, tested BENIGNCERTAIN on his own hardware and managed to obtain the VPN’s password, also known as a preshared key.
“I was able to pop out a VPN password from the ‘outside’ interface. Meaning the one that would be connected to the internet,” Waters told Motherboard in a Twitter message.
“To me this is verified,” Al-Bassam told Motherboard in an online chat.
“It’s proof that in a VPN that uses authentication with preshared keys, the NSA could have remotely sent a packet to that VPN from an outside Internet IP (unlike the other exploits which require internal access), and grabbed the preshared key […] With access to the preshared key, they could decrypt any traffic,” he added. Once they’ve accessed the network, an attacker might then be able to snoop on a target organisation’s traffic and spy on its users.
According to Al-Bassam, the tool references PIX versions 5.2(9) up to 6.3(4). However, Brian Waters said he carried out his test on hardware running the 6.3(5) version, implying that the attack may work on other versions of PIX than those listed in the tool’s code.
Both Al-Bassam and Maksym Zaitsev, another researcher who has been looking into BENIGNCERTAIN, believe that the attack is likely capable of extracting private encryption keys from VPNs as well, which is another, more robust way of authenticating access. Waters was unable to test that however.
Source | motherboard